In today's interconnected world, the Internet of Things (IoT) continues to revolutionize the way we interact with technology. At the heart of this transformation lies the SSH IoT platform free solutions, providing users with secure and cost-effective methods to manage their IoT devices. Whether you're a tech enthusiast, a small business owner, or a hobbyist, understanding the potential of SSH IoT platforms can significantly enhance your ability to control and monitor IoT devices efficiently.
As IoT adoption grows exponentially, the need for secure and reliable connectivity solutions becomes paramount. SSH IoT platform free options offer a viable alternative for those looking to harness the power of IoT without breaking the bank. By leveraging the robust security features of SSH, users can protect their devices from unauthorized access while maintaining seamless communication.
Within this comprehensive guide, we will explore the intricacies of SSH IoT platform free solutions, covering everything from the basics to advanced configurations. We will delve into the benefits, potential use cases, and how to implement SSH securely within an IoT ecosystem. Let's dive in and discover how SSH IoT platforms can transform your digital landscape.
Read also:How Old Is Jideon Unveiling The Age And Life Of A Rising Star
Table of Contents
- What is SSH?
- Understanding IoT Platforms
- The SSH IoT Platform Combination
- Benefits of SSH IoT Platform Free
- Security Features of SSH
- Real-World Use Cases
- How to Set Up SSH IoT Platform Free
- Essential Tools for SSH IoT Platforms
- Limitations and Challenges
- The Future of SSH IoT Platforms
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol designed to provide secure communication over an unsecured network. Initially developed in 1995, SSH has become a cornerstone for secure data transfer and remote command execution. It ensures that data exchanged between devices remains encrypted, safeguarding it from potential eavesdropping and tampering.
The protocol operates on a client-server model, where a user (client) connects to a remote server using SSH. Once connected, users can execute commands, transfer files, and manage systems securely. This functionality makes SSH an ideal choice for managing IoT devices, where security and reliability are critical.
Key Features of SSH
- Data Encryption: SSH encrypts all data transmitted between devices, ensuring confidentiality.
- Authentication: SSH supports multiple authentication methods, including password-based and public-key authentication.
- Integrity: The protocol ensures data integrity by verifying that transmitted data has not been altered.
Understanding IoT Platforms
