As technology continues to evolve, the Internet of Things (IoT) has become an integral part of modern living and business operations. However, managing IoT devices behind a firewall is a crucial task that requires careful planning and execution. In this article, we will delve into the strategies, tools, and techniques needed to effectively control IoT devices while maintaining robust security measures.
Controlling IoT devices behind a firewall can seem daunting, but with the right knowledge and tools, it becomes manageable. This guide aims to provide actionable insights for IT professionals, system administrators, and enthusiasts looking to enhance their IoT management skills.
Whether you're securing smart home devices or managing industrial IoT solutions, understanding how to control IoT devices behind firewalls is essential. This article will explore various aspects of IoT security, including best practices, potential risks, and advanced configurations. Let's dive in!
Read also:9x Doctor The Ultimate Guide To Understanding And Choosing The Right Medical Professional
Understanding IoT and Its Security Challenges
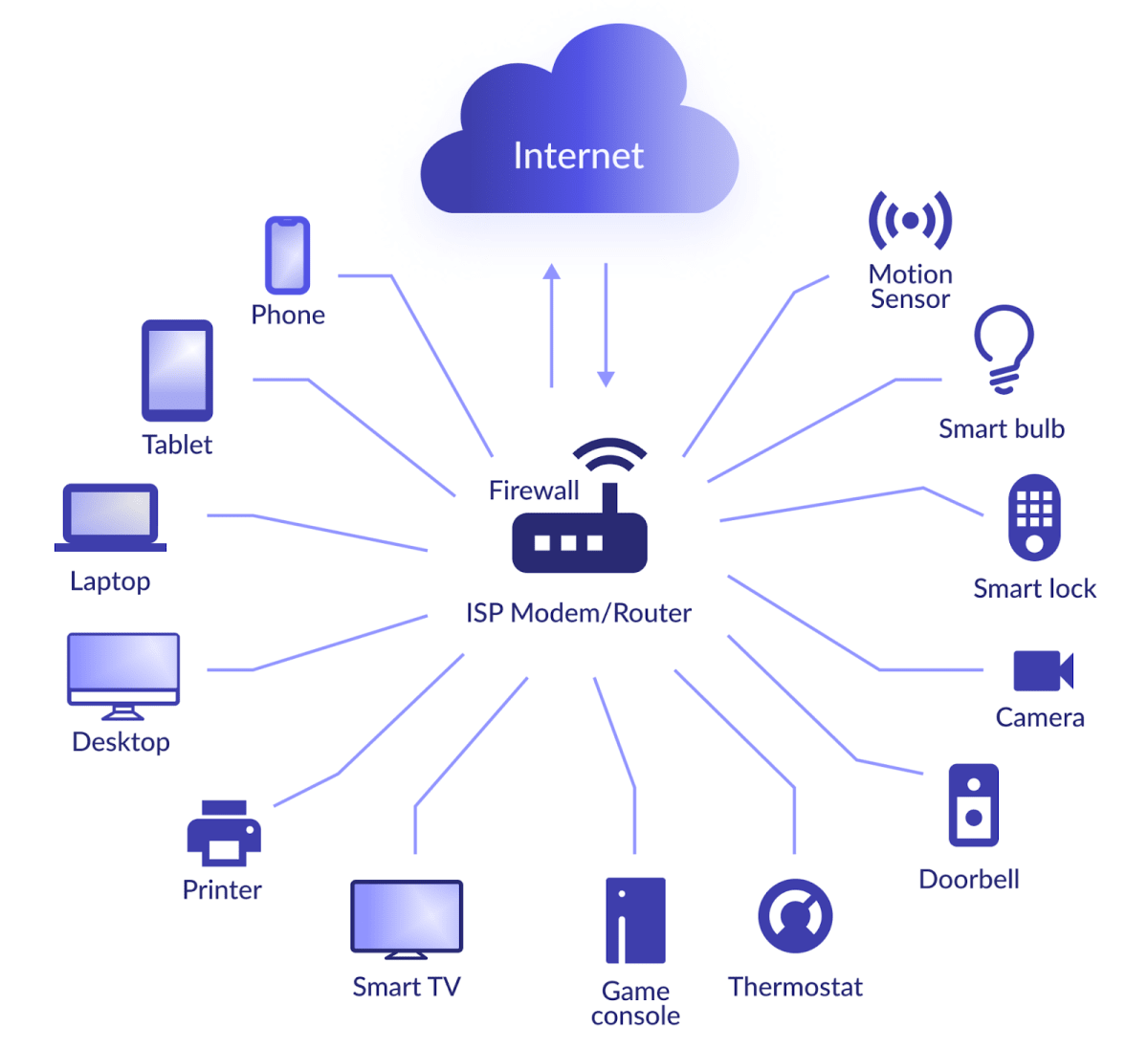
IoT refers to a network of interconnected devices that communicate and exchange data over the internet. While IoT offers numerous benefits, such as increased efficiency and automation, it also presents significant security challenges. One of the primary concerns is controlling these devices while ensuring they remain protected from external threats.
What Makes IoT Security Unique?
The unique aspects of IoT security stem from the diversity of devices and protocols involved. Below are some key factors:
- Device heterogeneity: IoT devices come in various shapes, sizes, and functionalities, making it challenging to implement a uniform security strategy.
- Network complexity: IoT networks often span multiple environments, including home, office, and cloud, which complicates management and security.
- Resource constraints: Many IoT devices have limited processing power and memory, restricting the use of traditional security measures.
Why Control IoT Devices Behind a Firewall?
A firewall acts as a barrier between your internal network and the outside world, filtering traffic to prevent unauthorized access. Controlling IoT devices behind a firewall ensures that only trusted connections can interact with these devices, reducing the risk of cyberattacks.
Key Benefits of Using Firewalls for IoT
Here are some advantages of controlling IoT devices behind firewalls:
- Enhanced security: Firewalls block malicious traffic and prevent unauthorized access to your IoT devices.
- Granular control: You can define specific rules and policies to govern how IoT devices interact with the network.
- Improved monitoring: Firewalls provide detailed logs and reports, allowing you to track device activity and detect anomalies.
Best Practices for Controlling IoT Devices Behind Firewalls
Implementing best practices is essential for effective IoT device management. Below are some strategies to consider:
1. Segment Your Network
Network segmentation involves dividing your network into smaller, isolated segments. By placing IoT devices on a separate network segment, you limit their exposure to the rest of your infrastructure.
Read also:New Year Ullu Web Series A Captivating Journey Into Indias Trendiest Digital Entertainment
2. Use Strong Authentication
Ensure that all IoT devices require strong authentication before accessing the network. This can include multi-factor authentication (MFA) and certificate-based authentication.
3. Regularly Update Firmware
Keep your IoT devices up to date with the latest firmware to address security vulnerabilities and improve performance. Manufacturers frequently release patches and updates to enhance device security.
4. Monitor Device Activity
Implement monitoring tools to track IoT device activity and detect any suspicious behavior. Real-time alerts can help you respond quickly to potential threats.
Common Challenges in Managing IoT Devices Behind Firewalls
Despite the benefits, managing IoT devices behind firewalls comes with its own set of challenges. Below are some common obstacles:
1. Limited Device Capabilities
Many IoT devices lack the necessary resources to support advanced security features, making it difficult to implement comprehensive protection.
2. Complex Configurations
Configuring firewalls to accommodate the diverse range of IoT devices can be a complex and time-consuming process.
3. Balancing Security and Usability
Striking the right balance between security and usability is crucial. Overly restrictive firewall rules can hinder device functionality, while lax rules increase the risk of attacks.
Tools and Technologies for Managing IoT Devices Behind Firewalls
Several tools and technologies can help streamline the process of controlling IoT devices behind firewalls. Below are some popular options:
1. Unified Threat Management (UTM) Solutions
UTM solutions combine multiple security features, such as firewalls, intrusion detection, and antivirus, into a single platform. This simplifies management and enhances protection.
2. IoT-Specific Firewalls
Some firewalls are specifically designed to handle the unique requirements of IoT devices. These solutions offer advanced features like deep packet inspection and protocol analysis.
3. Cloud-Based Management Platforms
Cloud-based platforms provide centralized management of IoT devices, enabling you to configure firewalls and other security settings from a single interface.
Data and Statistics on IoT Security
To emphasize the importance of controlling IoT devices behind firewalls, consider the following statistics:
- According to a report by Gartner, over 25% of identified attacks on enterprise systems will involve IoT by 2025.
- A study by Symantec found that IoT devices are targeted in 67% of all malware attacks.
- Research by Palo Alto Networks revealed that 98% of IoT device traffic is unencrypted, making it vulnerable to interception.
Case Studies: Successful IoT Device Management
Real-world examples can provide valuable insights into effective IoT device management. Below are two case studies:
1. Smart City Implementation
A major city implemented IoT devices to monitor traffic and optimize public transportation. By using firewalls and network segmentation, they successfully reduced cyberattacks by 70%.
2. Industrial IoT Deployment
A manufacturing company deployed IoT sensors to monitor equipment performance. By integrating firewalls and advanced monitoring tools, they improved operational efficiency while maintaining robust security.
Future Trends in IoT Device Management
The landscape of IoT device management is continually evolving. Below are some emerging trends to watch:
1. Artificial Intelligence (AI) Integration
AI-powered tools can analyze vast amounts of data to detect patterns and anomalies, enhancing IoT device management and security.
2. Edge Computing
Edge computing reduces latency and improves performance by processing data closer to the source, making it ideal for IoT applications.
3. Blockchain Technology
Blockchain offers decentralized and tamper-proof data storage, providing a new level of security for IoT devices.
Conclusion
Controlling IoT devices behind firewalls is a critical aspect of modern IT management. By understanding the challenges, implementing best practices, and leveraging advanced tools and technologies, you can ensure the security and functionality of your IoT devices.
We encourage you to take action by implementing the strategies discussed in this article. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our website for more valuable insights.
Table of Contents
- Understanding IoT and Its Security Challenges
- Why Control IoT Devices Behind a Firewall?
- Best Practices for Controlling IoT Devices Behind Firewalls
- Common Challenges in Managing IoT Devices Behind Firewalls
- Tools and Technologies for Managing IoT Devices Behind Firewalls
- Data and Statistics on IoT Security
- Case Studies: Successful IoT Device Management
- Future Trends in IoT Device Management
- Conclusion