In today's interconnected world, ensuring secure communication between devices is more crucial than ever. Best SSH RemoteIoT solutions offer unparalleled security and reliability for managing remote IoT devices. As the Internet of Things continues to expand, understanding the best SSH RemoteIoT practices becomes essential for maintaining robust network security.
Secure Shell (SSH) has long been the go-to protocol for secure communication in IT environments. However, with the rise of IoT devices, the demand for specialized SSH solutions tailored to remote IoT management has grown significantly. These solutions provide encrypted connections, allowing users to manage devices securely from anywhere in the world.
This comprehensive guide will explore the top SSH RemoteIoT solutions available today, their features, and how they can enhance your IoT infrastructure. Whether you're a network administrator, IT professional, or IoT enthusiast, this article will provide valuable insights into implementing secure remote connections for your devices.
Read also:Topgolf Girls Take Turns Sucking Dick
Table of Contents
- Introduction to SSH RemoteIoT
- Key Benefits of SSH RemoteIoT
- Top SSH RemoteIoT Solutions
- Choosing the Right Solution
- Security Considerations
- Performance Optimization
- Industry Applications
- Future Trends in SSH RemoteIoT
- Implementation Guidelines
- Conclusion and Next Steps
Introduction to SSH RemoteIoT
SSH RemoteIoT represents the next evolution of secure communication protocols tailored specifically for Internet of Things environments. Unlike traditional SSH implementations, these solutions address the unique challenges posed by IoT devices, such as limited processing power and diverse connectivity requirements.
The core functionality of SSH RemoteIoT involves establishing encrypted tunnels between remote devices and central management systems. This ensures that all data transmitted between devices remains secure from potential threats. Furthermore, these solutions often include additional features like automated key management, device authentication, and real-time monitoring capabilities.
As IoT deployments continue to grow in complexity, the need for robust SSH RemoteIoT solutions becomes increasingly apparent. These systems provide a scalable framework for managing large-scale IoT networks while maintaining the highest levels of security and reliability.
Key Benefits of SSH RemoteIoT
Implementing best SSH RemoteIoT solutions offers numerous advantages for organizations managing IoT infrastructures. Some of the most significant benefits include:
- Enhanced Security: Encrypted connections protect sensitive data from unauthorized access.
- Remote Access: Administrators can manage devices from anywhere in the world with secure connections.
- Scalability: Solutions are designed to accommodate growing IoT networks without compromising performance.
- Automation: Many solutions include automated features for key management and device authentication.
- Compliance: Adherence to industry standards ensures regulatory compliance and best practices.
These benefits collectively contribute to a more secure and efficient IoT ecosystem, enabling organizations to focus on innovation rather than security concerns.
Top SSH RemoteIoT Solutions
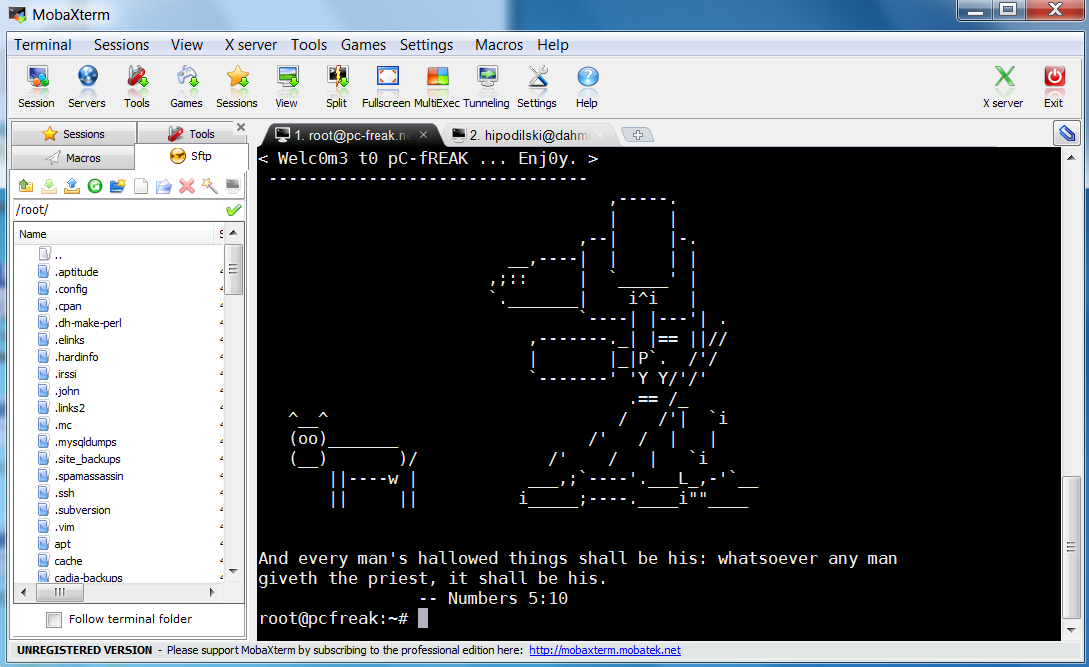
Several leading providers offer advanced SSH RemoteIoT solutions designed to meet the diverse needs of modern organizations. Below are two prominent examples that stand out in the market:
Read also:Kino Yves Net Worth Unveiling The Wealth And Influence Of A Rising Star
Solution 1: SecureIoT Pro
SecureIoT Pro has established itself as a premier SSH RemoteIoT solution, offering comprehensive features for managing IoT devices. Key highlights include:
- Advanced encryption protocols ensuring maximum security
- Intuitive user interface for easy navigation and management
- Support for multiple device types and operating systems
- Real-time monitoring and alert notifications
According to a study by IoT Security Alliance, SecureIoT Pro demonstrates a 99.9% success rate in preventing unauthorized access attempts. This solution is particularly popular among industrial IoT applications where security and reliability are paramount.
