In today's digital era, the remoteIoT platform SSH key plays a pivotal role in ensuring secure communication between devices. As the Internet of Things (IoT) continues to grow, understanding the intricacies of SSH keys has become essential for maintaining robust cybersecurity measures. This guide will delve into the nuances of SSH keys within the remoteIoT platform, empowering users with actionable insights.
The significance of secure communication cannot be overstated, especially in an IoT-driven world. With billions of interconnected devices exchanging data, vulnerabilities in security protocols can lead to catastrophic breaches. RemoteIoT platforms, equipped with SSH keys, provide a secure channel for device management and data transfer, making them indispensable for modern IoT deployments.
This article aims to equip readers with a deep understanding of remoteIoT platform SSH keys, from their foundational principles to advanced implementation strategies. Whether you're a beginner or an experienced professional, this guide will cater to your needs, offering practical advice and expert insights to enhance your IoT security framework.
Read also:Lord Have Mercy Meme A Comprehensive Dive Into Its Origins Popularity And Cultural Impact
Table of Contents
- Introduction to RemoteIoT Platform
- Understanding SSH Keys
- The Importance of SSH in IoT
- Implementing SSH Keys in RemoteIoT
- Security Considerations for SSH Keys
- Best Practices for Managing SSH Keys
- Troubleshooting Common SSH Key Issues
- Automation and Scalability in RemoteIoT
- Future Trends in IoT Security
- Conclusion
Introduction to RemoteIoT Platform
RemoteIoT platforms serve as the backbone of modern IoT ecosystems, enabling seamless communication and management of connected devices. These platforms leverage advanced technologies, such as SSH keys, to ensure secure and reliable interactions. By integrating SSH keys into their architecture, RemoteIoT platforms provide an additional layer of protection against unauthorized access and data breaches.
Key Features of RemoteIoT Platforms
RemoteIoT platforms are designed to cater to the unique needs of IoT deployments, offering a range of features that enhance functionality and security:
- Device Management: Comprehensive tools for monitoring and controlling connected devices.
- Data Encryption: Built-in encryption protocols, including SSH keys, to safeguard sensitive information.
- Scalability: The ability to accommodate growing numbers of devices without compromising performance.
- Real-Time Analytics: Advanced analytics capabilities for processing and interpreting IoT data in real-time.
With these features, RemoteIoT platforms empower organizations to build secure and efficient IoT infrastructures.
Understanding SSH Keys
SSH keys are cryptographic keys used for securely authenticating users or devices over a network. They serve as a more secure alternative to traditional password-based authentication methods, reducing the risk of unauthorized access. In the context of remoteIoT platform SSH key integration, understanding the basics of SSH keys is crucial for effective implementation.
Types of SSH Keys
There are several types of SSH keys, each with its own strengths and use cases:
- RSA Keys: Widely used and considered secure for most applications.
- ECDSA Keys: Offer faster performance and shorter key lengths compared to RSA keys.
- Ed25519 Keys: Known for their high security and efficiency, making them ideal for modern IoT applications.
Selecting the appropriate SSH key type depends on the specific requirements of your remoteIoT platform deployment.
Read also:Unveiling The Ultimate Guide To Tekken 8 Ranks Mastering The Art Of Fighting
The Importance of SSH in IoT
SSH keys play a vital role in securing IoT ecosystems, addressing the unique challenges posed by interconnected devices. In the realm of remoteIoT platforms, SSH keys provide a secure mechanism for device authentication and data encryption, mitigating potential security risks.
Benefits of Using SSH in IoT
Implementing SSH keys in IoT environments offers numerous benefits:
- Enhanced Security: Prevents unauthorized access and ensures data integrity.
- Scalability: Supports large-scale IoT deployments without compromising security.
- Automation: Facilitates automated processes for device management and data transfer.
By leveraging SSH keys, organizations can build resilient IoT infrastructures that meet the demands of today's digital landscape.
Implementing SSH Keys in RemoteIoT
Successfully integrating SSH keys into a remoteIoT platform requires a structured approach. This section will guide you through the implementation process, ensuring a secure and efficient deployment.
