In today's interconnected digital landscape, remote IoT (Internet of Things) devices have become a cornerstone of modern technology. As businesses and individuals increasingly rely on these devices, the importance of secure communication and management cannot be overstated. RemoteIoT SSH key management plays a pivotal role in ensuring the integrity and confidentiality of data exchanged between devices. This article will delve into the intricacies of RemoteIoT SSH key management, offering insights and actionable advice to enhance your security protocols.
With the rise of IoT devices, managing secure connections has become more complex. Traditional methods of securing devices are no longer sufficient, especially when dealing with remote systems. This is where RemoteIoT SSH key management comes into play, providing a robust framework for securing communication channels.
This guide is designed to equip you with the knowledge and tools necessary to implement effective SSH key management strategies. Whether you're a seasoned IT professional or a newcomer to the world of IoT, this article will provide valuable insights into best practices and emerging trends in the field.
Read also:Kardashian Twins Everything You Need To Know About The Famous Siblings
Understanding RemoteIoT SSH Key Management
What is SSH Key Management?
SSH key management refers to the process of creating, distributing, storing, and revoking SSH keys used for secure communication between devices. In the context of RemoteIoT, this involves ensuring that IoT devices can communicate securely with servers or other devices over the internet without compromising sensitive data.
SSH keys serve as a digital form of identification, replacing the need for passwords and providing a more secure authentication method. By implementing SSH key management, organizations can significantly reduce the risk of unauthorized access and data breaches.
Why is RemoteIoT SSH Key Management Important?
In the realm of IoT, devices often operate in unsecured environments, making them vulnerable to cyber threats. RemoteIoT SSH key management addresses these vulnerabilities by establishing secure connections that protect data in transit.
- Prevents unauthorized access to IoT devices.
- Ensures data integrity and confidentiality.
- Facilitates seamless communication between devices and servers.
By prioritizing SSH key management, organizations can safeguard their networks and protect sensitive information from malicious actors.
Core Components of RemoteIoT SSH Key Management
Key Generation and Distribution
Generating and distributing SSH keys is the first step in establishing secure communication. This process involves creating public and private key pairs, where the public key is shared with the server or device, and the private key is kept securely on the client side.
Best practices for key generation include:
Read also:Who Is Daphnerosen Exploring Her Life Career And Achievements
- Using strong cryptographic algorithms such as RSA or ECC.
- Generating keys with sufficient bit length (e.g., 2048-bit or higher).
- Storing private keys in secure environments, such as hardware security modules (HSMs).
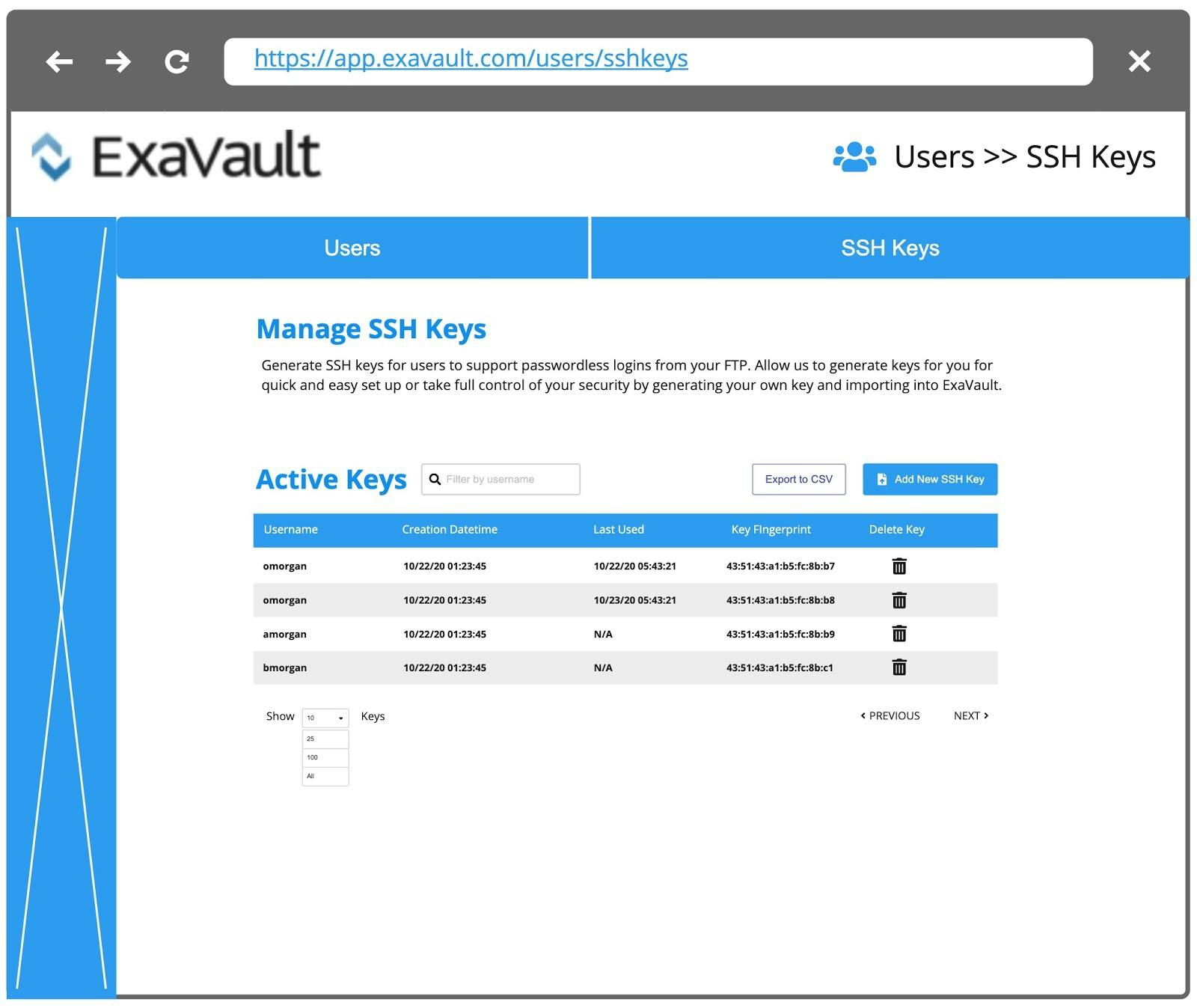
Key Storage and Revocation
Once keys are generated, proper storage and revocation mechanisms must be in place to maintain security. Keys should be stored in secure locations, and access to them should be strictly controlled.
