In today's digital age, remote IoT web SSH has become an essential tool for managing and maintaining Internet of Things (IoT) devices securely from any location. Whether you're a developer, network administrator, or IT professional, understanding how to leverage SSH for remote IoT management can significantly enhance your productivity and security. This comprehensive guide will walk you through everything you need to know about remote IoT web SSH, from its basics to advanced configurations.
As the Internet of Things continues to expand, the demand for secure remote access solutions is growing exponentially. RemoteIoT web SSH offers a robust and encrypted method to interact with IoT devices over the internet. By utilizing SSH protocols, users can establish secure connections, execute commands, and manage configurations without compromising sensitive data.
This article aims to provide a detailed overview of remote IoT web SSH, covering its benefits, setup processes, security considerations, and best practices. Whether you're a beginner or an experienced professional, this guide will equip you with the knowledge and tools necessary to implement and manage secure remote IoT connections effectively.
Read also:Who Is Peyton Mannings Wife Everything You Need To Know About Her Life And Legacy
Table of Contents
- Introduction to RemoteIoT Web SSH
- Why RemoteIoT Web SSH is Important
- Setting Up RemoteIoT Web SSH
- Benefits of RemoteIoT Web SSH
- Security Considerations
- Common Issues and Troubleshooting
- Best Practices for RemoteIoT Web SSH
- Real-World Applications
- Future Trends in RemoteIoT Web SSH
- Conclusion
Introduction to RemoteIoT Web SSH
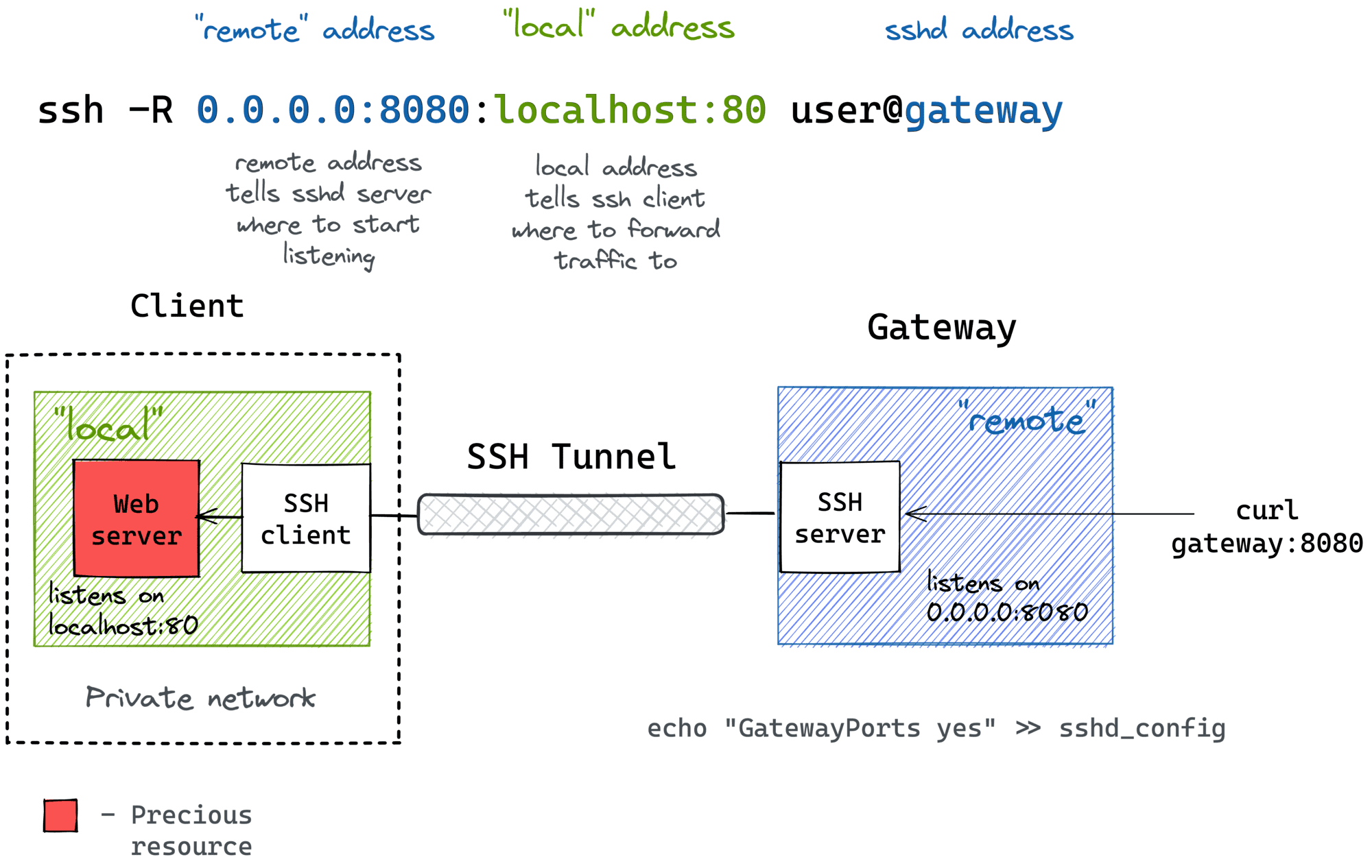
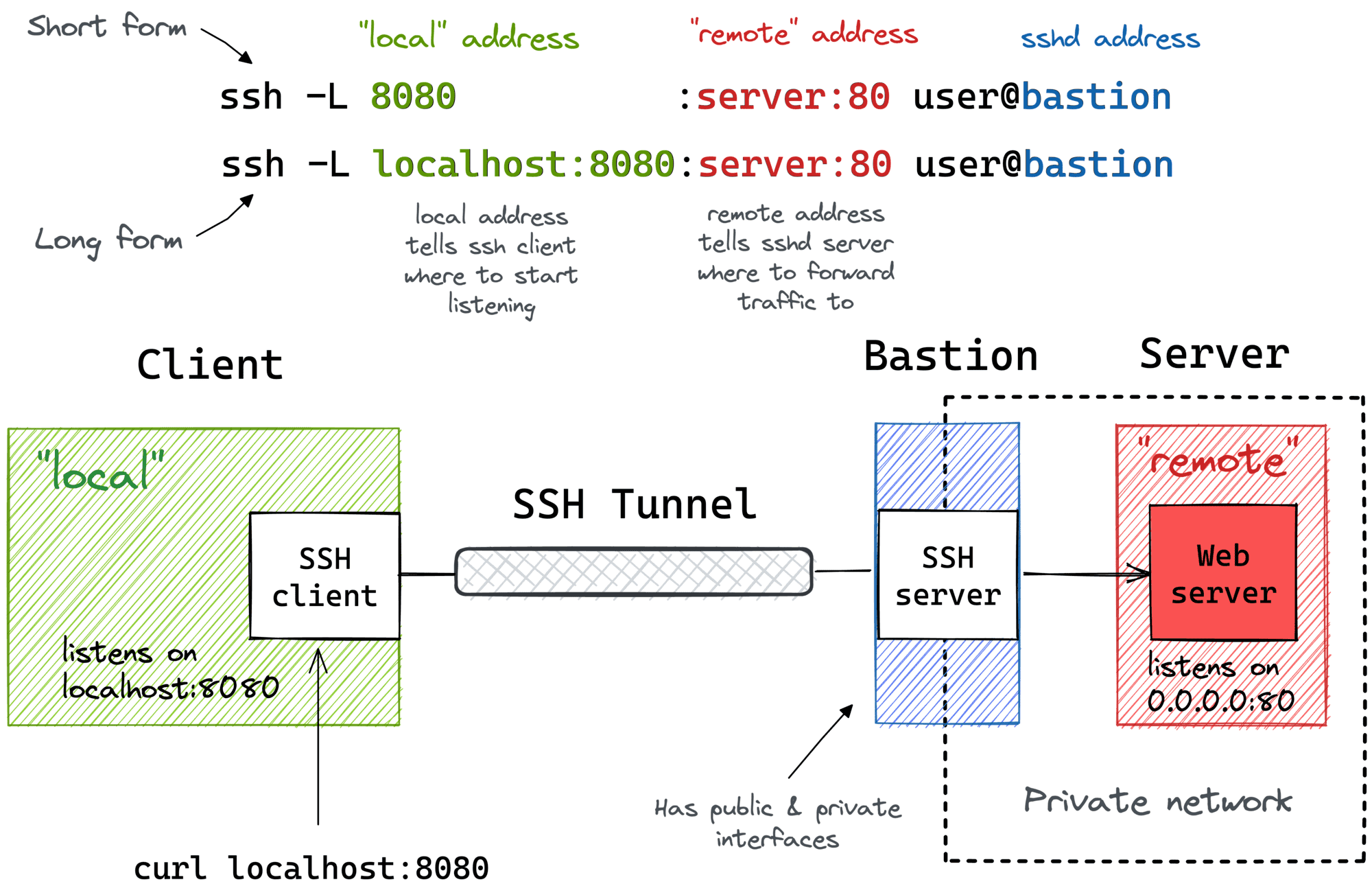
RemoteIoT web SSH is a secure protocol designed to facilitate remote access to IoT devices through web-based interfaces. It combines the power of SSH (Secure Shell) with web technologies, enabling users to manage IoT devices from anywhere in the world. By leveraging this technology, organizations can streamline their operations, reduce costs, and improve overall efficiency.
SSH, originally developed as a secure alternative to Telnet, has evolved into a cornerstone of modern networking. When applied to IoT devices, it provides a reliable and encrypted method for data transmission and device management. RemoteIoT web SSH takes this concept further by integrating web-based interfaces, making it accessible to users with varying levels of technical expertise.
This section will delve into the fundamental principles of remote IoT web SSH, explaining how it works and why it is becoming increasingly popular in the IoT landscape.
Why RemoteIoT Web SSH is Important
In the rapidly evolving world of IoT, the ability to manage devices remotely is no longer a luxury but a necessity. RemoteIoT web SSH addresses this need by offering a secure and efficient solution for remote device management. Its importance lies in its ability to:
- Enhance security through encryption and authentication.
- Provide seamless access to IoT devices from anywhere.
- Reduce operational costs by eliminating the need for on-site visits.
- Improve productivity by enabling real-time monitoring and management.
As the number of connected devices continues to grow, the demand for secure remote access solutions like remote IoT web SSH will only increase. Organizations that adopt this technology early will have a significant advantage in terms of efficiency and security.
Setting Up RemoteIoT Web SSH
Prerequisites
Before setting up remote IoT web SSH, ensure that you have the following prerequisites in place:
Read also:What Is A Filly Horse A Complete Guide To Understanding Young Female Horses
- An IoT device with SSH capabilities.
- A stable internet connection.
- A web server configured to support SSH tunneling.
- Basic knowledge of SSH and networking concepts.
Having these prerequisites will ensure a smooth setup process and minimize potential issues.
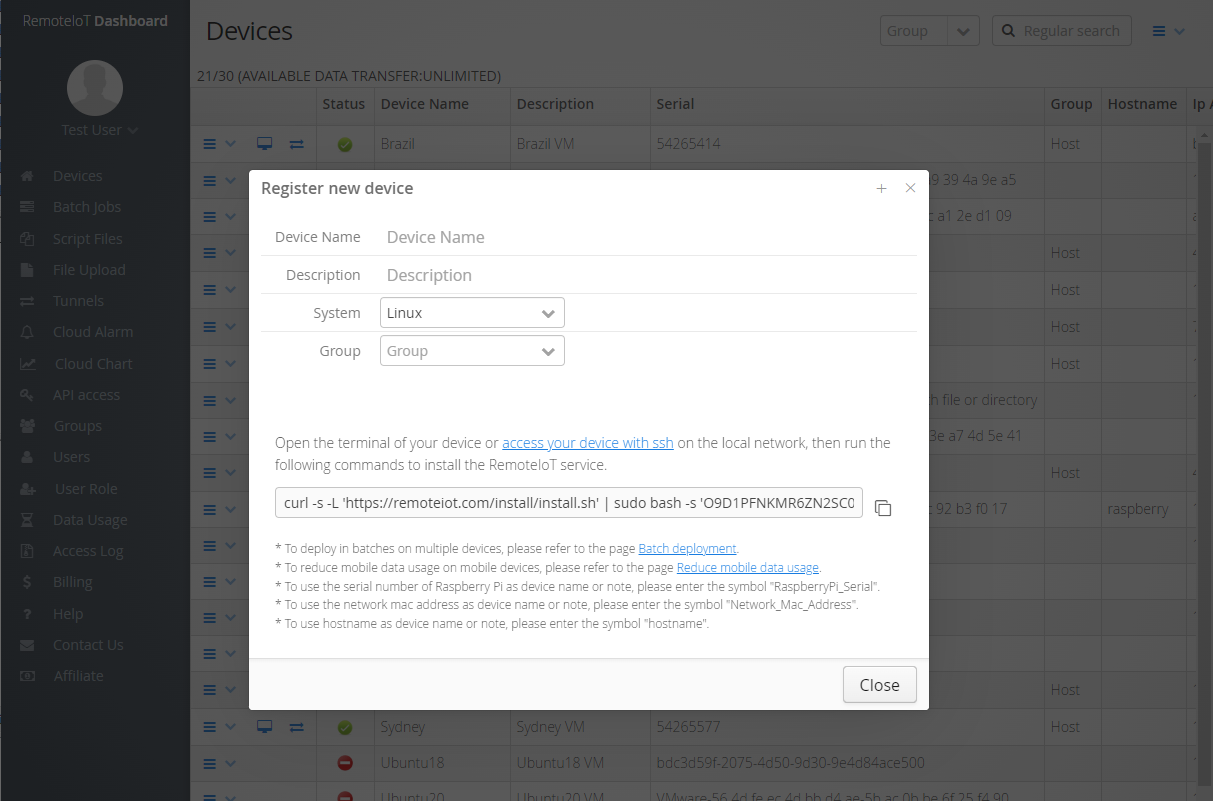
Installation Process
The installation process for remote IoT web SSH involves several key steps:
- Configure the IoT device to enable SSH access.
