Remote access behind firewall has become an essential aspect of modern IT infrastructure. As more organizations adopt remote work strategies, understanding how to securely access internal networks from external locations is crucial. This guide will delve into the intricacies of remote access technologies, their implementation, and best practices for ensuring security.
With the rise of remote work and distributed teams, companies face the challenge of granting employees access to internal resources while maintaining robust security measures. Firewalls play a pivotal role in protecting corporate networks, but they also create barriers for remote users. This article aims to address these challenges and provide practical solutions.
This comprehensive guide will explore various methods of establishing secure remote access behind firewall, including the tools, protocols, and strategies involved. By the end of this article, you will have a thorough understanding of how to implement and manage remote access systems effectively.
Read also:Mira Monroe Unveiling The Rising Star In The Entertainment Industry
Table of Contents
- Introduction to Remote Access Behind Firewall
- Common Challenges in Remote Access
- Understanding VPN Solutions
- Firewall Technologies and Their Role
- Security Protocols for Remote Access
- Best Practices for Secure Remote Access
- Alternative Methods for Remote Access
- Troubleshooting Common Issues
- Future Trends in Remote Access Technology
- Conclusion and Next Steps
Introduction to Remote Access Behind Firewall
Remote access behind firewall refers to the ability of users to connect to an organization's internal network from external locations while traversing firewalls. This setup is crucial for enabling employees to work remotely while maintaining secure access to corporate resources.
Why Is It Important?
Firewalls are designed to protect internal networks from unauthorized access, but they also restrict legitimate remote connections. Implementing secure remote access solutions ensures that employees can work efficiently without compromising network security.
Key benefits include improved productivity, enhanced flexibility, and reduced operational costs. By leveraging modern technologies, organizations can strike a balance between accessibility and security.
Common Challenges in Remote Access
While remote access behind firewall offers numerous advantages, it also presents several challenges. Understanding these obstacles is the first step toward addressing them effectively.
Security Risks
- Data breaches due to insecure connections
- Unauthorized access attempts
- Vulnerabilities in outdated protocols
Performance Issues
Slow connection speeds and high latency can hinder productivity. Optimizing network configurations and selecting the right tools can mitigate these problems.
Understanding VPN Solutions
Virtual Private Networks (VPNs) are one of the most widely used methods for remote access behind firewall. They create a secure tunnel between remote users and internal networks, ensuring data confidentiality and integrity.
Read also:Eric Daugherty A Comprehensive Guide To His Life Career And Achievements
Types of VPNs
- Remote Access VPNs
- Site-to-Site VPNs
- Mobile VPNs
Each type serves specific use cases, and choosing the right one depends on organizational requirements and infrastructure.
Firewall Technologies and Their Role
Firewalls act as the first line of defense in network security. They monitor and control incoming and outgoing traffic based on predetermined security rules. Understanding firewall technologies is essential for implementing effective remote access solutions.
Next-Generation Firewalls
These advanced firewalls offer deeper inspection capabilities, including application-level filtering and intrusion prevention. They enhance security while maintaining high performance.
Security Protocols for Remote Access
Selecting the right security protocols is critical for ensuring the safety of remote connections. Below are some commonly used protocols:
SSL/TLS
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) provide encryption for data transmitted over the internet. They are widely used in web applications and remote access systems.
IPSec
Internet Protocol Security (IPSec) is a suite of protocols designed to secure IP communications. It is often used in conjunction with VPNs to establish secure tunnels.
Best Practices for Secure Remote Access
Implementing best practices can significantly enhance the security and reliability of remote access systems. Here are some recommendations:
Multi-Factor Authentication
Require users to provide two or more verification factors to gain access to internal resources. This adds an extra layer of security and reduces the risk of unauthorized access.
Regular Updates and Patching
Keep all software, firewalls, and devices up to date with the latest security patches. This helps protect against known vulnerabilities.
