In today's digital era, remote IoT VPC SSH on Windows 10 has become a crucial skill for IT professionals and tech enthusiasts alike. Whether you're managing IoT devices or securing your network, understanding how to set up and maintain remote connections is essential. This guide will walk you through everything you need to know about remote IoT VPC SSH on Windows 10, from the basics to advanced configurations.
As technology evolves, the demand for secure remote access solutions continues to grow. Remote IoT VPC SSH on Windows 10 offers a powerful way to manage and monitor devices across networks securely. This article aims to provide a detailed exploration of this topic, ensuring you gain the knowledge and skills necessary to implement it effectively.
This guide is designed for both beginners and advanced users who want to deepen their understanding of remote IoT VPC SSH on Windows 10. By the end of this article, you'll be equipped with practical insights, step-by-step instructions, and expert tips to enhance your remote connectivity experience.
Read also:How Old Is Billy Bob Thornton A Comprehensive Look At His Age Career And Life
Table of Contents
Introduction to Remote IoT VPC SSH on Windows 10
Benefits of Using Remote IoT VPC SSH
Setting Up Remote IoT VPC SSH on Windows 10
Securing Your Remote IoT VPC SSH Connection
Common Issues and Troubleshooting
Optimizing Remote IoT VPC SSH Performance
Read also:Discover The Life And Journey Of Elisabeth Anne Carell Whatrsquos Her Age
Essential Tools for Managing Remote IoT VPC SSH
Integrating IoT Devices with VPC SSH
The Future of Remote IoT VPC SSH
Choosing the Right VPC Configuration
Best Practices for IoT Device Management
Automation in Remote IoT VPC SSH
Introduction to Remote IoT VPC SSH on Windows 10
Remote IoT VPC SSH on Windows 10 combines the power of IoT devices, virtual private clouds (VPC), and Secure Shell (SSH) protocols to create a robust remote access solution. This setup allows users to securely manage and monitor IoT devices from anywhere in the world. Understanding the fundamentals of this technology is the first step toward mastering it.
SSH, or Secure Shell, is a cryptographic network protocol that ensures secure communication over unsecured networks. When integrated with IoT devices and VPC, it provides an additional layer of security and control. Windows 10 users can leverage built-in features and third-party tools to set up this configuration efficiently.
This section will explore the key components of remote IoT VPC SSH, including its architecture, benefits, and potential applications. Whether you're a network administrator or an IoT enthusiast, this introduction will lay the foundation for more advanced topics.
Benefits of Using Remote IoT VPC SSH
Implementing remote IoT VPC SSH on Windows 10 offers numerous advantages. Here are some of the key benefits:
- Enhanced Security: SSH encrypts all data transmitted between devices, ensuring confidentiality and integrity.
- Scalability: VPC allows you to scale your network infrastructure seamlessly, accommodating growing numbers of IoT devices.
- Flexibility: Remote access enables you to manage devices from anywhere, improving operational efficiency.
- Cost-Effectiveness: By leveraging existing infrastructure, you can reduce costs associated with physical hardware and maintenance.
These benefits make remote IoT VPC SSH an attractive solution for businesses and individuals seeking secure and efficient remote connectivity.
Setting Up Remote IoT VPC SSH on Windows 10
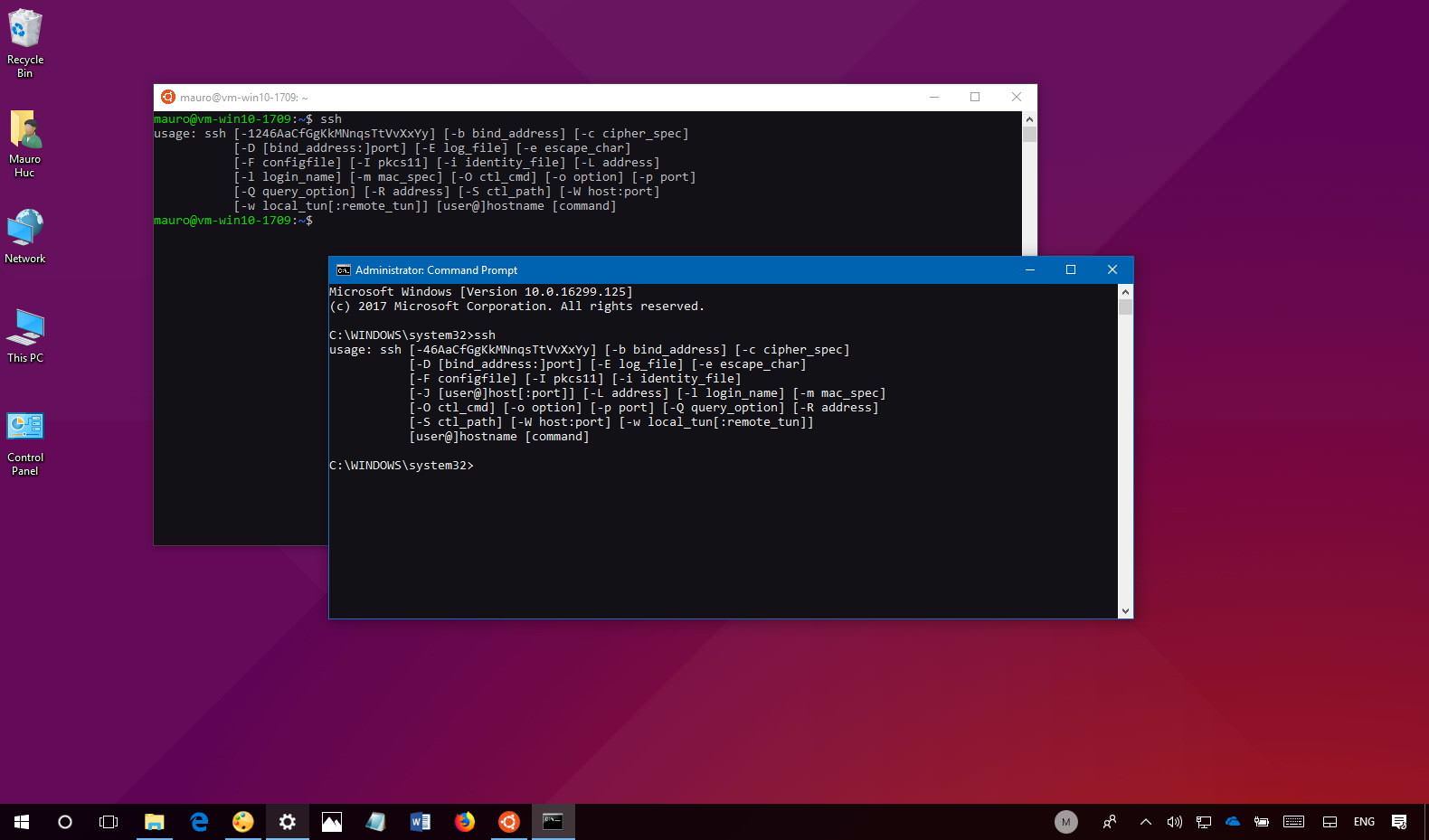
Understanding SSH Basics
Before diving into the setup process, it's important to understand the basics of SSH. SSH operates on port 22 by default and uses public-key cryptography to authenticate users and encrypt data. Familiarizing yourself with these concepts will help you configure your system more effectively.
Step-by-Step Guide
Follow these steps to set up remote IoT VPC SSH on Windows 10:
- Install OpenSSH: Windows 10 includes OpenSSH as an optional feature. Go to Settings > Apps > Optional Features to install it.
- Configure Firewall Settings: Allow SSH traffic through your firewall by creating inbound and outbound rules for port 22.
