In today's hyper-connected world, the ability to securely access remote IoT devices is more critical than ever. With the increasing number of smart devices in homes and businesses, leveraging SSH (Secure Shell) for remote management has become a fundamental practice. SSH remote IoT device management ensures secure communication between devices, protecting sensitive data from unauthorized access.
As the Internet of Things (IoT) continues to expand, users need reliable solutions to manage their devices remotely. Whether you're a tech enthusiast, a network administrator, or a business owner, understanding how SSH works with IoT devices can significantly enhance your operational capabilities. This article dives deep into the topic, exploring everything from setup to advanced security configurations.
By the end of this guide, you'll gain a comprehensive understanding of SSH remote IoT device management. You'll learn how to set up secure connections, troubleshoot common issues, and implement best practices for maintaining robust cybersecurity. Let's get started!
Read also:Exploring The Legacy Of Pavel Moreno An Indepth Look At His Journey And Achievements
Table of Contents
- Introduction to SSH Remote IoT Device Management
- What is SSH and Why is it Important?
- IoT Security Challenges and SSH Solutions
- Step-by-Step Guide to Setting Up SSH on IoT Devices
- Best Practices for Remote Access
- Troubleshooting Common SSH Issues
- Advanced SSH Configurations for IoT Devices
- Top Security Tips for SSH Remote IoT Device Management
- Useful Tools for Managing SSH Connections
- Future Trends in SSH and IoT Security
- Conclusion and Call to Action
Introduction to SSH Remote IoT Device Management
SSH remote IoT device management is a crucial aspect of modern cybersecurity practices. It allows users to securely access and manage IoT devices from anywhere in the world, ensuring that critical systems remain under control even when physical access is not possible.
One of the primary advantages of using SSH is its robust encryption protocols, which protect data during transmission. Unlike traditional methods such as telnet, SSH ensures that all communication between devices is encrypted, making it nearly impossible for attackers to intercept sensitive information.
Furthermore, SSH provides a reliable platform for automating tasks, performing remote updates, and monitoring device performance. This makes it an indispensable tool for both individual users and large enterprises relying on IoT infrastructure.
What is SSH and Why is it Important?
Definition and Functionality
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over untrusted networks. It provides a secure channel for accessing remote devices, transferring files, and executing commands.
- SSH uses encryption to protect data during transmission.
- It supports authentication methods such as passwords and public key cryptography.
- SSH is widely used in IoT environments due to its reliability and security features.
