In today's interconnected world, the ability to access IoT devices and Raspberry Pi remotely is becoming increasingly important. Whether you're managing a network of smart devices or running a home automation system, remote access through SSH offers a secure and efficient solution. This article will explore the concept of free remote access for IoT devices and Raspberry Pi, providing you with the knowledge and tools to implement it effectively.
Remote access allows users to control and monitor their devices from anywhere in the world, enhancing productivity and convenience. With the rise of IoT devices and the popularity of Raspberry Pi, understanding how to set up secure remote access has become essential for both hobbyists and professionals.
In this comprehensive guide, we'll walk you through everything you need to know about free remote access for IoT devices and Raspberry Pi using SSH. From setting up the necessary configurations to troubleshooting common issues, this article aims to empower you with the expertise to manage your devices remotely with confidence.
Read also:Everything You Need To Know About Hd Movies A Comprehensive Guide
Table of Contents
- Introduction to SSH
- Why Remote Access Matters
- Setting Up SSH on Raspberry Pi
- Securing Your SSH Connection
- Connecting to IoT Devices
- Troubleshooting Common Issues
- Alternative Tools for Remote Access
- Best Practices for Remote Access
- Frequently Asked Questions
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication between devices over an unsecured network. It is widely used for remote access and management of servers, IoT devices, and other networked systems. SSH encrypts all data transmitted between the client and server, ensuring confidentiality and integrity.
When it comes to IoT devices and Raspberry Pi, SSH provides a reliable method for remote access. By using SSH, users can securely log in to their devices, execute commands, transfer files, and manage configurations without being physically present.
Key Features of SSH
- Encryption of data during transmission
- Authentication mechanisms to ensure secure connections
- Support for multiple protocols, including SFTP for file transfers
- Compatibility with a wide range of devices and operating systems
Why Remote Access Matters
In today's digital landscape, remote access is no longer a luxury but a necessity. For IoT devices and Raspberry Pi users, the ability to access and manage devices remotely offers numerous advantages:
1. Increased Productivity
With remote access, users can perform tasks such as monitoring sensor data, updating software, and troubleshooting issues without needing to be physically present. This saves time and enhances overall productivity.
2. Cost Savings
Eliminating the need for on-site visits can lead to significant cost savings, especially for businesses managing large networks of IoT devices. Free remote access solutions like SSH further reduce expenses by avoiding the need for proprietary software.
3. Enhanced Flexibility
Remote access allows users to manage their devices from anywhere in the world, providing unparalleled flexibility. Whether you're at home, in the office, or traveling, you can stay connected to your IoT devices and Raspberry Pi.
Read also:What Is Paige From Young Sheldons Real Name Discover The Actress Behind The Character
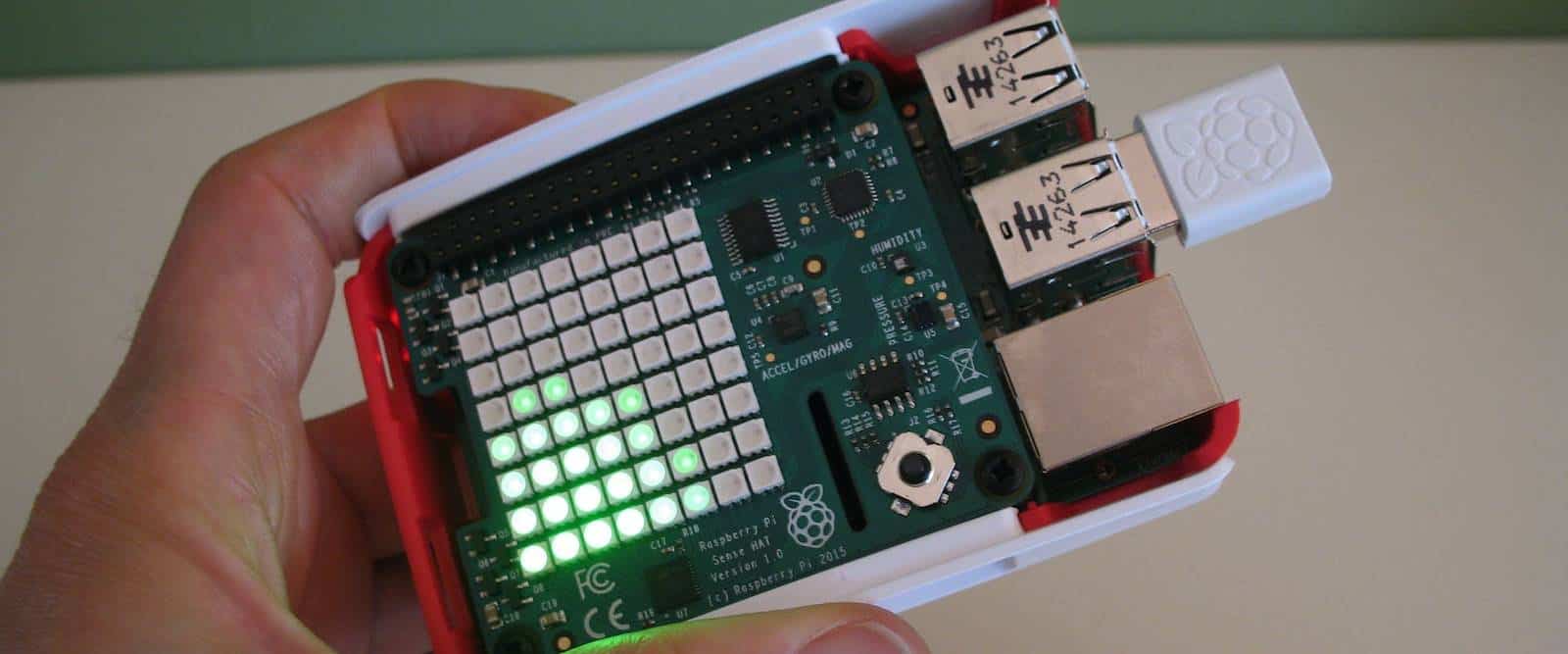
Setting Up SSH on Raspberry Pi
Setting up SSH on a Raspberry Pi is a straightforward process that can be completed in just a few steps. Follow the instructions below to enable SSH on your Raspberry Pi:
Step 1: Enable SSH
By default, SSH is disabled on newer versions of Raspberry Pi OS. To enable it, follow these steps:
- Boot your Raspberry Pi and log in to the desktop environment.
