In today's interconnected world, IoT SSH login free services have become an essential tool for managing and accessing remote devices securely. As more organizations and individuals embrace the Internet of Things (IoT), the need for secure and reliable remote access solutions has never been greater. IoT SSH login free platforms offer a cost-effective way to connect to devices without compromising on security.
With the rapid expansion of IoT devices, managing them remotely has become both a necessity and a challenge. Traditional methods often fall short in providing the level of security and flexibility required for modern IoT ecosystems. This is where SSH (Secure Shell) comes into play, offering encrypted communication channels that protect sensitive data and device integrity.
This comprehensive guide will explore the concept of IoT SSH login free services, their benefits, implementation strategies, and best practices. Whether you're a tech enthusiast, a developer, or a business owner, this article will provide valuable insights into leveraging SSH for secure IoT device management.
Read also:Jimmy Butler And Rachel Nichols A Look Into Their Professional Relationship And Impact On Sports Journalism
Table of Contents
- What is SSH?
- Benefits of IoT SSH Login Free
- How to Set Up IoT SSH Login
- Security Considerations for IoT SSH
- Common Use Cases for IoT SSH
- Best Practices for IoT SSH
- Tools and Software for IoT SSH
- Troubleshooting IoT SSH Issues
- Future Trends in IoT SSH
- Conclusion
What is SSH?
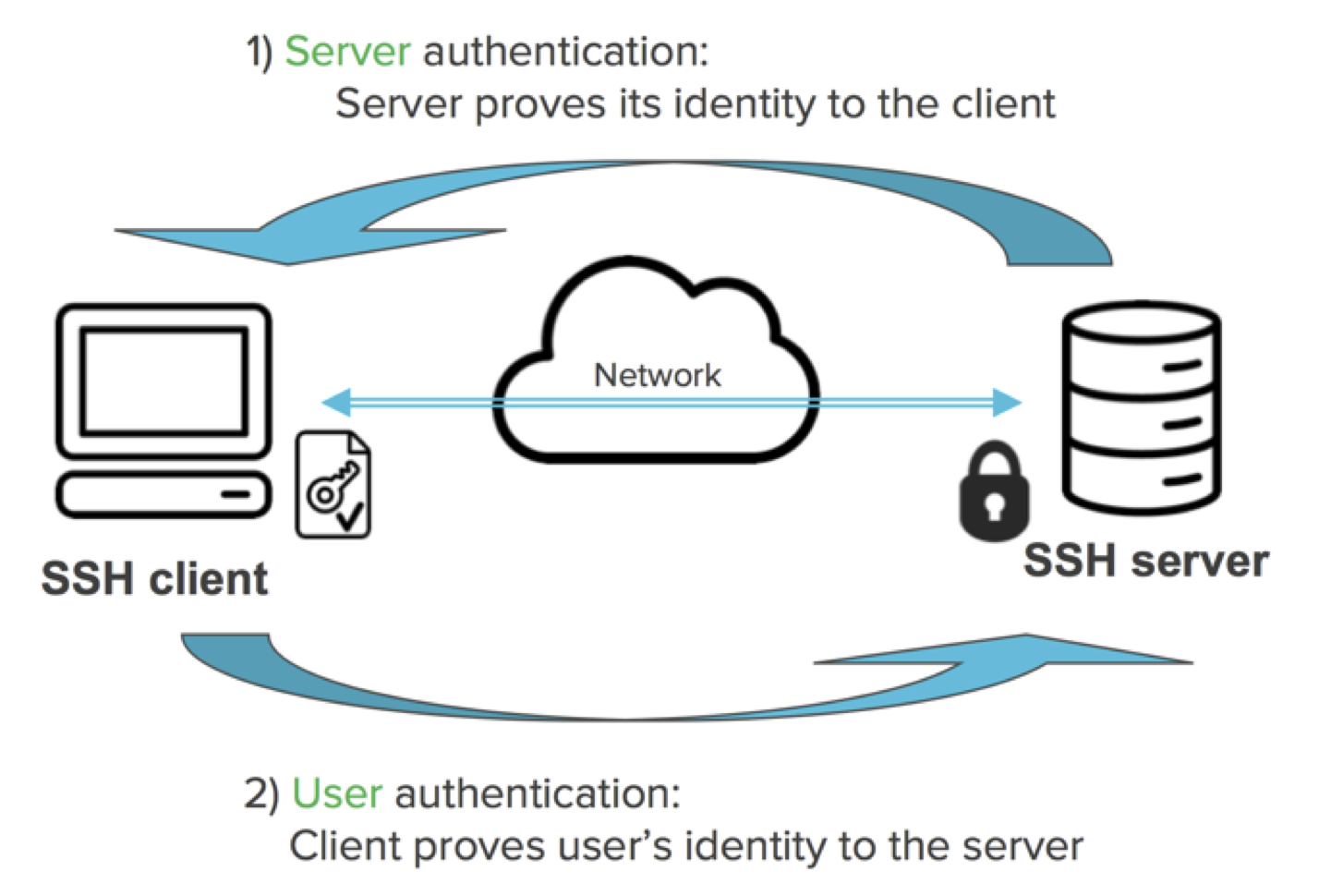
SSH, or Secure Shell, is a network protocol that provides secure communication between two computers over an unsecured network. Originally developed in 1995, SSH has become a standard tool for remote server management and secure file transfers. The protocol encrypts all data exchanged between the client and server, ensuring confidentiality, integrity, and authentication.
For IoT devices, SSH offers a reliable way to access and manage systems remotely. With the rise of IoT SSH login free platforms, users can now leverage this powerful protocol without incurring additional costs. This section will delve deeper into how SSH works and its role in modern IoT ecosystems.
Key Features of SSH
- Encryption: SSH uses strong encryption algorithms to protect data in transit.
