In today's interconnected world, the best remote IoT SSH solutions are becoming increasingly essential for businesses and individuals alike. As the Internet of Things (IoT) continues to expand, secure remote access has become a critical need for managing devices and systems efficiently. Whether you're a network administrator or a tech enthusiast, understanding how to leverage SSH for remote IoT access can significantly enhance your operations.
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication over unsecured networks. It provides a robust layer of security for remote device management, making it an indispensable tool in the realm of IoT. This article will delve into the nuances of implementing the best remote IoT SSH solutions, offering practical advice, expert tips, and actionable strategies.
By the end of this guide, you'll have a solid understanding of how to set up and maintain secure SSH connections for IoT devices, ensuring both efficiency and data protection. Let's dive in and explore the possibilities of remote IoT SSH technology.
Read also:Flushed Away Fat Rat The Ultimate Guide To Rodent Control And Prevention
Table of Contents
- Introduction to Remote IoT SSH
- The Importance of Secure IoT Connections
- Understanding SSH Basics
- Setting Up Remote IoT SSH
- Best Tools for Remote IoT SSH
- Enhancing SSH Security
- Common Issues and Troubleshooting
- Scalability Considerations
- Future Trends in IoT SSH
- Conclusion and Next Steps
Introduction to Remote IoT SSH
Remote IoT SSH has emerged as one of the most reliable methods for managing IoT devices from afar. This technology allows users to securely connect to IoT devices over the internet, enabling efficient monitoring, configuration, and troubleshooting. Whether you're managing a fleet of smart sensors or automating industrial processes, SSH provides the necessary tools to ensure secure and seamless communication.
For businesses, the best remote IoT SSH solutions can significantly reduce operational costs while improving productivity. By enabling remote access, companies can eliminate the need for physical presence at device locations, saving both time and resources. Moreover, SSH's robust encryption ensures that sensitive data remains protected from unauthorized access.
Individuals also benefit from remote IoT SSH, as it simplifies the management of personal IoT devices such as smart home systems, wearable tech, and automotive sensors. With SSH, users can maintain control over their devices from anywhere in the world, ensuring that their IoT ecosystems remain functional and secure.
The Importance of Secure IoT Connections
In the era of IoT, security is paramount. As more devices become interconnected, the risk of cyberattacks increases exponentially. Without proper safeguards, IoT networks can become vulnerable to hacking, data breaches, and other malicious activities. This is where the best remote IoT SSH solutions come into play, offering a secure and reliable method for managing IoT devices.
SSH encrypts all data transmitted between devices, ensuring that sensitive information remains confidential. It also authenticates users and devices, preventing unauthorized access to IoT systems. By implementing SSH, organizations and individuals can protect their IoT networks from potential threats while maintaining full control over their devices.
Key Benefits of Secure IoT Connections
- Enhanced data protection through encryption
- Strong user and device authentication
- Reduced risk of cyberattacks and data breaches
- Improved operational efficiency
Understanding SSH Basics
Before diving into the best remote IoT SSH solutions, it's essential to understand the fundamentals of SSH. Developed in the 1990s, SSH was designed to provide secure communication over unsecured networks. Over the years, it has evolved into a powerful tool for remote device management, widely adopted across industries.
