In today's hyper-connected world, secure P2P IoT has become a critical topic for individuals, businesses, and governments alike. The Internet of Things (IoT) is revolutionizing how devices communicate and interact, and peer-to-peer (P2P) networking is at the forefront of this transformation. However, ensuring the security of these networks is paramount as they become more integrated into our daily lives.
As billions of devices come online, the need for secure P2P IoT solutions has never been more urgent. Traditional centralized systems are often inefficient and vulnerable to attacks, making P2P architectures an attractive alternative. This article explores the intricacies of secure P2P IoT, highlighting its benefits, challenges, and future potential.
Whether you're a tech enthusiast, a business owner, or a developer, understanding secure P2P IoT is essential. This article will provide you with a comprehensive overview of the technology, its applications, and the security measures necessary to protect your data and devices in the modern digital landscape.
Read also:Discover The World Of Yogi Hit A Comprehensive Guide
Table of Contents
- Introduction to P2P IoT
- Importance of Secure P2P IoT
- Benefits of P2P IoT
- Challenges in Secure P2P IoT
- Security Measures for P2P IoT
- Emerging Technologies in Secure P2P IoT
- Use Cases of Secure P2P IoT
- Industry Standards for P2P IoT
- Future of Secure P2P IoT
- Conclusion and Call to Action
Introduction to P2P IoT
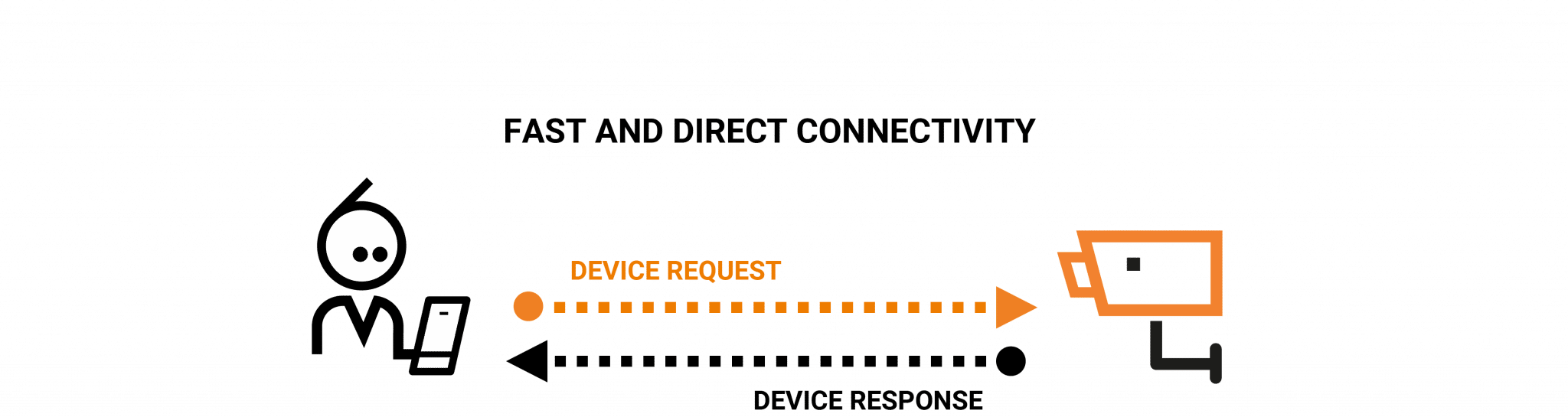
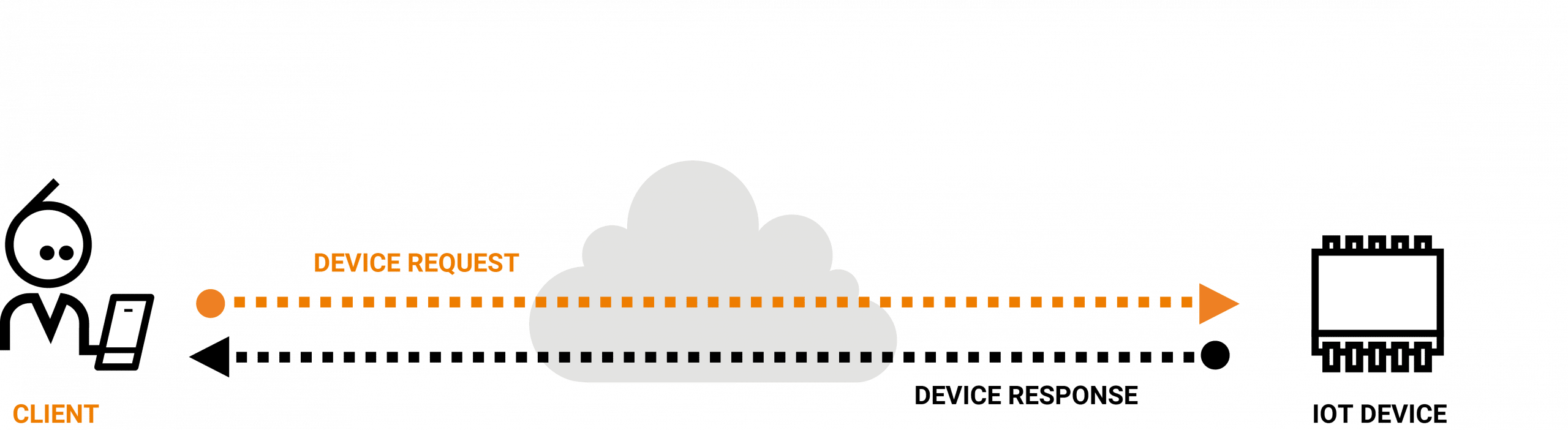
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that allow them to exchange data. Peer-to-peer (P2P) networking, on the other hand, is a decentralized architecture where devices communicate directly without relying on a central server. Secure P2P IoT combines these two concepts, enabling devices to interact securely and efficiently.
P2P IoT offers several advantages over traditional client-server models, including reduced latency, improved scalability, and enhanced resilience. However, ensuring the security of these networks is crucial, as they often handle sensitive data and critical operations.
In this section, we will explore the fundamental principles of P2P IoT and its role in modern technology ecosystems. We will also discuss why security is a top priority in P2P IoT implementations.
Key Features of P2P IoT
- Decentralized architecture
- Direct device communication
- Improved efficiency and reliability
- Scalability for large-scale networks
Importance of Secure P2P IoT