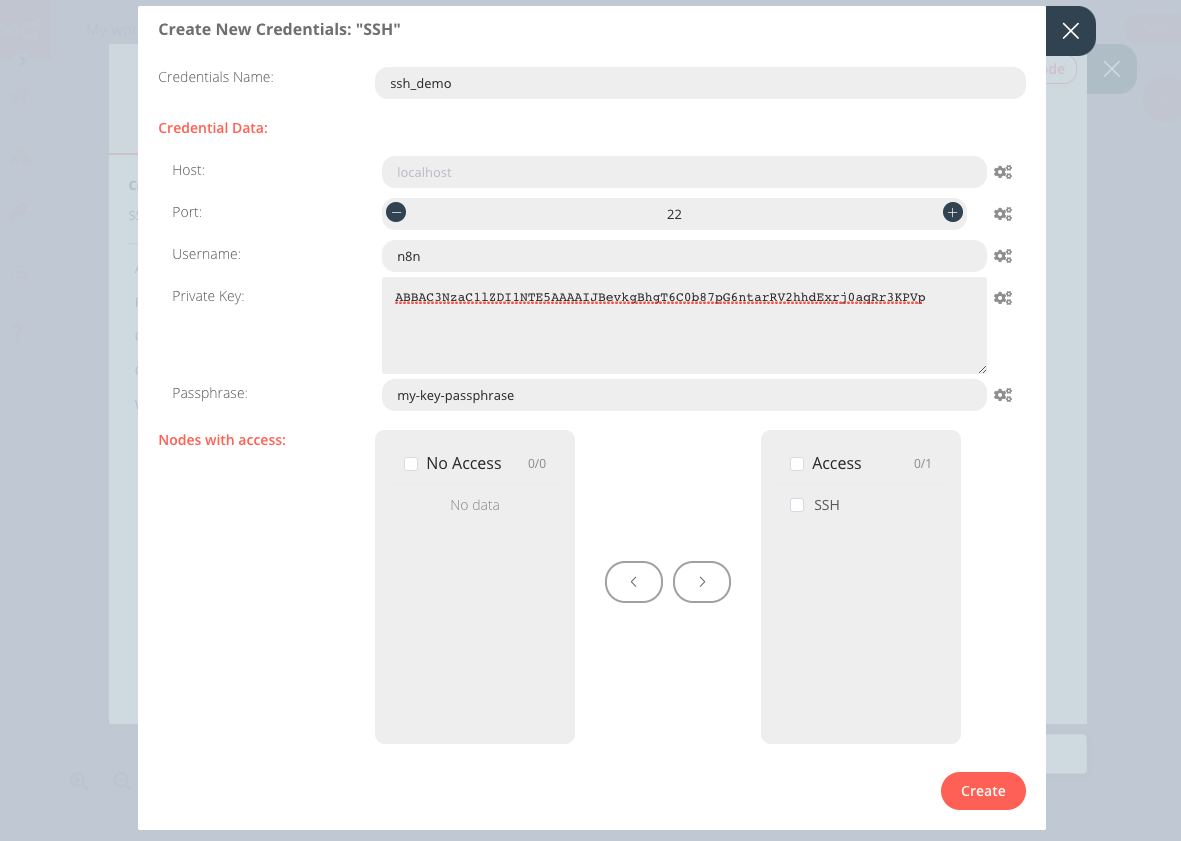
Step-by-Step Guide
- Generate SSH Key Pair: Use tools like OpenSSH to create a public-private key pair.
- Configure RemoteIoT Platform: Update platform settings to accept SSH key-based authentication.
- Test Connectivity: Verify that devices can establish secure connections using SSH keys.
- Monitor and Maintain: Regularly review and update SSH keys to ensure ongoing security.
Following these steps will help you establish a secure SSH key infrastructure within your remoteIoT platform.
Security Considerations for SSH Keys
While SSH keys offer robust security, they are not without vulnerabilities. It's essential to address potential security risks to ensure the integrity of your remoteIoT platform.
Common Security Threats
- Key Mismanagement: Failing to securely store or rotate SSH keys can lead to unauthorized access.
- Weak Key Algorithms: Using outdated or weak algorithms may compromise encryption strength.
- Phishing Attacks: Social engineering tactics can trick users into revealing private SSH keys.
By implementing proper security measures, such as key rotation and multi-factor authentication, organizations can minimize these risks and safeguard their remoteIoT platforms.
Best Practices for Managing SSH Keys
Effective management of SSH keys is critical for maintaining the security of remoteIoT platforms. This section outlines best practices to help you optimize your SSH key infrastructure.
Key Management Strategies
- Regular Key Rotation: Update SSH keys periodically to prevent long-term exposure.
- Access Control: Limit SSH key access to authorized personnel only.
- Audit and Monitoring: Conduct regular audits to identify and address potential security issues.
Adhering to these best practices will enhance the security and reliability of your remoteIoT platform.
Troubleshooting Common SSH Key Issues
Despite their effectiveness, SSH keys can sometimes encounter issues that disrupt connectivity. This section addresses common problems and provides solutions to help you resolve them.
Typical Issues and Solutions
- Connection Errors: Verify SSH key configuration and ensure proper permissions are set.
- Key Expiration: Update expired keys and notify affected users of the changes.
- Authentication Failures: Check for typos or mismatches in public and private keys.
By identifying and addressing these issues promptly, you can maintain uninterrupted connectivity within your remoteIoT platform.
Automation and Scalability in RemoteIoT
As IoT ecosystems continue to expand, automation and scalability become increasingly important. SSH keys play a crucial role in enabling these capabilities within remoteIoT platforms.
Automation Tools for SSH Key Management
Leveraging automation tools can streamline SSH key management processes, improving efficiency and reducing errors:
- Ansible: Automates SSH key deployment and configuration across multiple devices.
- Puppet: Provides centralized control for managing SSH keys in large-scale deployments.
- Chef: Offers robust automation capabilities for SSH key lifecycle management.
By integrating automation tools, organizations can achieve scalable and secure SSH key management within their remoteIoT platforms.
Future Trends in IoT Security
The landscape of IoT security is constantly evolving, with emerging trends shaping the future of remoteIoT platforms. Staying informed about these trends will help organizations adapt and thrive in an ever-changing digital environment.
Emerging Technologies
- Quantum Cryptography: Offers unparalleled security for SSH key encryption.
- Blockchain: Provides decentralized solutions for secure SSH key storage and management.
- AI-driven Security: Utilizes artificial intelligence to detect and respond to potential threats in real-time.
Embracing these advancements will enable organizations to build cutting-edge remoteIoT platforms that meet the demands of tomorrow's IoT landscape.
Conclusion
In conclusion, the remoteIoT platform SSH key serves as a cornerstone of IoT security, ensuring secure communication and device management. By understanding the fundamentals of SSH keys and implementing best practices, organizations can build robust and scalable IoT infrastructures. We encourage readers to apply the insights gained from this guide, leaving comments or sharing the article to further promote IoT security awareness.
For more information on remoteIoT platform SSH keys and related topics, explore additional resources and stay updated on the latest developments in IoT security.
References:
- OpenSSH Documentation: https://www.openssh.com/manual.html
- NIST Cybersecurity Framework: https://www.nist.gov/cyberframework
- IoT Security Foundation: https://iotsecurityfoundation.org/