Read also:The Rise Of Themaryburke A Comprehensive Guide To Her Influence And Achievements
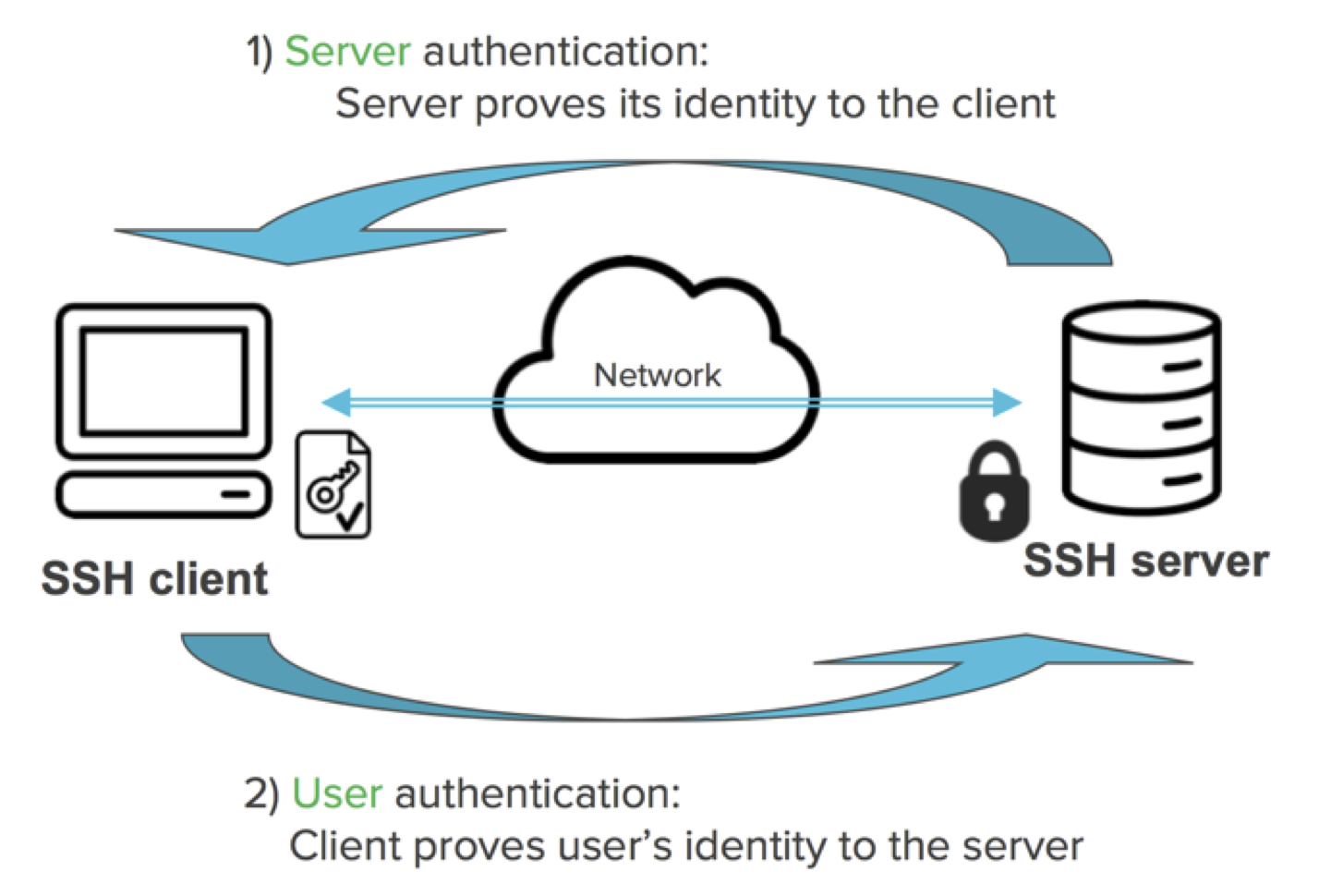
SSH operates on a client-server model, where a client initiates a connection to a server. The connection is encrypted using advanced cryptographic algorithms, ensuring that all data exchanged between the client and server remains secure. Additionally, SSH supports various authentication methods, including passwords, public key authentication, and multi-factor authentication (MFA).
How SSH Works
- Establishes a secure connection between client and server
- Encrypts all data transmitted during the session
- Authenticates users and devices to ensure secure access
Setting Up Remote IoT SSH
Setting up remote IoT SSH involves several steps, from configuring devices to securing connections. Below is a step-by-step guide to help you implement the best remote IoT SSH solutions for your needs.
Step 1: Install SSH Server on IoT Devices
Begin by installing an SSH server on your IoT devices. Most modern IoT platforms, such as Raspberry Pi and Arduino, come with built-in SSH capabilities. If your device doesn't have an SSH server pre-installed, you can easily add one using open-source software like OpenSSH.
Step 2: Configure SSH Settings
Once the SSH server is installed, configure its settings to meet your security requirements. This includes setting up user accounts, enabling encryption, and defining access permissions. Ensure that only authorized users can connect to your IoT devices via SSH.
Step 3: Test the Connection
After configuring SSH, test the connection to ensure everything is working correctly. Use an SSH client, such as PuTTY or OpenSSH, to establish a connection to your IoT device. If the connection is successful, you're ready to start managing your devices remotely.
Best Tools for Remote IoT SSH
Several tools and platforms are available to help you implement the best remote IoT SSH solutions. Below are some of the most popular options:
1. OpenSSH
OpenSSH is an open-source software suite that provides secure communication over unsecured networks. It includes both an SSH server and client, making it an ideal choice for remote IoT SSH.
2. PuTTY
PuTTY is a free and widely-used SSH client for Windows. It offers a user-friendly interface and supports various authentication methods, including public key authentication.
3. SSH.NET
SSH.NET is a .NET library for implementing SSH functionality in applications. It's particularly useful for developers who want to integrate SSH capabilities into their software.
Enhancing SSH Security
While SSH is inherently secure, there are additional steps you can take to further enhance its security. Below are some best practices for securing your remote IoT SSH connections:
1. Use Strong Passwords
Ensure that all user accounts have strong, complex passwords. Avoid using default passwords or easily guessable combinations.
2. Enable Public Key Authentication
Public key authentication provides an extra layer of security by requiring users to possess a private key to access devices. This method is more secure than traditional password-based authentication.
3. Disable Root Login
Disabling root login prevents unauthorized users from gaining administrative access to your IoT devices. Instead, create separate user accounts with limited privileges.
Common Issues and Troubleshooting
Even with the best remote IoT SSH solutions, issues can arise. Below are some common problems and their solutions:
1. Connection Refused
If you receive a "connection refused" error, ensure that the SSH server is running on your IoT device and that the correct IP address and port number are being used.
2. Authentication Failed
Authentication failures typically occur due to incorrect passwords or missing public keys. Double-check your credentials and ensure that all necessary files are present on both the client and server.
3. Slow Connection
Slow connections can be caused by network congestion or insufficient bandwidth. Consider upgrading your network infrastructure or optimizing your SSH settings to improve performance.
Scalability Considerations
As your IoT ecosystem grows, it's important to consider scalability when implementing the best remote IoT SSH solutions. Below are some factors to keep in mind:
1. Device Management
As the number of devices increases, managing them individually can become cumbersome. Consider using centralized management tools to streamline device configuration and monitoring.
2. Network Bandwidth
Ensure that your network has sufficient bandwidth to support all SSH connections. Monitor network performance regularly and make adjustments as needed to maintain optimal speeds.
3. Security Policies
Regularly review and update your security policies to address new threats and vulnerabilities. Implement automated tools to detect and respond to potential security breaches.
Future Trends in IoT SSH
The future of IoT SSH looks promising, with advancements in technology driving innovation in the field. Below are some trends to watch:
1. Quantum Cryptography
Quantum cryptography offers unparalleled security by leveraging the principles of quantum mechanics. As this technology matures, it may become a standard feature in SSH protocols.
2. AI-Driven Security
Artificial intelligence is increasingly being used to enhance cybersecurity measures. AI-powered systems can detect and respond to threats in real-time, providing an additional layer of protection for IoT SSH connections.
3. Edge Computing
Edge computing brings processing power closer to IoT devices, reducing latency and improving performance. By integrating edge computing with SSH, organizations can achieve faster and more efficient remote device management.
Conclusion and Next Steps
In conclusion, the best remote IoT SSH solutions offer a secure and efficient way to manage IoT devices from anywhere in the world. By understanding SSH basics, implementing best practices, and staying informed about future trends, you can ensure that your IoT ecosystem remains protected and functional.
We encourage you to take action by exploring the tools and techniques discussed in this article. Whether you're a seasoned professional or a newcomer to the world of IoT, there's always room to grow and improve. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insightful content.