In today's interconnected world, securely connect remote IoT VPC has become a critical aspect of modern technology infrastructure. As businesses increasingly rely on Internet of Things (IoT) devices, ensuring secure communication between remote networks and Virtual Private Clouds (VPCs) is essential for safeguarding sensitive data. This article will delve into the importance of secure IoT VPC connections, providing actionable strategies and best practices to fortify your network.
The rise of IoT devices has transformed industries, enabling smart homes, intelligent factories, and advanced healthcare systems. However, with this innovation comes the challenge of maintaining robust cybersecurity measures. Connecting IoT devices to remote VPCs without compromising security requires a well-planned approach, incorporating encryption, access control, and monitoring tools.
Whether you're an IT professional, a business owner, or a tech enthusiast, understanding how to securely connect remote IoT VPC is crucial. This guide will cover everything from the basics of IoT and VPC to advanced security techniques, ensuring your network remains protected against potential threats.
Read also:Discover The Vibrant Charm Of Usa San Antonio A Hidden Gem Worth Exploring
Table of Contents
- Introduction to IoT and VPC
- Why Securely Connect Remote IoT VPC?
- Architecture of IoT VPC
- Best Practices for Secure IoT VPC
- Encryption Methods for IoT
- Access Control and Authentication
- Monitoring and Logging
- Common Security Challenges
- Future of Secure IoT VPC
- Conclusion
Introduction to IoT and VPC
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that allows them to exchange data. A Virtual Private Cloud (VPC) is an isolated section of a cloud environment that provides secure and scalable infrastructure for hosting applications and services. Combining IoT with VPC enables businesses to create a secure and efficient ecosystem for data processing and storage.
Connecting IoT devices to a remote VPC offers numerous advantages, including centralized management, improved scalability, and enhanced security. However, this integration requires careful planning to ensure data integrity and prevent unauthorized access.
Why Securely Connect Remote IoT VPC?
Securely connecting remote IoT VPC is vital for several reasons. First, it protects sensitive data from cyber threats, ensuring compliance with industry regulations. Second, it enhances operational efficiency by enabling seamless communication between devices and cloud services. Lastly, it reduces the risk of costly data breaches, which can damage a company's reputation and financial standing.
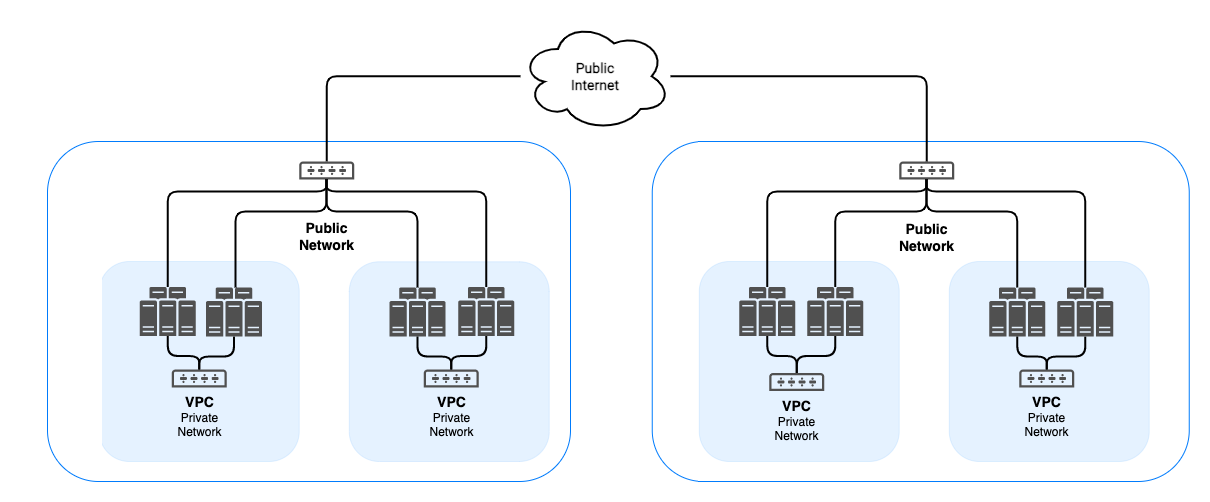
Architecture of IoT VPC
Network Layer
The network layer forms the foundation of IoT VPC architecture, facilitating communication between devices and the cloud. This layer includes routers, switches, and gateways that manage data flow and ensure connectivity. Implementing a robust network layer is crucial for maintaining reliable and secure IoT VPC connections.
Security Layer
The security layer encompasses encryption protocols, firewalls, and intrusion detection systems that safeguard IoT VPC environments. By integrating these components, businesses can effectively mitigate potential security risks and protect their data from malicious actors.
Best Practices for Secure IoT VPC
Adopting best practices for secure IoT VPC is essential for maintaining a strong cybersecurity posture. Below are some key strategies to consider:
Read also:London Academy Of Music And Dramatic Art A Comprehensive Guide To Excellence In Performing Arts Education
- Use strong encryption protocols to protect data in transit and at rest.
- Implement multi-factor authentication (MFA) for accessing IoT devices and VPC environments.
- Regularly update firmware and software to address known vulnerabilities.
- Segment networks to isolate critical assets and limit the impact of potential breaches.
Encryption Methods for IoT
Encryption plays a critical role in securing IoT VPC connections. Common encryption methods include:
- Advanced Encryption Standard (AES): A widely used symmetric encryption algorithm for securing data.
- Transport Layer Security (TLS): A protocol that ensures secure communication between devices and servers.
- Secure Sockets Layer (SSL): An older protocol that provides encryption for web traffic.
Choosing the right encryption method depends on the specific requirements of your IoT VPC setup and the level of security needed.
Access Control and Authentication
Implementing robust access control and authentication mechanisms is crucial for securing IoT VPC environments. This involves:
- Defining roles and permissions for users and devices.
- Using strong passwords and passphrase policies.
- Enforcing multi-factor authentication (MFA) for added security.
By restricting access to authorized personnel and devices, businesses can significantly reduce the risk of unauthorized access and data breaches.
Monitoring and Logging
Continuous monitoring and logging are essential for detecting and responding to security incidents in IoT VPC environments. Key practices include:
- Implementing intrusion detection and prevention systems (IDPS).
- Configuring centralized logging solutions to track activities across the network.
- Performing regular security audits and vulnerability assessments.
These measures help identify potential threats and enable swift action to mitigate risks.
Common Security Challenges
Securing remote IoT VPC connections presents several challenges, including:
- Device management: Ensuring all IoT devices are properly configured and updated.
- Data privacy: Protecting sensitive information from unauthorized access and disclosure.
- Scalability: Maintaining security as the network expands to accommodate more devices.
Addressing these challenges requires a proactive approach, combining technology, processes, and people to create a secure IoT VPC environment.
Future of Secure IoT VPC
The future of secure IoT VPC lies in advancements such as artificial intelligence (AI), machine learning (ML), and quantum encryption. These technologies promise to enhance security by detecting anomalies, predicting threats, and providing unbreakable encryption methods. As IoT continues to evolve, businesses must stay informed about emerging trends and adopt innovative solutions to protect their networks.
Conclusion
Securing remote IoT VPC connections is a critical component of modern cybersecurity strategies. By understanding the architecture, implementing best practices, and leveraging advanced technologies, businesses can protect their data and maintain operational integrity. We encourage readers to apply the strategies outlined in this guide and explore additional resources to further enhance their IoT VPC security.
Feel free to leave a comment below sharing your thoughts or questions about securely connect remote IoT VPC. Don't forget to share this article with others who may find it useful. For more insights on cybersecurity and IoT, explore our other articles on the website.