- Open the Raspberry Pi Configuration tool from the Preferences menu.
- Select the "Interfaces" tab and set SSH to "Enabled."
Step 2: Find Your Raspberry Pi's IP Address
To connect to your Raspberry Pi via SSH, you'll need its IP address. You can find this by running the following command in the terminal:
hostname -I
Step 3: Connect Using an SSH Client
Once SSH is enabled and you have the IP address, you can connect to your Raspberry Pi using an SSH client. Popular options include:
- Terminal (Mac/Linux)
- PuTTY (Windows)
Securing Your SSH Connection
While SSH provides a secure method for remote access, it's essential to take additional steps to protect your devices from unauthorized access:
1. Change the Default SSH Port
By changing the default SSH port (22) to a custom port, you can reduce the risk of automated attacks. Edit the SSH configuration file using the following command:
sudo nano /etc/ssh/sshd_config
Locate the line that reads "Port 22" and change it to your desired port number. Restart the SSH service for the changes to take effect:
sudo systemctl restart ssh
2. Use Strong Passwords or Key-Based Authentication
Ensure that your SSH credentials are secure by using strong passwords or implementing key-based authentication. Key-based authentication eliminates the need for passwords, providing an additional layer of security.
3. Limit User Access
Restrict SSH access to specific users or groups to minimize the risk of unauthorized access. Modify the SSH configuration file to include the following line:
AllowUsers your_username
Connecting to IoT Devices
SSH can also be used to connect to IoT devices, enabling remote management and monitoring. The process is similar to setting up SSH on a Raspberry Pi, with some variations depending on the device:
Step 1: Check Device Compatibility
Ensure that your IoT device supports SSH and has the necessary software installed. Most modern IoT devices come with SSH pre-installed, but older models may require manual configuration.
Step 2: Configure Network Settings
Set up your IoT device to connect to your local network. This may involve configuring Wi-Fi settings or assigning a static IP address.
Step 3: Connect via SSH
Use an SSH client to connect to your IoT device using its IP address and login credentials. Once connected, you can execute commands, transfer files, and manage configurations as needed.
Troubleshooting Common Issues
While SSH is a robust protocol, users may encounter issues during setup or connection. Below are some common problems and their solutions:
1. Connection Refused
If you receive a "connection refused" error, ensure that SSH is enabled on your device and that the correct IP address and port number are being used.
2. Authentication Failed
Double-check your login credentials and ensure that the correct username and password are being entered. If you're using key-based authentication, verify that the keys are properly configured.
3. Timeout Errors
Timeout errors may occur due to network issues or firewall restrictions. Check your network settings and ensure that the necessary ports are open.
Alternative Tools for Remote Access
While SSH is a popular choice for remote access, several alternative tools offer additional features and functionality:
1. VNC (Virtual Network Computing)
VNC allows users to remotely access the graphical interface of their devices, making it ideal for tasks that require visual interaction.
2. TeamViewer
TeamViewer is a user-friendly remote access tool that supports both command-line and graphical interfaces. It also includes features such as file transfer and collaboration.
3. ngrok
ngrok provides an easy way to expose local servers to the internet, enabling remote access without the need for port forwarding or static IP addresses.
Best Practices for Remote Access
To ensure a secure and reliable remote access experience, follow these best practices:
1. Regularly Update Software
Keep your devices and software up to date to protect against vulnerabilities and exploits.
2. Monitor Access Logs
Regularly review your SSH access logs to detect and respond to suspicious activity.
3. Use a Firewall
Implement a firewall to restrict access to your devices and protect against unauthorized connections.
Frequently Asked Questions
Q: Is SSH free to use?
A: Yes, SSH is an open-source protocol and can be used free of charge.
Q: Can SSH be used on all IoT devices?
A: While SSH is widely supported, not all IoT devices have the necessary software installed. Check the device's documentation for compatibility.
Q: How can I secure my SSH connection?
A: Use strong passwords, implement key-based authentication, and configure firewall rules to enhance SSH security.
Conclusion
Free remote access for IoT devices and Raspberry Pi through SSH offers a secure and efficient way to manage your devices from anywhere in the world. By following the steps outlined in this article, you can set up and secure your SSH connections with confidence.
We encourage you to share your experiences and ask questions in the comments section below. Additionally, explore other articles on our site to further enhance your knowledge of IoT and remote access technologies.