For IoT devices, SSH offers a secure way to manage configurations, monitor performance, and troubleshoot issues without compromising sensitive information.
IoT Security Challenges and SSH Solutions
Common IoT Security Threats
IoT devices are vulnerable to various security threats, including unauthorized access, data breaches, and malware attacks. These risks can be mitigated by implementing robust security measures, such as SSH remote IoT device management.
Read also:Hdhub4u Your Ultimate Destination For Highquality Movies And Tv Shows
SSH addresses these challenges by:
- Providing end-to-end encryption for all communications.
- Offering strong authentication mechanisms to prevent unauthorized access.
- Allowing administrators to monitor and control device activity remotely.
By integrating SSH into your IoT infrastructure, you can significantly enhance the security of your network and protect sensitive data from potential threats.
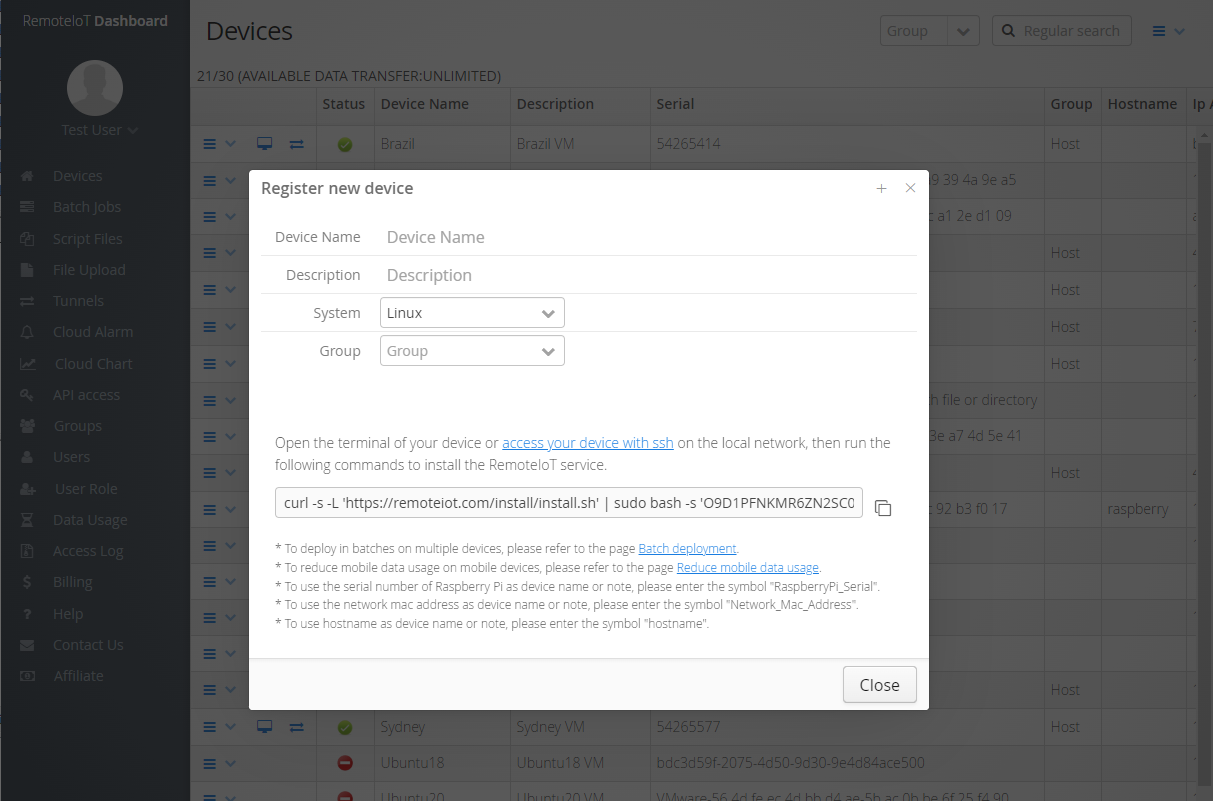
Step-by-Step Guide to Setting Up SSH on IoT Devices
Prerequisites
Before setting up SSH on your IoT devices, ensure you have the following:
- An IoT device with SSH capabilities (e.g., Raspberry Pi, ESP32).
- A stable internet connection.
- A computer or laptop with an SSH client installed (e.g., PuTTY for Windows, Terminal for macOS).
Configuration Steps
Follow these steps to set up SSH on your IoT device:
- Connect your IoT device to the internet.
- Enable SSH on the device by accessing its settings or configuration files.
- Use an SSH client to connect to the device using its IP address.
- Authenticate using a password or public key.
- Begin managing your device remotely through the SSH session.
This process ensures that your IoT device is securely accessible from anywhere, allowing you to manage it effectively without compromising security.
Best Practices for Remote Access
Securing Your SSH Connections
To ensure secure remote access to your IoT devices, follow these best practices:
- Use strong, unique passwords for authentication.
- Implement public key authentication for added security.
- Disable password authentication if possible to prevent brute-force attacks.
- Regularly update your SSH server software to patch vulnerabilities.
By adhering to these guidelines, you can minimize the risk of unauthorized access and protect your IoT devices from potential threats.
Troubleshooting Common SSH Issues
Identifying and Resolving Problems
Even with proper configuration, SSH connections can sometimes encounter issues. Here are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running on the IoT device and that the firewall allows incoming connections on port 22.
- Authentication Failed: Verify that the username and password are correct or check your public key configuration.
- Timeout Errors: Check your network connection and ensure that there are no routing issues between your computer and the IoT device.
Addressing these issues promptly can help maintain uninterrupted access to your IoT devices.
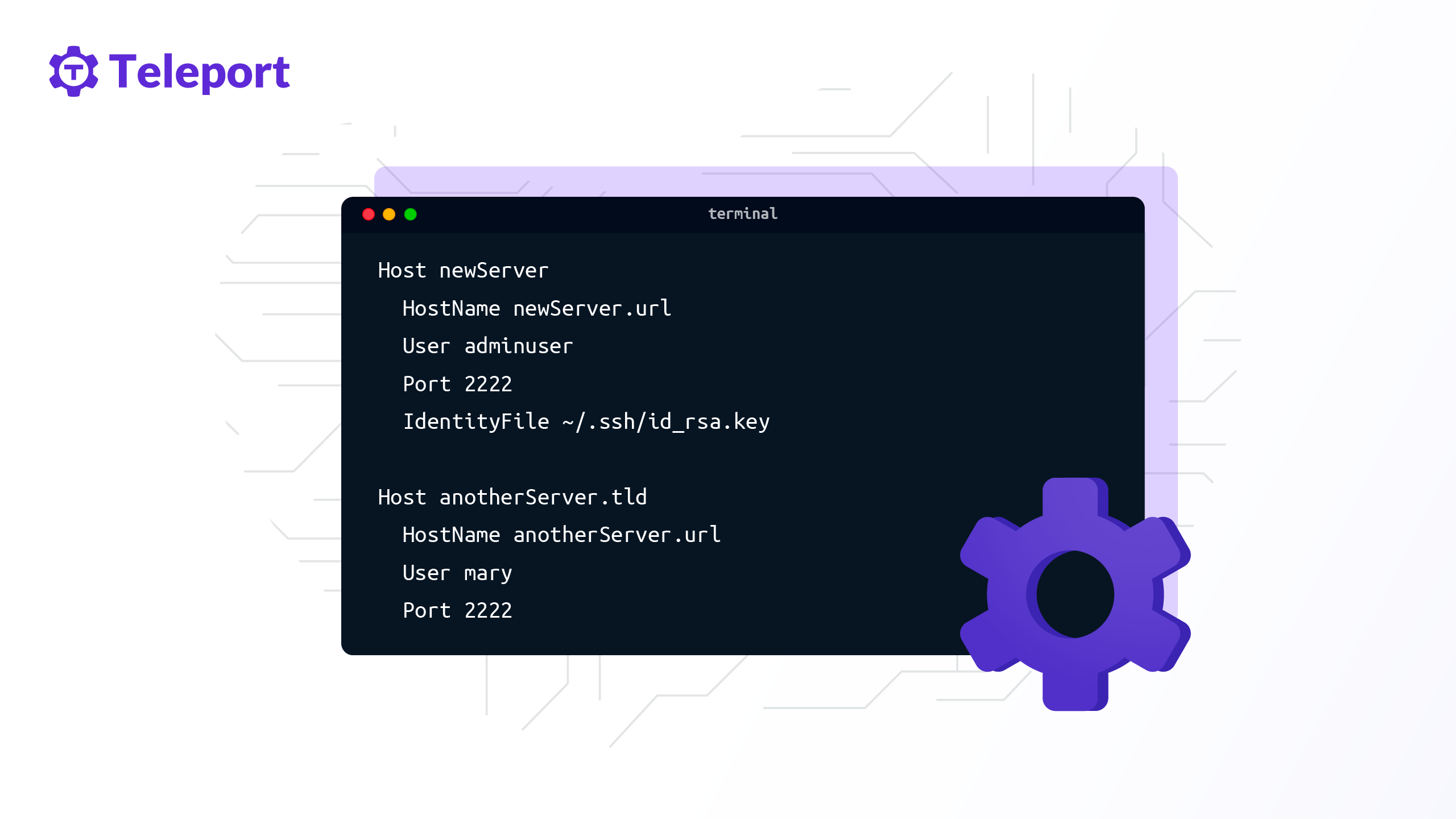
Advanced SSH Configurations for IoT Devices
Customizing SSH Settings
For advanced users, SSH offers numerous configuration options to enhance security and performance. Some of these include:
- Changing the default SSH port to a non-standard number to reduce automated attacks.
- Enabling logging to monitor SSH activity and detect suspicious behavior.
- Configuring SSH to use stronger encryption algorithms for increased security.
By fine-tuning these settings, you can create a more secure and efficient SSH environment for managing your IoT devices.
Top Security Tips for SSH Remote IoT Device Management
Staying Ahead of Threats
In addition to the best practices mentioned earlier, consider implementing the following security tips:
- Regularly audit SSH logs to identify and respond to potential threats.
- Limit SSH access to specific IP addresses or networks to reduce exposure.
- Use two-factor authentication (2FA) for an additional layer of security.
These measures can help safeguard your IoT devices against evolving cybersecurity threats.
Useful Tools for Managing SSH Connections
Streamlining Your Workflow
Several tools are available to simplify SSH remote IoT device management. Some popular options include:
- PuTTY: A free and open-source SSH client for Windows users.
- SSHFS: Allows you to mount remote file systems over SSH, enabling seamless file access.
- MobaXterm: A comprehensive SSH client with additional features like session management and terminal emulation.
These tools can enhance your productivity and make managing SSH connections easier and more efficient.
Future Trends in SSH and IoT Security
Evolution of Secure Communication Protocols
As technology advances, so do the methods for securing IoT devices. Future trends in SSH and IoT security may include:
- Integration of quantum-resistant encryption algorithms to protect against future threats.
- Increased adoption of zero-trust architectures to enhance network security.
- Development of AI-driven solutions for detecting and responding to security incidents in real-time.
Staying informed about these developments can help you stay ahead of the curve and ensure the long-term security of your IoT infrastructure.
Conclusion and Call to Action
In conclusion, SSH remote IoT device management is an essential practice for securing and maintaining your IoT devices. By following the guidelines outlined in this article, you can set up secure connections, implement best practices, and troubleshoot common issues effectively.
We encourage you to take action by:
- Implementing SSH on your IoT devices to enhance security.
- Regularly updating your knowledge of SSH and IoT security trends.
- Sharing this article with others to spread awareness about the importance of secure remote access.
Thank you for reading, and we hope this guide has been helpful in your journey toward secure IoT management. Feel free to leave a comment or explore other articles on our website for more valuable insights!