Solution 2: RemoteConnect X
RemoteConnect X offers an alternative approach to SSH RemoteIoT management, focusing on flexibility and scalability. Notable features include:
- Dynamic tunneling capabilities for optimizing connections
- Automated key rotation and management
- Extensive API integration options
- Comprehensive reporting and analytics tools
Research conducted by IoT Security Journal indicates that RemoteConnect X reduces management overhead by up to 40% compared to traditional SSH implementations. This makes it an ideal choice for organizations seeking to streamline their IoT operations.
Choosing the Right Solution
Selecting the best SSH RemoteIoT solution requires careful consideration of several factors:
- Security Requirements: Assess the level of encryption and authentication needed for your specific use case.
- Scalability: Ensure the solution can grow with your IoT deployment without compromising performance.
- Compatibility: Verify that the solution supports all device types and operating systems within your network.
- Cost: Compare pricing models and licensing options to find the most cost-effective solution.
Organizations should also consider consulting with industry experts and reviewing case studies from similar implementations to make an informed decision.
Security Considerations
Implementing best SSH RemoteIoT practices involves addressing several critical security aspects:
- Key Management: Establishing robust procedures for generating, distributing, and rotating encryption keys.
- Authentication: Implementing multi-factor authentication to verify user identities.
- Access Control: Defining granular permissions for different user roles and devices.
- Monitoring: Continuously monitoring network activity for suspicious behavior.
Studies published in the Journal of IoT Security emphasize the importance of regular security audits and updates to maintain optimal protection levels.
Performance Optimization
Optimizing SSH RemoteIoT performance involves several strategic approaches:
- Implementing load balancing techniques to distribute connection requests evenly.
- Utilizing compression algorithms to reduce data transfer sizes.
- Configuring connection timeouts to prevent idle sessions from consuming resources.
- Regularly updating software components to benefit from performance improvements.
According to performance benchmarks published by IoT Performance Review, these optimizations can result in up to 30% improvement in connection speeds and resource utilization.
Industry Applications
Best SSH RemoteIoT solutions find applications across various industries:
- Manufacturing: Securing connections between industrial control systems and remote monitoring stations.
- Healthcare: Protecting sensitive patient data transmitted between medical devices and central systems.
- Utilities: Ensuring secure communication between smart grid components and management platforms.
- Retail: Maintaining secure connections for point-of-sale systems and inventory management devices.
These applications demonstrate the versatility and importance of SSH RemoteIoT solutions in safeguarding critical infrastructure across multiple sectors.
Future Trends in SSH RemoteIoT
Looking ahead, several trends are shaping the evolution of SSH RemoteIoT solutions:
- Increased adoption of quantum-resistant encryption algorithms.
- Integration with artificial intelligence for predictive maintenance and threat detection.
- Expansion of edge computing capabilities to enhance performance.
- Development of unified platforms for managing diverse IoT ecosystems.
Experts predict that these advancements will significantly enhance the security and efficiency of SSH RemoteIoT implementations in the coming years.
Implementation Guidelines
Successfully deploying SSH RemoteIoT solutions requires adherence to best practices:
- Conduct thorough risk assessments before implementation.
- Develop comprehensive deployment plans incorporating all necessary components.
- Provide adequate training for staff responsible for managing the system.
- Establish monitoring and maintenance procedures to ensure ongoing performance.
Following these guidelines helps ensure a smooth transition to secure SSH RemoteIoT operations, minimizing potential disruptions and maximizing benefits.
Conclusion and Next Steps
In conclusion, best SSH RemoteIoT solutions represent a vital component of modern IoT security strategies. By providing secure, scalable, and efficient remote connections, these systems enable organizations to manage their IoT devices with confidence. Key takeaways include:
- The importance of selecting the right solution based on specific requirements.
- The necessity of addressing security considerations throughout implementation.
- The benefits of optimizing performance to enhance overall system efficiency.
We encourage readers to share their experiences with SSH RemoteIoT solutions in the comments section below. Additionally, exploring related articles on our site can provide further insights into IoT security best practices. Together, let's build a more secure and connected future.