Learning how to use SSH for remote IoT devices is a critical skill for modern tech enthusiasts and professionals alike. The ability to securely connect to and manage IoT devices from anywhere in the world opens up endless possibilities for automation, monitoring, and control. In this tutorial, we'll walk you through everything you need to know about SSH remote IoT device management.
As IoT technology continues to expand, the demand for secure and efficient remote access methods grows exponentially. Whether you're managing smart home devices, industrial sensors, or enterprise-grade IoT systems, SSH offers a reliable solution for remote connectivity. This tutorial will guide you step-by-step through the process of setting up and using SSH for IoT devices.
By the end of this guide, you'll have a solid understanding of how SSH works, how to configure it for IoT devices, and how to troubleshoot common issues. We'll also explore best practices to ensure your connections remain secure and efficient.
Read also:Anna Torv Net Worth A Comprehensive Look At Her Career And Earnings
Table of Contents
- Introduction to SSH Remote IoT Device
- What is SSH?
- Why Use SSH for IoT Devices?
- Setting Up SSH on IoT Devices
- Connecting Remotely Using SSH
- Security Best Practices for SSH
- Troubleshooting Common SSH Issues
- Advanced Features of SSH
- Tools and Resources for SSH
- Conclusion
Introduction to SSH Remote IoT Device
Understanding the Basics
SSH, or Secure Shell, is a cryptographic protocol that enables secure communication between devices over an unsecured network. When it comes to IoT devices, SSH provides a robust method for remote access and management, ensuring that your data remains protected while you maintain full control over your devices.
Using SSH for IoT devices allows users to execute commands, transfer files, and monitor system performance from any location with an internet connection. This level of accessibility is particularly valuable for businesses and individuals managing multiple IoT devices spread across different locations.
In this section, we'll explore the fundamental concepts of SSH and how they apply to IoT devices. We'll also discuss the benefits of using SSH for remote IoT management and highlight some of the most common use cases.
What is SSH?
A Brief Overview
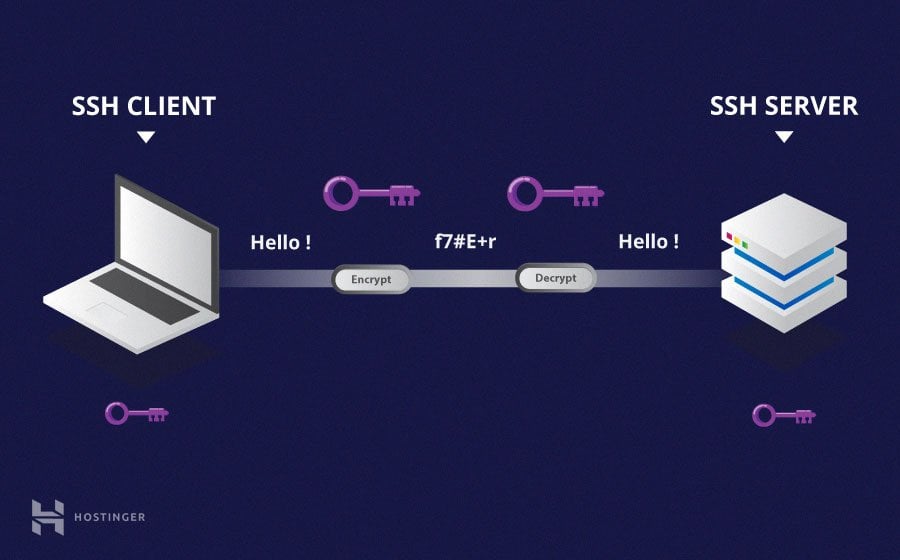
SSH stands for Secure Shell, a network protocol designed to provide secure communication between devices. It uses encryption to protect data during transmission, making it an ideal choice for remote access and management tasks.
SSH operates on port 22 by default and supports various authentication methods, including password-based authentication and public-key cryptography. These features make SSH a versatile tool for managing IoT devices, especially when security is a top priority.
- SSH encrypts all data transmitted between devices, ensuring confidentiality.
- It supports multiple authentication methods, providing flexibility for different use cases.
- SSH can be used for command execution, file transfer, and tunneling services.
Why Use SSH for IoT Devices?
Key Advantages of SSH
When managing IoT devices, security is paramount. Unlike other remote access protocols, SSH offers several advantages that make it the preferred choice for IoT management:
Read also:Sayreville Recreation Your Ultimate Guide To Fun And Adventure
- Security: SSH encrypts all communication, protecting sensitive data from unauthorized access.