- Set Up IoT Devices: Ensure your IoT devices are connected to the same network and properly configured for remote access.
- Establish VPC Connection: Use a cloud provider's VPC service to create a secure connection between your local network and IoT devices.
Securing Your Remote IoT VPC SSH Connection
Choosing the Right VPC Configuration
Selecting the appropriate VPC configuration is crucial for maintaining security. Consider factors such as subnet划分, access control lists, and security groups when designing your VPC. These elements help protect your network from unauthorized access and potential threats.
Implementing multi-factor authentication (MFA) and regularly updating your SSH keys are additional measures to enhance security. Staying informed about the latest security practices and vulnerabilities is essential for maintaining a secure remote IoT VPC SSH setup.
Common Issues and Troubleshooting
Troubleshooting Common Errors
Despite careful planning, issues may arise during the setup and operation of remote IoT VPC SSH. Here are some common problems and their solutions:
- Connection Refused: Verify that SSH is enabled and the correct port is open in your firewall settings.
- Authentication Failure: Double-check your SSH keys and ensure they match on both the client and server sides.
- Network Connectivity Issues: Test your network connection and ensure all devices are properly configured within the VPC.
Addressing these issues promptly will help ensure smooth operation of your remote IoT VPC SSH setup.
Optimizing Remote IoT VPC SSH Performance
Optimizing the performance of your remote IoT VPC SSH setup involves several strategies. Consider the following tips:
- Use compression to reduce data transfer times.
- Implement load balancing to distribute traffic across multiple devices.
- Monitor network performance regularly to identify and address bottlenecks.
By optimizing your setup, you can improve the speed and reliability of your remote connections, enhancing overall user experience.
Essential Tools for Managing Remote IoT VPC SSH
Best Practices for IoT Device Management
Several tools are available to simplify the management of remote IoT VPC SSH setups. These include:
- Putty: A popular SSH client for Windows users, offering a user-friendly interface.
- WinSCP: A secure file transfer protocol (SFTP) client that supports SSH connections.
- Cloud Providers' Management Consoles: Tools like AWS Management Console or Azure Portal provide comprehensive VPC management capabilities.
Adopting best practices for IoT device management, such as regular updates and backups, will further enhance the reliability of your setup.
Integrating IoT Devices with VPC SSH
Monitoring Remote Connections
Integrating IoT devices with VPC SSH requires careful planning and execution. Begin by identifying the specific needs of your IoT devices and selecting appropriate VPC configurations. Monitor your connections regularly to ensure they remain secure and stable.
Automation in Remote IoT VPC SSH
Automation can significantly streamline the management of remote IoT VPC SSH setups. Use scripts and automation tools to perform routine tasks, such as updating configurations and monitoring device status. This reduces the workload on administrators and minimizes the risk of human error.
The Future of Remote IoT VPC SSH
As technology continues to evolve, the future of remote IoT VPC SSH looks promising. Advancements in encryption protocols, network infrastructure, and cloud computing will further enhance the capabilities of this technology. Staying updated with the latest trends and innovations will help you leverage these advancements effectively.
Conclusion and Next Steps
Remote IoT VPC SSH on Windows 10 offers a powerful solution for managing and securing IoT devices remotely. By following the guidelines and best practices outlined in this article, you can set up and maintain a robust remote connectivity system. Remember to prioritize security, optimization, and integration when implementing this technology.
We encourage you to share your thoughts and experiences in the comments section below. Your feedback is invaluable in helping us improve our content. Additionally, consider exploring other articles on our site for more insights into technology and networking topics.