As the number of connected devices continues to grow, the importance of secure P2P IoT cannot be overstated. According to a report by Gartner, there will be over 25 billion connected devices by 2025. This exponential growth presents both opportunities and challenges, particularly in terms of security.
Secure P2P IoT is vital for protecting sensitive data, ensuring privacy, and preventing cyberattacks. In industries such as healthcare, finance, and smart cities, the consequences of a security breach can be catastrophic. By implementing robust security measures, organizations can safeguard their networks and maintain trust with users.
This section will delve into the reasons why secure P2P IoT is critical for modern applications and the potential risks associated with insecure implementations.
Read also:Comprehensive Guide To Technology Support In Jackson Wy Your Ultimate Solution
Statistics on IoT Security
- 70% of IoT devices have known vulnerabilities, according to a Symantec study.
- IoT-related cyberattacks increased by 300% in 2020, as reported by F-Secure.
- By 2025, the global IoT security market is expected to reach $30 billion, driven by the need for secure P2P IoT solutions.
Benefits of P2P IoT
P2P IoT offers numerous advantages over traditional centralized architectures. Some of the key benefits include:
- Reduced Latency: Devices can communicate directly, eliminating the need for intermediaries and reducing delays.
- Improved Scalability: P2P networks can handle large numbers of devices without compromising performance.
- Enhanced Resilience: Decentralized systems are less vulnerable to single points of failure, making them more reliable.
- Cost Efficiency: P2P IoT reduces the need for expensive infrastructure and maintenance costs.
These benefits make P2P IoT an attractive option for a wide range of applications, from smart homes to industrial automation. However, realizing these advantages requires careful consideration of security measures.
Applications of P2P IoT
P2P IoT is being used in various industries, including:
- Smart cities
- Healthcare
- Supply chain management
- Industrial automation
Challenges in Secure P2P IoT
While P2P IoT offers many benefits, it also presents several challenges, particularly in terms of security. Some of the key challenges include:
- Data Privacy: Protecting sensitive information exchanged between devices is a major concern.
- Cybersecurity Threats: P2P IoT networks are vulnerable to attacks such as denial-of-service (DoS) and man-in-the-middle (MITM) attacks.
- Device Authentication: Ensuring that only authorized devices can access the network is crucial for maintaining security.
- Scalability Issues: As the number of devices grows, maintaining security and performance can become challenging.
This section will examine these challenges in detail and discuss potential solutions for overcoming them.
Common Security Threats in P2P IoT
Some of the most common security threats in P2P IoT include:
- Malware infections
- Unauthorized access
- Data breaches
- Network congestion
Security Measures for P2P IoT
To address the security challenges of P2P IoT, several measures can be implemented. These include:
- Encryption: Encrypting data transmitted between devices ensures confidentiality and integrity.
- Authentication: Implementing strong authentication mechanisms helps verify the identity of devices.
- Firewalls and Intrusion Detection Systems: These tools can detect and prevent unauthorized access to the network.
- Regular Updates: Keeping software and firmware up to date is essential for addressing vulnerabilities.
By adopting these security measures, organizations can significantly enhance the security of their P2P IoT networks.
Best Practices for Secure P2P IoT
Some best practices for securing P2P IoT networks include:
- Using strong encryption protocols
- Implementing multi-factor authentication
- Regularly monitoring network activity
- Conducting security audits
Emerging Technologies in Secure P2P IoT
Several emerging technologies are shaping the future of secure P2P IoT. These include:
- Blockchain: Blockchain technology can provide secure and transparent transaction records for P2P IoT networks.
- Artificial Intelligence (AI): AI can be used to detect anomalies and potential threats in real-time.
- Edge Computing: Edge computing allows data processing to occur closer to the source, reducing latency and improving security.
- Quantum Cryptography: Quantum cryptography offers advanced encryption techniques that are resistant to quantum computing attacks.
This section will explore these technologies and their potential impact on secure P2P IoT.
Advantages of Blockchain in P2P IoT
Blockchain technology offers several advantages for secure P2P IoT, including:
- Decentralized trust
- Immutable transaction records
- Enhanced security
Use Cases of Secure P2P IoT
Secure P2P IoT has numerous real-world applications across various industries. Some of the most prominent use cases include:
- Smart Cities: P2P IoT can be used to optimize traffic management, energy consumption, and public services.
- Healthcare: Secure P2P IoT enables remote patient monitoring and secure data sharing between healthcare providers.
- Supply Chain Management: P2P IoT can improve transparency and efficiency in supply chains by tracking goods in real-time.
- Industrial Automation: Secure P2P IoT can enhance productivity and safety in manufacturing environments.
This section will provide detailed examples of how secure P2P IoT is being implemented in these industries.
Case Study: Smart Cities
One of the most promising applications of secure P2P IoT is in smart cities. By connecting devices such as traffic lights, parking meters, and environmental sensors, cities can improve efficiency and sustainability. For example, a study by McKinsey found that smart city technologies could reduce traffic congestion by up to 20%.
Industry Standards for P2P IoT
Several industry standards have been developed to ensure the security and interoperability of P2P IoT networks. These include:
- IEEE 802.15.4: A standard for low-power wireless communication in IoT devices.
- MQTT (Message Queuing Telemetry Transport): A lightweight protocol for IoT messaging.
- CoAP (Constrained Application Protocol): A protocol designed for resource-constrained devices.
- ISO/IEC 27001: A standard for information security management systems.
This section will discuss these standards and their role in promoting secure P2P IoT.
Why Standards Matter
Industry standards are crucial for ensuring compatibility, security, and reliability in P2P IoT networks. By adhering to these standards, organizations can avoid vendor lock-in and ensure that their devices can communicate seamlessly with others.
Future of Secure P2P IoT
The future of secure P2P IoT looks promising, with continued advancements in technology and increasing adoption across industries. As more devices become connected, the need for secure and efficient communication will only grow. Emerging technologies such as blockchain, AI, and quantum cryptography will play a key role in shaping the future of P2P IoT.
However, challenges such as data privacy, cybersecurity threats, and scalability issues will need to be addressed to fully realize the potential of secure P2P IoT. Collaboration between industry stakeholders, governments, and researchers will be essential in driving innovation and ensuring the security of these networks.
This section will explore the future trends and opportunities in secure P2P IoT and discuss how organizations can prepare for the next wave of innovation.
Predictions for Secure P2P IoT
- Increased adoption of blockchain for secure transactions
- Advancements in AI-driven security solutions
- Growth of edge computing for real-time data processing
- Development of quantum-resistant encryption techniques