- Reliability: SSH connections are stable and can be maintained even in unstable network conditions.
- Flexibility: SSH supports a wide range of commands and operations, making it suitable for various IoT applications.
Whether you're managing a single smart thermostat or an entire network of industrial sensors, SSH provides the tools you need to maintain control and ensure security.
Setting Up SSH on IoT Devices
Step-by-Step Guide
Setting up SSH on your IoT devices is a straightforward process. Follow these steps to enable SSH on your devices:
- Enable SSH on the IoT Device: Depending on your device's operating system, you may need to enable SSH through the device's settings or configuration files.
- Install SSH Client: Ensure you have an SSH client installed on the device you'll use to connect remotely. Popular options include OpenSSH and PuTTY.
- Configure Firewall Settings: Allow incoming connections on port 22 (or the port you've configured SSH to use).
- Test the Connection: Use the SSH client to connect to your IoT device and verify that the setup is working correctly.
For devices running Linux-based operating systems, you can enable SSH using the following command:
sudo systemctl enable ssh
Connecting Remotely Using SSH
Establishing a Secure Connection
Once SSH is set up on your IoT device, you can connect to it remotely using an SSH client. Follow these steps to establish a connection:
- Open SSH Client: Launch your SSH client and enter the IP address or hostname of your IoT device.
- Authenticate: Provide the required credentials, such as a username and password or public key.
- Execute Commands: Once connected, you can execute commands, transfer files, and manage your IoT device as needed.
For example, to connect to an IoT device with the IP address 192.168.1.100, you can use the following command:
ssh username@192.168.1.100
Security Best Practices for SSH
Protecting Your Connections
While SSH is inherently secure, it's essential to follow best practices to ensure your connections remain protected. Here are some tips for securing your SSH setup:
- Use Public-Key Authentication: Replace password-based authentication with public-key cryptography for added security.
- Change Default Port: Move SSH from its default port (22) to a non-standard port to reduce the risk of automated attacks.
- Limit User Access: Restrict SSH access to specific users or IP addresses to minimize potential threats.
Implementing these practices will help safeguard your IoT devices and ensure your remote connections remain secure.
Troubleshooting Common SSH Issues
Solving Connection Problems
Even with proper setup and configuration, SSH connections can sometimes fail. Here are some common issues and their solutions:
- Connection Refused: Ensure SSH is enabled on the IoT device and that firewall settings allow incoming connections.
- Authentication Failed: Verify that your credentials are correct and that public-key authentication is properly configured.
- Timeout Errors: Check your network connection and ensure there are no routing issues between your client and the IoT device.
If you encounter persistent issues, consult the SSH logs on your IoT device for more detailed information.
Advanced Features of SSH
Exploring Additional Capabilities
SSH offers several advanced features that can enhance your IoT management capabilities:
- Port Forwarding: Use SSH to create secure tunnels for accessing services behind firewalls.
- File Transfer: Utilize SCP (Secure Copy Protocol) or SFTP (SSH File Transfer Protocol) for secure file transfers.
- Automation: Integrate SSH into scripts and automation tools for streamlined device management.
These features make SSH an invaluable tool for managing complex IoT networks and automating routine tasks.
Tools and Resources for SSH
Enhancing Your SSH Experience
Several tools and resources can help you get the most out of SSH for IoT device management:
- OpenSSH: A widely-used, open-source SSH implementation available on most Linux and macOS systems. PuTTY: A popular SSH client for Windows users, offering a user-friendly interface and advanced features.
- SSH Keys: Tools like ssh-keygen can help you generate and manage public-private key pairs for secure authentication.
For more information on SSH and its applications, consult the official documentation and community forums for additional resources.
Conclusion
In this comprehensive SSH remote IoT device tutorial, we've covered everything you need to know about using SSH for IoT management. From setting up SSH on your devices to troubleshooting common issues, you now have the knowledge and tools to manage your IoT network securely and efficiently.
We encourage you to explore the advanced features of SSH and experiment with automation and scripting to further enhance your IoT management capabilities. Don't forget to follow security best practices to protect your devices and data.
Feel free to leave a comment or question below, and consider sharing this tutorial with others who may find it helpful. For more in-depth guides and resources, explore our other articles on IoT and network management.
Stay tuned for more updates and tutorials on SSH and IoT technology!