- Authentication: It supports various authentication methods, including passwords and public key cryptography.
- Command Execution: Users can execute commands on remote devices securely.
Benefits of IoT SSH Login Free
IoT SSH login free services offer several advantages for both individuals and organizations. By eliminating the need for paid subscriptions, these platforms make secure remote access more accessible to a broader audience. Below are some of the key benefits:
Cost Efficiency
One of the most significant advantages of IoT SSH login free platforms is their cost-effectiveness. Users can manage and monitor IoT devices without incurring additional expenses for proprietary software or licensing fees. This makes it an ideal solution for startups, small businesses, and hobbyists.
Enhanced Security
SSH provides robust security features that protect IoT devices from unauthorized access and cyber threats. By leveraging encryption and secure authentication methods, users can ensure the integrity and confidentiality of their data.
Flexibility
IoT SSH login free services support a wide range of devices and operating systems, making them highly versatile. Whether you're managing a smart home system or an industrial IoT network, SSH offers the flexibility needed to adapt to various use cases.
Read also:Discover The Ultimate Fun At Cascade Bay Water Park Your Guide To Adventure
How to Set Up IoT SSH Login
Setting up IoT SSH login involves several steps, from configuring the server to enabling SSH access on your devices. Below is a step-by-step guide to help you get started:
Step 1: Install SSH Server
Begin by installing an SSH server on your IoT device. Most Linux-based systems come with OpenSSH pre-installed, but you may need to enable it. For Windows devices, you can use tools like PuTTY or Windows Subsystem for Linux (WSL).
Step 2: Configure Firewall Settings
Ensure that your firewall allows incoming connections on the default SSH port (22). Adjusting these settings is crucial for enabling remote access while maintaining security.
Step 3: Test the Connection
Once the server is set up, test the connection by logging in from a remote client. Use the command:
ssh username@ip_address
Replace "username" and "ip_address" with the appropriate values for your device.
Security Considerations for IoT SSH
While SSH provides a secure method for remote access, it's essential to implement additional security measures to protect your IoT devices. Below are some best practices to enhance the security of your IoT SSH setup:
Use Strong Passwords
Avoid using weak or default passwords for your SSH accounts. Instead, opt for strong, complex passwords that combine letters, numbers, and special characters.
Enable Public Key Authentication
Public key authentication offers a more secure alternative to password-based login. By generating a public-private key pair, you can eliminate the need for passwords and reduce the risk of brute-force attacks.
Limit Access
Restrict SSH access to specific IP addresses or networks to minimize the attack surface. This can be achieved by configuring firewall rules or using tools like fail2ban to block malicious login attempts.
Common Use Cases for IoT SSH
IoT SSH login free services find applications in various industries and scenarios. Below are some common use cases:
Remote Device Management
IT administrators can use SSH to manage and monitor IoT devices remotely, ensuring optimal performance and security.
Automated Data Collection
SSH can be used to automate data collection processes, enabling real-time monitoring and analysis of IoT devices.
Software Deployment
Developers can leverage SSH to deploy and update software on IoT devices, streamlining the development and testing process.
Best Practices for IoT SSH
To maximize the benefits of IoT SSH login free platforms, it's essential to follow best practices. Below are some recommendations:
Regularly Update Software
Keep your SSH server and client software up to date to address any security vulnerabilities or bugs.
Monitor Logs
Regularly review SSH logs to detect and respond to suspicious activities or unauthorized access attempts.
Implement Multi-Factor Authentication
For added security, consider implementing multi-factor authentication (MFA) for SSH access. This adds an extra layer of protection beyond passwords or public keys.
Tools and Software for IoT SSH
Several tools and software solutions are available to simplify the implementation and management of IoT SSH login free platforms. Below are some popular options:
OpenSSH
OpenSSH is an open-source implementation of the SSH protocol, widely used for secure remote access. It supports a wide range of platforms and offers extensive configuration options.
PuTTY
PuTTY is a free and portable SSH client for Windows and Unix-based systems. It provides a user-friendly interface for connecting to remote devices via SSH.
SSHFS
SSHFS allows users to mount remote file systems over SSH, enabling seamless file access and management.
Troubleshooting IoT SSH Issues
Despite its reliability, SSH can sometimes encounter issues that prevent successful connections. Below are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, ensure that the SSH server is running and that the firewall allows incoming connections on port 22.
Authentication Failure
Check your username, password, or public key to ensure they match the server's configuration. Incorrect credentials are a common cause of authentication failures.
Timeout Errors
Timeout errors may occur due to network issues or high latency. Verify your internet connection and consider using a faster or more stable network.
Future Trends in IoT SSH
As IoT continues to evolve, SSH will play an increasingly important role in securing and managing connected devices. Below are some trends to watch for:
Quantum-Resistant Cryptography
With the advent of quantum computing, researchers are exploring new encryption methods that can withstand attacks from quantum computers. These advancements will likely influence the future of SSH and IoT security.
Edge Computing Integration
Edge computing will further enhance the capabilities of IoT SSH by enabling faster and more efficient data processing at the network edge.
AI-Driven Security
Artificial intelligence (AI) and machine learning (ML) will play a significant role in detecting and mitigating security threats in IoT SSH environments.
Conclusion
IoT SSH login free platforms offer a powerful and cost-effective solution for managing and accessing remote devices securely. By leveraging the benefits of SSH, users can protect their IoT ecosystems from cyber threats while maintaining flexibility and ease of use.
In conclusion, this guide has explored the fundamentals of IoT SSH, its benefits, implementation strategies, and future trends. We encourage readers to apply the knowledge gained here to enhance their IoT security practices. Don't forget to share your thoughts and experiences in the comments below, and explore other articles on our site for more insights into IoT and cybersecurity.
Data Sources: