In the era of connected devices, securely connecting remote IoT (Internet of Things) devices using P2P (Peer-to-Peer) technology on a Raspberry Pi has become increasingly important. As more individuals and businesses rely on IoT devices for automation and efficiency, ensuring secure communication between devices is paramount. This article will provide you with an in-depth guide to setting up a secure remote IoT P2P connection on a Raspberry Pi, complete with free download resources.
With the rapid growth of IoT, the need for secure communication has never been more critical. Devices such as smart home appliances, industrial sensors, and wearable gadgets require seamless and protected data exchange. By leveraging P2P technology on a Raspberry Pi, you can create a robust and secure network for your IoT devices without relying on centralized servers.
This guide aims to provide you with actionable insights, practical steps, and expert advice to ensure your IoT setup is both secure and efficient. Whether you're a hobbyist, a professional developer, or a business owner, this article will equip you with the knowledge needed to establish a reliable P2P connection for your IoT devices.
Read also:Matt Cutshall Age Unveiling The Life And Career Of The Rising Star
Table of Contents
- Introduction to Secure IoT Connections
- Raspberry Pi Overview
- Understanding P2P Technology
- Security Challenges in IoT
- Step-by-Step Setup Guide
- Free Resources for Download
- Optimizing Performance
- Common Issues and Troubleshooting
- Best Practices for Security
- Future Trends in IoT Security
- Conclusion
Introduction to Secure IoT Connections
In today's interconnected world, securely connect remote IoT P2P Raspberry Pi has become a necessity for ensuring the safety and reliability of data transmission. IoT devices are vulnerable to cyber threats, and without proper security measures, sensitive information can be compromised. This section will delve into the importance of secure connections and how they impact the overall functionality of IoT networks.
Why Security Matters
- Prevents unauthorized access to devices.
- Protects sensitive data from being intercepted.
- Ensures the integrity of communication between devices.
By implementing secure protocols, you can safeguard your IoT ecosystem against potential breaches and ensure uninterrupted operation.
Raspberry Pi Overview
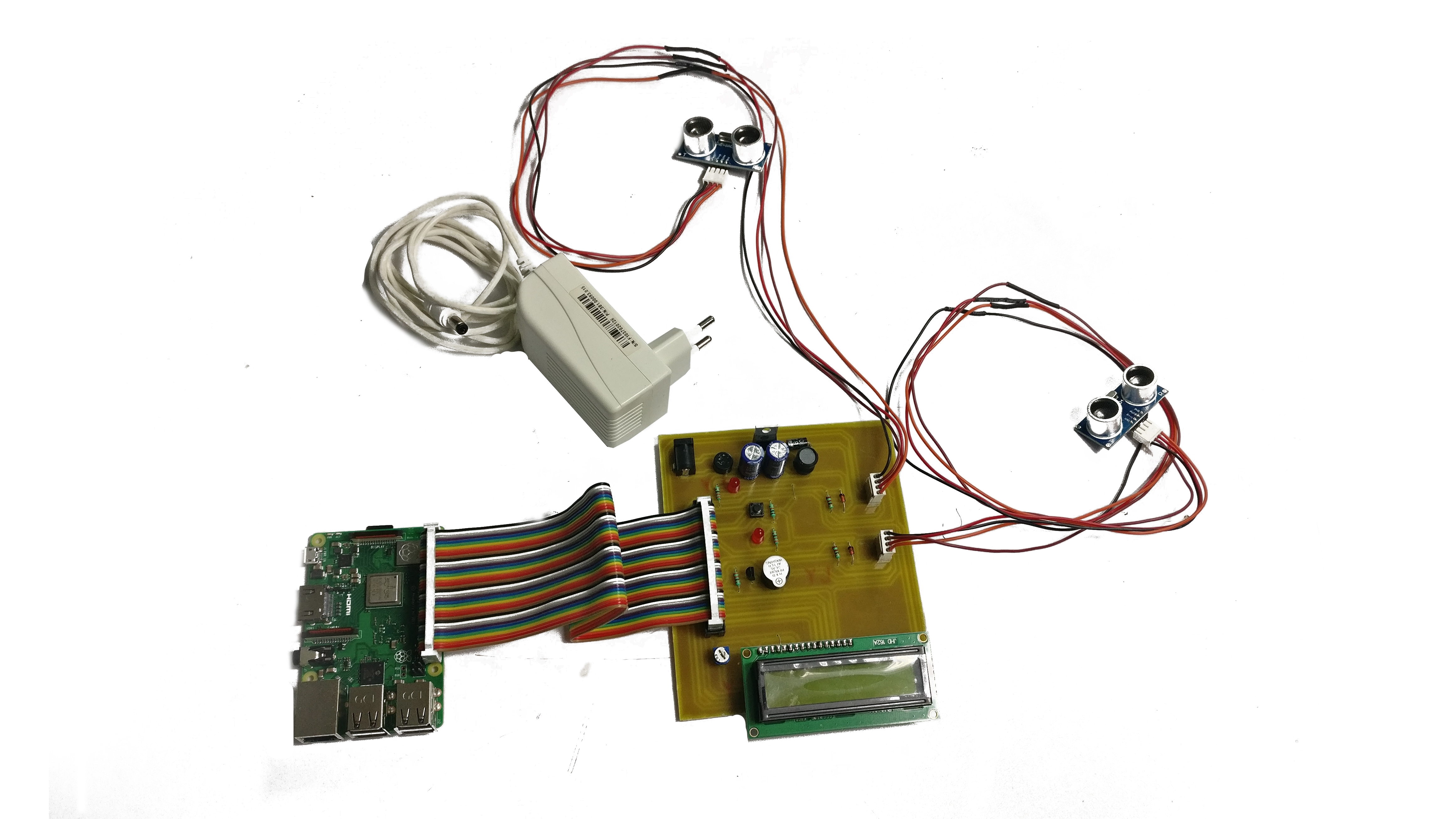
The Raspberry Pi is a versatile, low-cost single-board computer that has gained immense popularity among developers and hobbyists alike. Its compact size and powerful performance make it an ideal platform for running IoT applications. In this section, we will explore the features and capabilities of the Raspberry Pi that make it suitable for securely connect remote IoT P2P.
Key Features of Raspberry Pi
- Compact and energy-efficient design.
- Supports multiple operating systems, including Linux-based distributions.
- Equipped with GPIO pins for interfacing with external devices.
These features enable the Raspberry Pi to act as a reliable gateway for IoT devices, facilitating secure and efficient communication.
Understanding P2P Technology
P2P technology eliminates the need for centralized servers by allowing devices to communicate directly with each other. This decentralized approach offers several advantages, including reduced latency, improved scalability, and enhanced security. In the context of IoT, securely connect remote IoT P2P Raspberry Pi ensures that devices can exchange data without relying on third-party infrastructure.
Benefits of P2P in IoT
- Enhanced privacy and security.
- Lower operational costs due to reduced reliance on cloud services.
- Improved resilience against network failures.
By adopting P2P technology, you can create a more robust and secure IoT network that meets the demands of modern applications.
Read also:Annaxnasty The Rising Star In The Digital Age
Security Challenges in IoT
Despite the numerous benefits of IoT, security remains a significant concern. Devices connected to the internet are susceptible to various threats, including hacking, malware, and data breaches. To securely connect remote IoT P2P Raspberry Pi, it is essential to address these challenges proactively. This section will highlight the common security issues faced in IoT networks and provide solutions to mitigate them.
Common IoT Security Threats
- Unauthorized access to devices.
- Data interception and eavesdropping.
- Denial-of-Service (DoS) attacks.
Implementing robust security measures, such as encryption and authentication protocols, can significantly reduce the risk of these threats.
Step-by-Step Setup Guide
This section will walk you through the process of setting up a secure remote IoT P2P connection on a Raspberry Pi. By following these steps, you can ensure that your IoT devices communicate securely and efficiently.
Step 1: Install the Operating System
Begin by installing a suitable operating system on your Raspberry Pi. Raspbian, a Debian-based distribution, is a popular choice due to its stability and extensive community support.
Step 2: Configure Network Settings
Set up your Raspberry Pi to connect to your local network. Ensure that the device has a static IP address to facilitate consistent communication.
Step 3: Implement Security Protocols
Install and configure encryption and authentication tools to secure your IoT network. Tools such as OpenSSL and SSH can help protect your data from unauthorized access.
Step 4: Establish P2P Connection
Use P2P software, such as WebRTC or libp2p, to enable direct communication between IoT devices. These tools simplify the process of creating secure connections without the need for centralized servers.
Free Resources for Download
To assist you in setting up your secure remote IoT P2P Raspberry Pi, we have compiled a list of free resources that you can download. These resources include software tools, tutorials, and documentation to help you get started.
Recommended Downloads
- Raspbian OS Image
- libp2p Library
- OpenSSL Documentation
These resources are available from reputable sources and are regularly updated to ensure compatibility and security.
Optimizing Performance
Once your secure remote IoT P2P Raspberry Pi setup is complete, it is essential to optimize its performance for optimal functionality. This section will provide tips and techniques to enhance the efficiency of your IoT network.
Performance Optimization Tips
- Regularly update your software and firmware to ensure compatibility and security.
- Monitor network traffic to identify and resolve bottlenecks.
- Implement load balancing techniques to distribute traffic evenly across devices.
By following these tips, you can ensure that your IoT network operates smoothly and efficiently.
Common Issues and Troubleshooting
Even with careful planning and execution, issues may arise during the setup and operation of your secure remote IoT P2P Raspberry Pi. This section will address common problems and provide solutions to help you troubleshoot effectively.
Troubleshooting Guide
- Connection Issues: Check network settings and ensure all devices are properly configured.
- Performance Problems: Analyze system logs to identify and resolve performance bottlenecks.
- Security Breaches: Regularly audit your network for vulnerabilities and apply necessary patches.
By addressing these issues promptly, you can maintain the stability and security of your IoT network.
Best Practices for Security
To ensure the long-term security of your IoT network, it is crucial to follow best practices. This section will outline key strategies to enhance the security of your secure remote IoT P2P Raspberry Pi setup.
Security Best Practices
- Use strong passwords and implement two-factor authentication.
- Regularly back up your data to prevent loss in case of a security breach.
- Stay informed about the latest security trends and updates in the IoT industry.
By adhering to these best practices, you can minimize the risk of security breaches and ensure the protection of your IoT devices.
Future Trends in IoT Security
The field of IoT security is constantly evolving, with new technologies and strategies emerging to address existing challenges. This section will explore the future trends in IoT security and their potential impact on securely connect remote IoT P2P Raspberry Pi.
Emerging Technologies
- Blockchain for decentralized security.
- Artificial Intelligence for threat detection and response.
- Quantum Cryptography for enhanced encryption.
By staying ahead of these trends, you can future-proof your IoT network and ensure its continued security and functionality.
Conclusion
In conclusion, securely connect remote IoT P2P Raspberry Pi is essential for creating a robust and reliable IoT network. By following the steps outlined in this guide, you can establish a secure connection that protects your devices and data from potential threats. Remember to regularly update your software, monitor your network, and adhere to best practices to ensure the long-term security of your IoT setup.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, we can build a safer and more connected world.