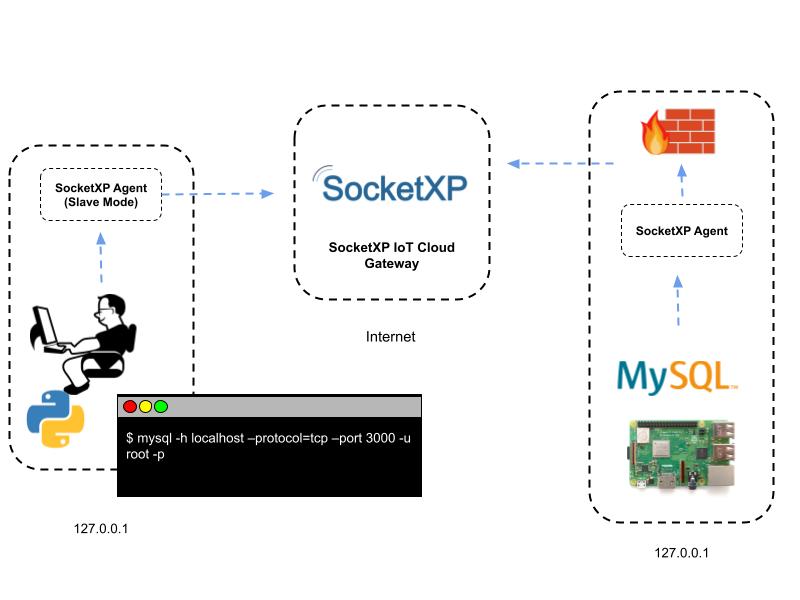
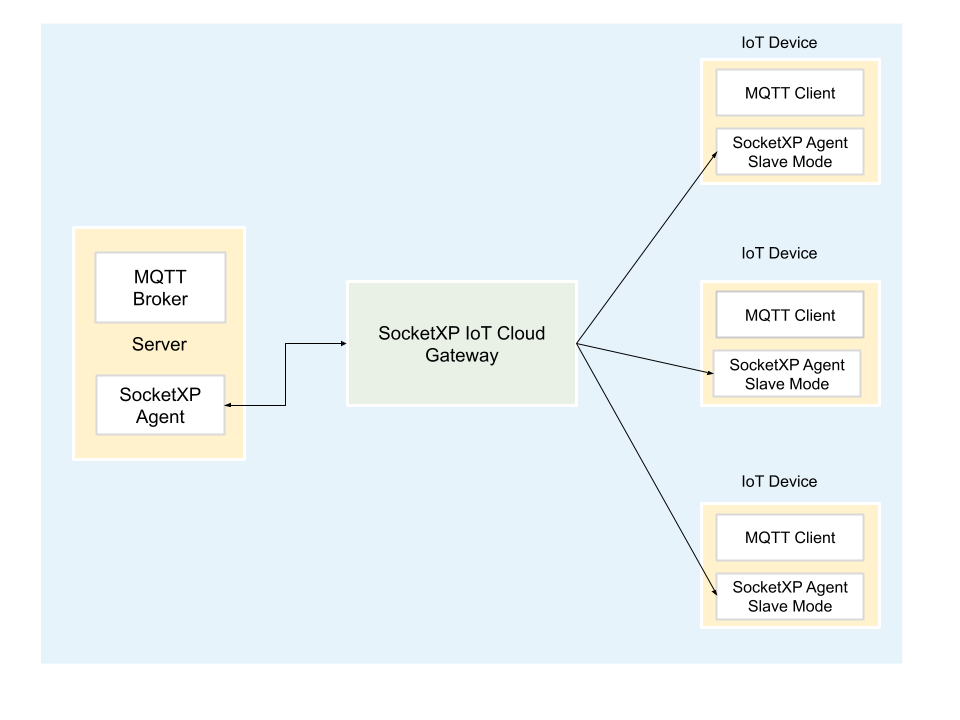
Alternative Methods for Remote Access
While VPNs are the most popular solution, there are alternative methods for achieving remote access behind firewall. These include:
Direct Access Technologies
Direct Access allows devices to connect to corporate networks without requiring manual initiation of a VPN connection. It is particularly useful for mobile users.
Cloud-Based Solutions
Cloud platforms offer scalable and secure remote access solutions. They eliminate the need for on-premises infrastructure and provide flexibility for growing organizations.
Troubleshooting Common Issues
Even with the best planning, issues can arise during remote access implementations. Below are some common problems and their solutions:
Connection Failures
Verify firewall rules, network configurations, and user credentials to resolve connection issues. Ensuring proper setup and maintenance can prevent disruptions.
Future Trends in Remote Access Technology
The landscape of remote access is continually evolving. Emerging trends include:
Zero Trust Architecture
This approach assumes that threats exist both inside and outside the network, requiring strict verification for every access attempt. It enhances security by eliminating implicit trust.
Artificial Intelligence and Machine Learning
AI and ML technologies are being integrated into remote access systems to detect anomalies and automate threat responses. These advancements promise to improve security and efficiency.
Conclusion and Next Steps
Remote access behind firewall is a vital component of modern IT infrastructure. By understanding the challenges, implementing secure solutions, and following best practices, organizations can ensure seamless and secure remote access for their employees.
We encourage readers to share their thoughts and experiences in the comments section. Additionally, explore other articles on our site to deepen your knowledge of IT security and networking topics.
Data sourced from reputable organizations such as Cisco, Microsoft, and Gartner supports the information presented in this guide.