- Set up a web server to act as a bridge between the device and the user.
- Install and configure SSH client software on the user's device.
- Test the connection to ensure secure and reliable access.
Each step is crucial for establishing a functional and secure remote IoT web SSH environment.
Benefits of RemoteIoT Web SSH
RemoteIoT web SSH offers numerous benefits that make it an attractive solution for IoT device management. Some of the key advantages include:
- Enhanced security through end-to-end encryption.
- Improved accessibility, allowing users to manage devices from anywhere.
- Cost savings by reducing the need for on-site visits.
- Increased efficiency through real-time monitoring and control.
- Compatibility with a wide range of IoT devices and platforms.
These benefits make remote IoT web SSH an essential tool for anyone involved in IoT device management.
Security Considerations
Encryption Methods
Encryption is a critical component of remote IoT web SSH, ensuring that data transmitted between devices remains secure. Common encryption methods used in SSH include:
- AES (Advanced Encryption Standard)
- Blowfish
- 3DES (Triple Data Encryption Standard)
By selecting the appropriate encryption method, users can protect their data from unauthorized access and potential cyber threats.
Authentication Techniques
Authentication is another vital aspect of remote IoT web SSH security. Popular authentication techniques include:
- Password-based authentication
- Public key authentication
- Two-factor authentication (2FA)
Implementing robust authentication methods can significantly enhance the security of remote IoT web SSH connections.
Common Issues and Troubleshooting
While remote IoT web SSH is a powerful tool, users may encounter various issues during setup and operation. Common problems include:
- Connection timeouts
- Authentication failures
- Firewall restrictions
To address these issues, users can refer to the following troubleshooting tips:
- Check network configurations and ensure proper port forwarding.
- Verify SSH settings and authentication credentials.
- Consult the device's user manual for specific troubleshooting guidance.
By following these steps, users can resolve most common issues and maintain a stable remote IoT web SSH connection.
Best Practices for RemoteIoT Web SSH
To maximize the effectiveness and security of remote IoT web SSH, consider adopting the following best practices:
- Regularly update SSH software and firmware to address security vulnerabilities.
- Use strong passwords and enable public key authentication for added security.
- Implement network monitoring tools to detect and respond to potential threats.
- Limit access to authorized users only and enforce strict access controls.
By adhering to these best practices, users can ensure a secure and reliable remote IoT web SSH environment.
Real-World Applications
RemoteIoT web SSH is widely used across various industries, including:
- Manufacturing, where it enables remote monitoring and control of production equipment.
- Healthcare, where it facilitates secure access to medical devices and patient data.
- Smart cities, where it supports the management of connected infrastructure.
These applications demonstrate the versatility and importance of remote IoT web SSH in modern technology landscapes.
Future Trends in RemoteIoT Web SSH
As technology continues to evolve, the future of remote IoT web SSH looks promising. Emerging trends include:
- Integration with artificial intelligence (AI) for enhanced automation and security.
- Development of quantum-resistant encryption methods to address future security challenges.
- Expansion of IoT ecosystems, driving the need for more advanced remote management solutions.
By staying informed about these trends, users can prepare for the future of remote IoT web SSH and its role in shaping the IoT landscape.
Conclusion
RemoteIoT web SSH represents a powerful and secure solution for managing IoT devices remotely. By understanding its principles, benefits, and security considerations, users can effectively implement and manage this technology to enhance their operations. We encourage readers to:
- Experiment with remote IoT web SSH in their own environments.
- Share their experiences and insights in the comments section below.
- Explore additional resources and articles on our website for further learning.
Together, we can harness the potential of remote IoT web SSH to drive innovation and improve security in the IoT space.
For further reading, refer to trusted sources such as SSH.com and IoT For All for comprehensive guides and updates on SSH and IoT technologies.