The Internet of Things (IoT) refers to a network of interconnected devices capable of exchanging data without requiring human intervention. IoT platforms serve as the backbone of these networks, providing the infrastructure needed to manage and monitor devices effectively. These platforms offer various features, including data collection, device management, analytics, and integration capabilities.
As IoT adoption increases, so does the demand for platforms that offer robust security and scalability. SSH IoT platform free solutions address these needs by providing secure communication channels while maintaining cost-effectiveness.
Components of IoT Platforms
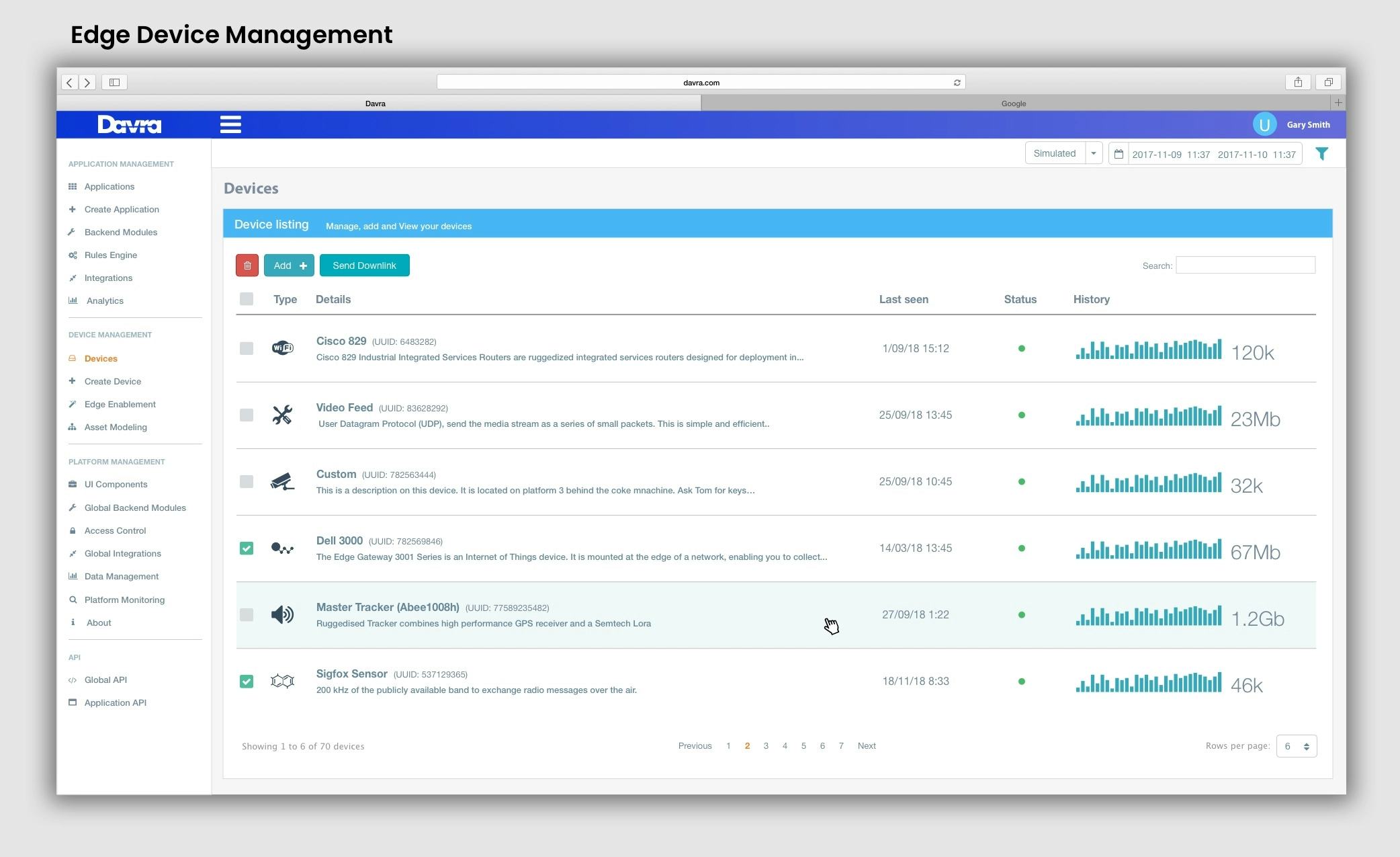
- Device Management: Tools for configuring, monitoring, and updating IoT devices.
- Data Analytics: Features for processing and analyzing data collected from devices.
- Integration: Capabilities to connect with third-party applications and services.
The SSH IoT Platform Combination
Combining SSH with IoT platforms creates a powerful synergy that enhances security and functionality. By leveraging SSH's encryption and authentication capabilities, IoT platforms can ensure that data transmitted between devices remains secure and tamper-proof. This combination is particularly beneficial for free SSH IoT platform solutions, where users can enjoy secure connectivity without incurring additional costs.
SSH IoT platform free solutions are ideal for small-scale IoT deployments, hobbyists, and educational purposes. They provide users with the tools needed to manage IoT devices securely while maintaining flexibility and scalability.
Read also:Andrea Agnelli Net Worth A Deep Dive Into The Juventus Chairmans Wealth And Influence
Why Choose SSH for IoT?
- Strong Encryption: SSH offers robust encryption protocols that protect data from unauthorized access.
- Public Key Infrastructure: The use of public-key cryptography ensures secure authentication.
- Cost-Effective: Free SSH IoT platforms provide a budget-friendly option for securing IoT devices.
Benefits of SSH IoT Platform Free
Adopting SSH IoT platform free solutions offers numerous advantages, making it an attractive option for individuals and organizations looking to secure their IoT ecosystems. Below are some of the key benefits:
- Enhanced Security: SSH's encryption and authentication features protect IoT devices from cyber threats.
- Scalability: Free SSH IoT platforms can scale to accommodate growing IoT deployments.
- Cost-Effectiveness: By eliminating licensing fees, users can secure their IoT devices without incurring additional costs.
These benefits make SSH IoT platform free solutions an ideal choice for those seeking secure and flexible IoT management options.
Security Features of SSH
SSH provides a comprehensive suite of security features that make it an excellent choice for securing IoT platforms. These features include:
- Data Encryption: SSH encrypts all data transmitted between devices, ensuring confidentiality.
- Public-Key Authentication: This method allows users to authenticate securely without relying on passwords.
- Integrity Verification: SSH ensures data integrity by verifying that transmitted data has not been altered.
By incorporating these security features into IoT platforms, users can protect their devices from unauthorized access and potential cyberattacks.
Best Practices for SSH Security
- Use Strong Passwords: Ensure that all SSH accounts have strong, complex passwords.
- Enable Public-Key Authentication: This method provides a more secure alternative to password-based authentication.
- Regularly Update SSH: Keep your SSH software up to date to protect against vulnerabilities.
Real-World Use Cases
SSH IoT platform free solutions find applications in various industries, addressing specific needs and challenges. Below are some real-world use cases:
Smart Home Automation
Homeowners can use SSH IoT platforms to securely manage smart home devices, such as lighting, thermostats, and security systems. By leveraging SSH's encryption and authentication capabilities, users can protect their devices from unauthorized access while maintaining remote control.
Industrial IoT
In the industrial sector, SSH IoT platforms help secure critical infrastructure, such as manufacturing equipment and energy grids. By ensuring secure communication between devices, SSH helps prevent costly downtime and potential security breaches.
How to Set Up SSH IoT Platform Free
Setting up an SSH IoT platform free solution involves several steps, including installing the necessary software, configuring devices, and securing the network. Below is a step-by-step guide:
Step 1: Install SSH Server
Begin by installing an SSH server on your IoT devices. Popular options include OpenSSH and Dropbear. These servers provide the foundation for secure communication between devices.
Step 2: Configure Devices
Once the SSH server is installed, configure your IoT devices to connect to the server. This process typically involves setting up usernames, passwords, and public-key authentication.
Step 3: Secure the Network
Implement best practices for SSH security, such as enabling public-key authentication, disabling password-based authentication, and regularly updating the SSH software.
Essential Tools for SSH IoT Platforms
To maximize the potential of SSH IoT platform free solutions, users can leverage various tools and resources. Some essential tools include:
- SSH Clients: Software applications that allow users to connect to SSH servers, such as PuTTY and OpenSSH.
- Network Monitoring Tools: Solutions for monitoring network activity and detecting potential security threats.
- Device Management Platforms: Tools for configuring, monitoring, and updating IoT devices.
Limitations and Challenges
While SSH IoT platform free solutions offer numerous benefits, they also come with certain limitations and challenges. These include:
- Resource Constraints: Free SSH IoT platforms may lack advanced features found in commercial solutions.
- Technical Expertise: Users may require technical knowledge to configure and manage SSH effectively.
- Compatibility Issues: Not all IoT devices may be compatible with SSH, limiting its application in certain scenarios.
Addressing these limitations requires careful planning and consideration of the specific needs and constraints of your IoT deployment.
The Future of SSH IoT Platforms
As IoT continues to evolve, the role of SSH IoT platforms will become increasingly important. Advances in encryption technologies, authentication methods, and network protocols will further enhance the security and functionality of these platforms. Additionally, the growing demand for secure and cost-effective IoT solutions will drive innovation in the SSH IoT space.
Looking ahead, SSH IoT platform free solutions will play a crucial role in shaping the future of IoT, enabling users to secure their devices while maintaining flexibility and scalability.
Emerging Trends in SSH IoT
- Quantum-Resistant Encryption: As quantum computing becomes a reality, SSH IoT platforms will need to adopt encryption methods resistant to quantum attacks.
- AI-Driven Security: Artificial intelligence will enhance SSH's ability to detect and respond to potential security threats.
- Edge Computing Integration: SSH IoT platforms will increasingly integrate with edge computing technologies to improve performance and reduce latency.
Kesimpulan
SSH IoT platform free solutions offer a powerful and cost-effective way to secure IoT devices while maintaining flexibility and scalability. By leveraging SSH's encryption and authentication capabilities, users can protect their devices from unauthorized access and potential cyber threats. Understanding the benefits, limitations, and future trends of SSH IoT platforms is essential for anyone looking to harness the full potential of IoT technology.
We invite you to explore further resources and share your thoughts in the comments below. For more insights into SSH IoT platforms and other cutting-edge technologies, check out our other articles and stay updated on the latest developments in the world of IoT.