In the rapidly evolving world of technology, securely connecting remote IoT devices through peer-to-peer (P2P) networks has become an essential skill for enthusiasts and professionals alike. Whether you're setting up a home automation system or managing industrial IoT devices, ensuring secure communication is critical. This guide dives deep into the process of securely connecting remote IoT devices using P2P technology on a Raspberry Pi, complete with free download options and practical tips.
As IoT devices continue to proliferate, the need for secure and efficient communication channels grows exponentially. In this article, we'll explore how to leverage Raspberry Pi to create a robust, secure P2P connection for remote IoT devices. By following the steps outlined, you can ensure that your IoT ecosystem remains protected while maintaining seamless functionality.
This guide is designed for both beginners and advanced users who are interested in exploring IoT security, P2P networking, and Raspberry Pi configurations. We'll cover everything from setting up your Raspberry Pi to downloading and installing the necessary software for secure remote IoT P2P connections.
Read also:Kat Temps Due Date Everything You Need To Know
Table of Contents
- Introduction
- Understanding Raspberry Pi Basics
- The Importance of IoT Security
- What is P2P Networking?
- Setting Up Your Raspberry Pi for IoT P2P
- Free Software Options for Secure Connections
- Download Guides and Installation Steps
- Best Practices for Securing IoT Devices
- Common Issues and Troubleshooting Tips
- Conclusion
Introduction
Securely connect remote IoT P2P Raspberry Pi free download options are becoming increasingly important as more devices come online. The Internet of Things (IoT) has revolutionized how we interact with technology, enabling smart homes, connected cars, and industrial automation systems. However, with this increased connectivity comes the challenge of ensuring secure communication between devices.
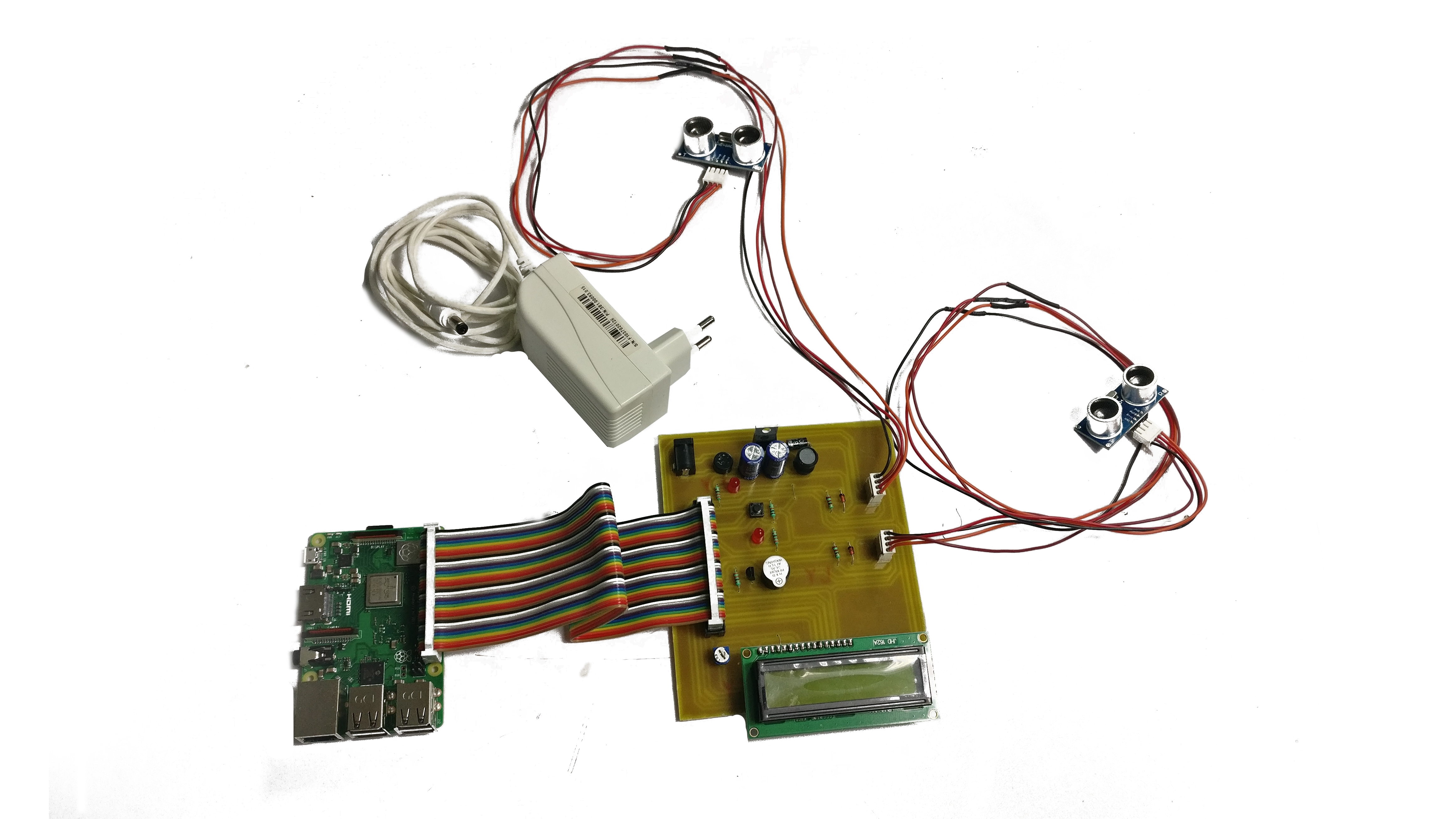
Raspberry Pi serves as an excellent platform for experimenting with IoT applications due to its affordability, versatility, and ease of use. By leveraging P2P networking, you can establish direct connections between IoT devices without relying on centralized servers, reducing latency and enhancing security.