Revocation processes are essential for addressing compromised keys or retiring old ones. Implementing a centralized key management system can streamline these processes and ensure compliance with security policies.
Best Practices for RemoteIoT SSH Key Management
Implementing Strong Authentication
Strong authentication is critical for securing IoT devices. By leveraging SSH keys, organizations can eliminate the need for passwords, reducing the risk of brute-force attacks and credential theft.
Key strategies for strong authentication include:
- Using multi-factor authentication (MFA) in conjunction with SSH keys.
- Regularly rotating keys to minimize the impact of potential breaches.
- Monitoring key usage and detecting anomalies in real-time.
Automating Key Management Processes
Manual key management can be error-prone and time-consuming. Automating key management processes can improve efficiency and reduce the likelihood of human error.
Automation tools can handle tasks such as:
- Key generation and distribution.
- Key rotation and revocation.
- Audit logging and compliance reporting.
Challenges in RemoteIoT SSH Key Management
Key Scalability
As the number of IoT devices grows, managing SSH keys at scale becomes increasingly challenging. Organizations must implement scalable solutions that can accommodate the growing demand for secure connections.
Strategies for addressing scalability include:
- Using cloud-based key management systems.
- Implementing hierarchical key structures to simplify management.
- Leveraging automation to streamline key operations.
Key Security
Ensuring the security of SSH keys is paramount to maintaining the integrity of IoT networks. Organizations must adopt robust security measures to protect keys from unauthorized access and theft.
Best practices for key security include:
- Encrypting keys during storage and transmission.
- Implementing role-based access controls (RBAC) for key management.
- Regularly auditing key usage and permissions.
Emerging Trends in RemoteIoT SSH Key Management
Quantum-Resistant Cryptography
With the advent of quantum computing, traditional cryptographic algorithms may become vulnerable to attacks. Quantum-resistant cryptography offers a solution by providing algorithms that are resistant to quantum-based attacks.
Organizations should consider adopting quantum-resistant algorithms to future-proof their SSH key management systems.
Blockchain-Based Key Management
Blockchain technology offers a decentralized approach to key management, enhancing security and transparency. By leveraging blockchain, organizations can create tamper-proof records of key transactions and ensure the integrity of their key management processes.
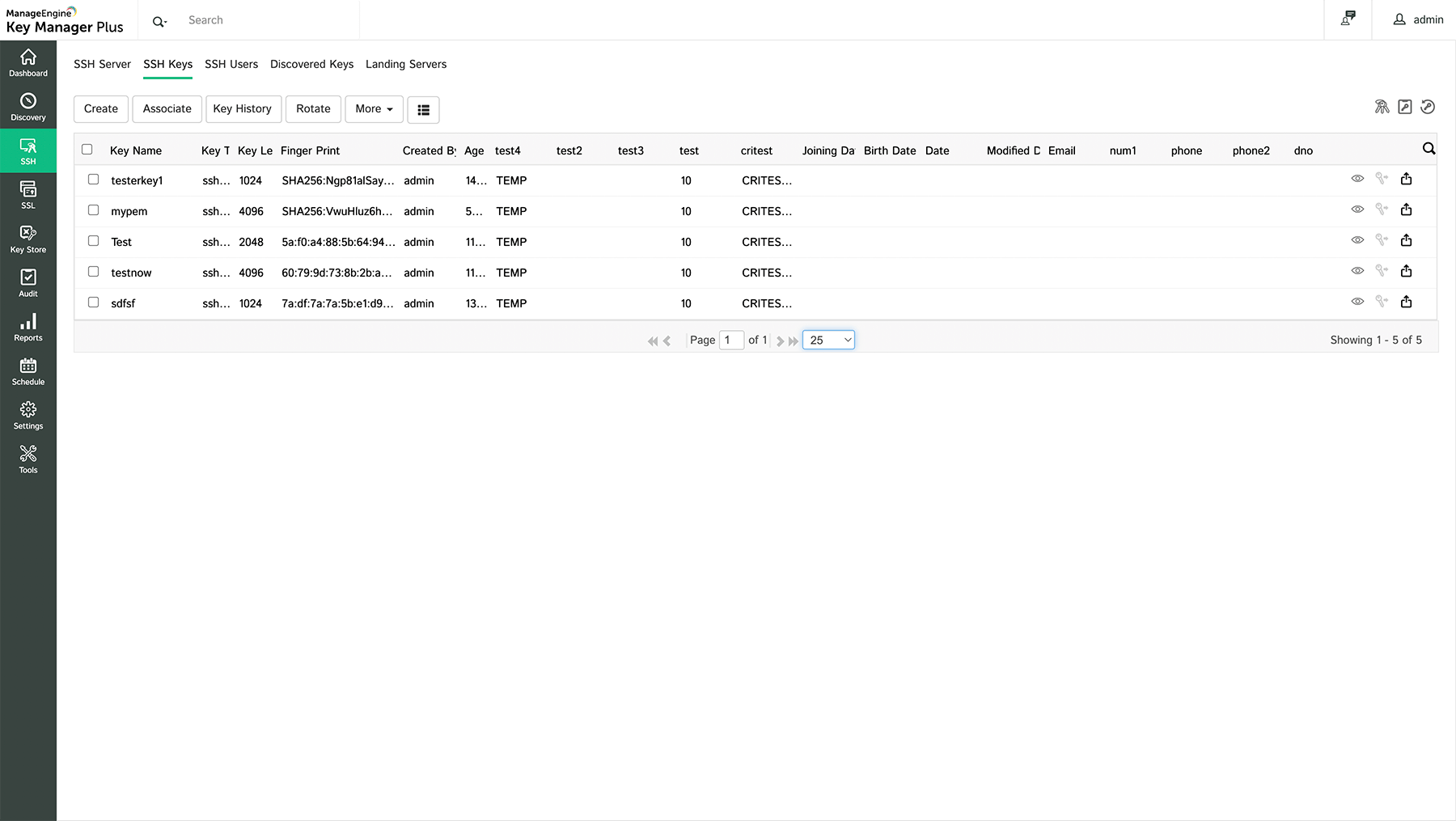
Tools and Technologies for RemoteIoT SSH Key Management
OpenSSH
OpenSSH is a widely used open-source tool for implementing SSH key management. It provides a robust framework for securing communications and managing keys across IoT devices.
Key features of OpenSSH include:
- Support for various cryptographic algorithms.
- Configurable security policies.
- Integration with third-party tools and systems.
HashiCorp Vault
HashiCorp Vault is a popular solution for managing secrets, including SSH keys. It offers a centralized platform for storing and distributing keys securely.
Benefits of using HashiCorp Vault include:
- Automated key rotation and revocation.
- Role-based access controls for key management.
- Comprehensive audit logging and reporting.
Case Studies in RemoteIoT SSH Key Management
Company A: Securing IoT Devices in Smart Cities
Company A implemented a comprehensive SSH key management strategy to secure IoT devices deployed in smart city infrastructure. By leveraging automation and centralized key management, they were able to reduce the risk of cyberattacks and ensure the reliability of their systems.
Company B: Enhancing Industrial IoT Security
Company B focused on strengthening SSH key management for their industrial IoT devices. Through the adoption of quantum-resistant cryptography and blockchain-based solutions, they achieved a higher level of security and compliance with industry standards.
Compliance and Regulatory Considerations
Data Privacy Laws
Organizations must adhere to data privacy laws such as GDPR and CCPA when implementing SSH key management systems. These regulations require the protection of personal data and the implementation of robust security measures.
Cybersecurity Standards
Adhering to cybersecurity standards such as NIST and ISO 27001 is essential for ensuring the security of IoT networks. These standards provide guidelines for managing SSH keys and securing communication channels.
Conclusion
RemoteIoT SSH key management is a critical component of securing IoT devices and networks. By implementing best practices, leveraging emerging technologies, and adhering to regulatory requirements, organizations can enhance their security posture and protect sensitive information.
We encourage readers to:
- Implement automated key management systems to improve efficiency.
- Stay informed about emerging trends and technologies in SSH key management.
- Share your thoughts and experiences in the comments section below.
For more insights into IoT security and related topics, explore our other articles and resources.
Table of Contents
- Understanding RemoteIoT SSH Key Management
- Core Components of RemoteIoT SSH Key Management
- Best Practices for RemoteIoT SSH Key Management
- Challenges in RemoteIoT SSH Key Management
- Emerging Trends in RemoteIoT SSH Key Management
- Tools and Technologies for RemoteIoT SSH Key Management
- Case Studies in RemoteIoT SSH Key Management
- Compliance and Regulatory Considerations
- Conclusion