Understanding Raspberry Pi Basics
The Raspberry Pi is a compact, single-board computer that has gained immense popularity among hobbyists, educators, and developers. It offers a powerful yet cost-effective solution for running various applications, including IoT projects. Below are some key features of the Raspberry Pi:
- Low power consumption
- Multiple GPIO pins for interfacing with external devices
- Support for Linux-based operating systems
- Extensive community support and resources
When choosing a Raspberry Pi model for your IoT project, consider factors such as processing power, memory, and connectivity options. The Raspberry Pi 4 is a popular choice due to its improved performance and expanded USB-C support.
The Importance of IoT Security
IoT security is a critical concern for anyone deploying connected devices. Without proper security measures, IoT devices can become vulnerable to cyberattacks, data breaches, and unauthorized access. Securely connect remote IoT P2P Raspberry Pi configurations can help mitigate these risks by:
- Encrypting data transmissions
- Implementing authentication protocols
- Limiting access to authorized devices only
By prioritizing security from the outset, you can protect your IoT ecosystem and ensure the integrity of your data.
Read also:Who Is Cj Strouds Girlfriend Everything You Need To Know About Their Relationship
What is P2P Networking?
Peer-to-Peer Networking Defined
P2P networking allows devices to communicate directly with one another without the need for a central server. This architecture offers several advantages, including:
- Reduced latency
- Improved scalability
- Enhanced security through decentralized communication
In the context of IoT, P2P networking can significantly enhance the performance and reliability of connected devices. By securely connect remote IoT P2P Raspberry Pi setups, you can create a robust network that operates independently of traditional server-based architectures.
Setting Up Your Raspberry Pi for IoT P2P
Step-by-Step Guide
Setting up your Raspberry Pi for secure IoT P2P connections involves several key steps:
- Install the latest version of Raspberry Pi OS
- Enable SSH for remote access
- Configure Wi-Fi or Ethernet settings
- Install necessary libraries and dependencies
Each of these steps plays a crucial role in ensuring a secure and stable connection. For example, enabling SSH allows you to remotely manage your Raspberry Pi, while configuring network settings ensures proper communication with other devices.
Free Software Options for Secure Connections
Open-Source Tools for IoT Security
Several free software options are available for securely connect remote IoT P2P Raspberry Pi setups. These include:
- OpenVPN: A widely used open-source solution for creating secure virtual private networks (VPNs)
- WireGuard: A modern, lightweight alternative to traditional VPNs
- Tailscale: A user-friendly P2P networking tool that simplifies device connections
Each of these tools offers unique features and benefits, so it's important to evaluate your specific needs before choosing a solution. For example, WireGuard is known for its speed and simplicity, making it an excellent choice for resource-constrained environments.
Download Guides and Installation Steps
How to Download and Install OpenVPN
Downloading and installing OpenVPN on your Raspberry Pi is a straightforward process. Follow these steps:
- Update your system:
sudo apt update && sudo apt upgrade - Install OpenVPN:
sudo apt install openvpn - Download the desired configuration file from the OpenVPN website
- Transfer the configuration file to your Raspberry Pi using SCP or USB
- Start the OpenVPN service:
sudo openvpn --config your_config_file.ovpn
By following these steps, you can establish a secure connection between your Raspberry Pi and other IoT devices.
Best Practices for Securing IoT Devices
Key Strategies for IoT Security
To ensure the security of your IoT ecosystem, consider implementing the following best practices:
- Use strong, unique passwords for all devices
- Regularly update firmware and software
- Limit network access to trusted devices
- Monitor device activity for suspicious behavior
By adopting these strategies, you can significantly reduce the risk of security breaches and protect your IoT devices from potential threats.
Common Issues and Troubleshooting Tips
Addressing Connectivity Problems
While setting up a securely connect remote IoT P2P Raspberry Pi network, you may encounter various issues. Below are some common problems and their solutions:
- Device not connecting: Verify network settings and ensure all devices are on the same subnet.
- Slow performance: Optimize your network configuration and consider upgrading your hardware if necessary.
- Authentication errors: Double-check your credentials and ensure all devices have the correct certificates installed.
For more advanced troubleshooting, consult the official Raspberry Pi documentation or seek assistance from online communities.
Conclusion
Securing remote IoT P2P Raspberry Pi connections is essential for maintaining a safe and reliable IoT ecosystem. By following the steps outlined in this guide, you can create a robust, secure network that meets your needs. Remember to prioritize security best practices and stay informed about the latest developments in IoT technology.
We encourage you to share your experiences and insights in the comments below. Additionally, feel free to explore other articles on our site for more information on IoT, Raspberry Pi, and related topics. Together, let's build a safer, smarter connected world!
Data sources and references: