In the rapidly evolving world of technology, IoT remote access via SSH for free has become a popular solution for individuals and businesses looking to manage their devices remotely without incurring high costs. The Internet of Things (IoT) has transformed the way we interact with devices, enabling seamless connectivity and automation. Remote access plays a pivotal role in this ecosystem, allowing users to monitor and control their IoT devices from anywhere in the world.
With SSH (Secure Shell), you can establish secure connections to your IoT devices, ensuring that your data remains protected while enabling remote management. This guide delves into the intricacies of IoT remote access via SSH for free, equipping you with the knowledge and tools to implement this technology effectively.
Whether you're a hobbyist, a small business owner, or a tech enthusiast, understanding how to leverage SSH for IoT remote access is essential. By the end of this article, you'll have a clear roadmap to set up and manage your IoT devices remotely without breaking the bank.
Read also:Best Remote Ssh Iot Over Internet Free A Comprehensive Guide
Table of Contents
- Introduction to IoT and SSH
- Benefits of Using SSH for IoT Remote Access
- Setting Up IoT Remote Access via SSH
- Security Considerations for IoT SSH
- Tools for Free SSH Access
- Troubleshooting Common Issues
- Optimizing IoT SSH Performance
- Real-World Applications of IoT SSH
- Future Trends in IoT Remote Access
- Conclusion
Introduction to IoT and SSH
The Internet of Things (IoT) refers to the interconnected network of devices that communicate and exchange data over the internet. These devices range from smart home appliances to industrial machinery, all designed to enhance efficiency and convenience. SSH, or Secure Shell, is a network protocol that provides a secure way to access remote devices.
Using SSH for IoT remote access offers several advantages, including enhanced security, ease of use, and cost-effectiveness. Unlike proprietary solutions that may require expensive licenses, SSH is widely available for free, making it an attractive option for those looking to manage their IoT devices remotely without additional expenses.
Understanding SSH Protocol
SSH operates by encrypting data transmitted between a client and a server, ensuring that sensitive information remains protected from unauthorized access. This protocol supports various authentication methods, including password-based and public-key authentication, providing flexibility in securing your IoT devices.
Benefits of Using SSH for IoT Remote Access
Adopting SSH for IoT remote access comes with numerous benefits, making it a preferred choice for many users. Below are some of the key advantages:
- Cost-Effective: SSH is available for free, eliminating the need for expensive proprietary software.
- Secure: With encryption and robust authentication mechanisms, SSH ensures the safety of your data during transmission.
- Scalable: Whether you manage a single device or a large network, SSH can scale to meet your needs.
- Platform Independent: SSH works across multiple platforms, including Linux, Windows, and macOS, ensuring compatibility with various IoT devices.
Why Choose Free SSH Solutions?
Free SSH solutions provide an excellent alternative to paid options without compromising on security or functionality. These solutions are often open-source, fostering a community-driven development process that ensures continuous improvement and innovation.
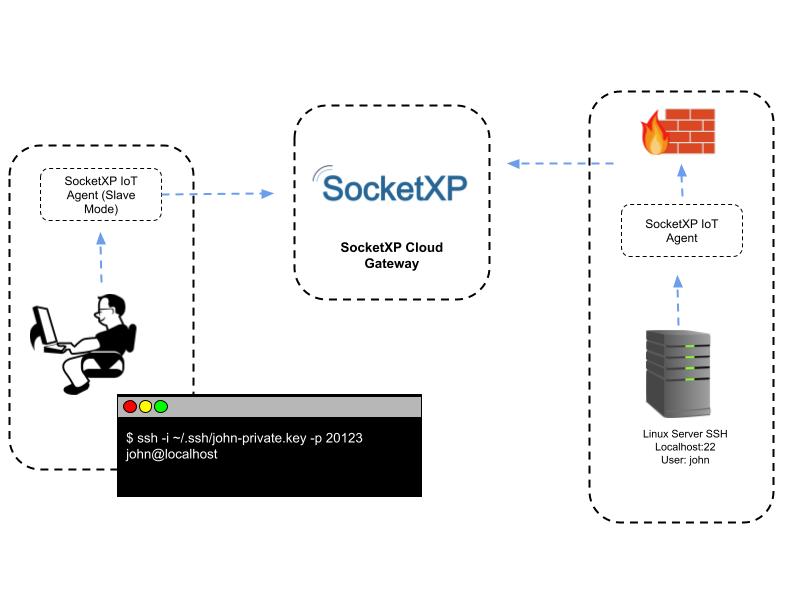
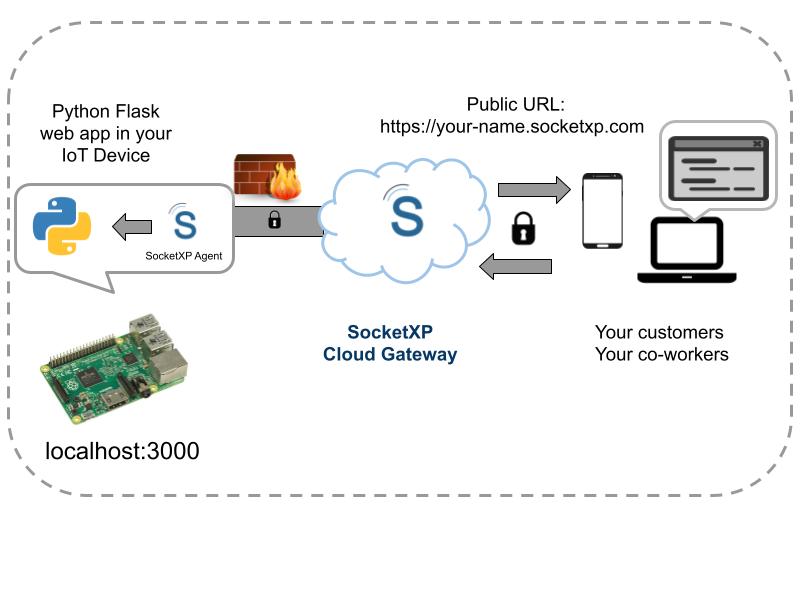
Setting Up IoT Remote Access via SSH
Setting up IoT remote access via SSH involves several steps, from configuring your devices to establishing secure connections. Follow this step-by-step guide to get started:
Read also:Patrick Mahomes Father The Man Behind The Nfl Stars Success
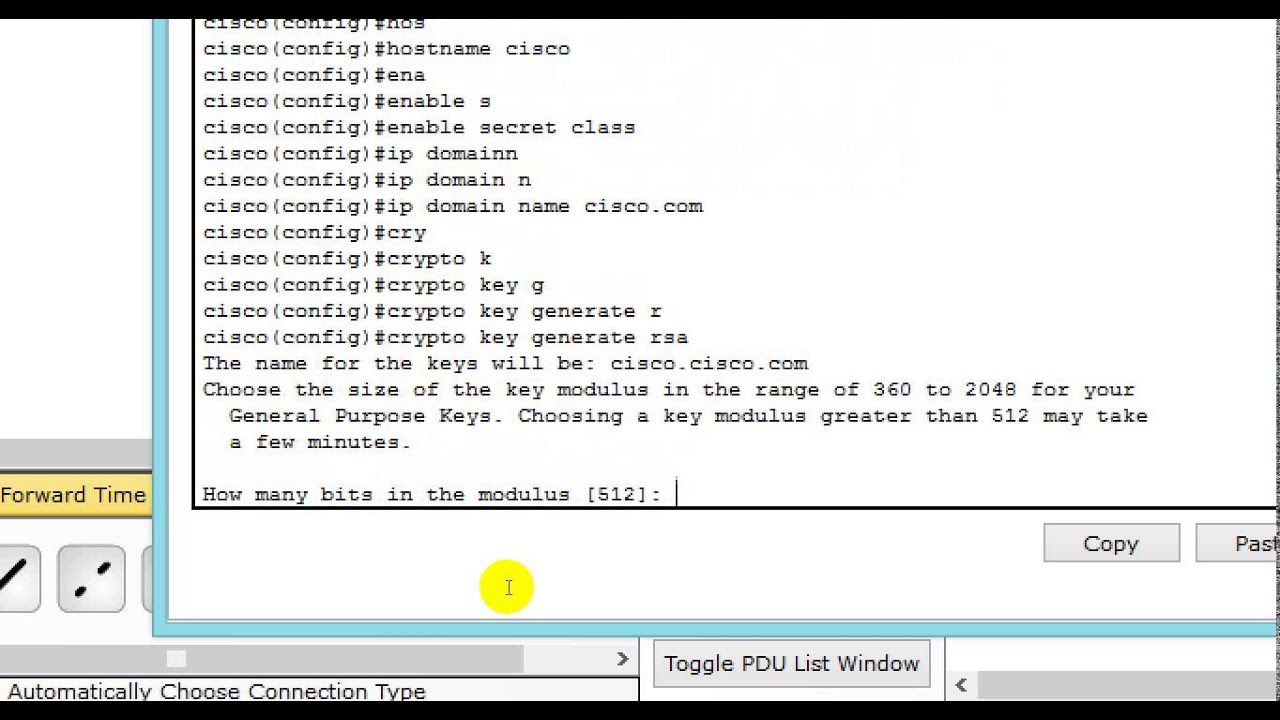
- Install SSH Server: Begin by installing an SSH server on your IoT device. For Linux-based devices, you can use OpenSSH.
- Generate SSH Keys: Create public and private keys for authentication to enhance security.
- Configure Firewall Settings: Adjust your firewall to allow SSH traffic on the appropriate port (usually port 22).
- Test the Connection: Use an SSH client to connect to your IoT device and ensure everything is working as expected.
Best Practices for Setup
When setting up IoT remote access via SSH, adhere to best practices such as using strong passwords, enabling two-factor authentication, and regularly updating your software to patch vulnerabilities.
Security Considerations for IoT SSH
While SSH provides robust security features, it's essential to address potential vulnerabilities to ensure the safety of your IoT devices. Consider the following security measures:
- Use Strong Authentication: Implement public-key authentication instead of relying solely on passwords.
- Disable Root Login: Restrict direct access to the root account to minimize the risk of unauthorized access.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities promptly.
Advanced Security Techniques
For added security, consider implementing advanced techniques such as IP whitelisting, port forwarding, and using a jump server to further secure your IoT remote access setup.
Tools for Free SSH Access
Several tools are available for free SSH access, catering to different operating systems and user preferences. Some popular options include:
- Putty: A widely used SSH client for Windows users, known for its simplicity and reliability.
- OpenSSH: Available on Linux and macOS, OpenSSH is a comprehensive suite of secure networking utilities.
- Termius: A cross-platform SSH client that supports iOS, Android, macOS, and Windows, offering a user-friendly interface.
Comparing SSH Tools
Each SSH tool has its strengths and weaknesses. Evaluate your specific needs, such as platform compatibility and feature set, to choose the best tool for your IoT remote access requirements.
Troubleshooting Common Issues
Despite its reliability, SSH may encounter issues that can disrupt IoT remote access. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running and that the firewall allows traffic on the correct port.
- Authentication Failure: Verify that your credentials are correct and that public-key authentication is properly configured.
- Slow Connections: Optimize network settings and consider using compression to improve connection speed.
Advanced Troubleshooting Tips
For persistent issues, consult SSH logs for detailed error messages and use diagnostic tools to identify and resolve underlying problems.
Optimizing IoT SSH Performance
Optimizing SSH performance is crucial for maintaining efficient IoT remote access. Consider the following strategies:
- Enable Compression: Reduce data transfer times by enabling compression in your SSH configuration.
- Use Efficient Algorithms: Select algorithms that balance security and performance, such as AES-128 for encryption.
- Limit Concurrent Connections: Restrict the number of simultaneous connections to prevent server overload.
Performance Monitoring
Regularly monitor SSH performance metrics to identify bottlenecks and areas for improvement. Tools like Nagios and Zabbix can help automate this process.
Real-World Applications of IoT SSH
IoT remote access via SSH has numerous real-world applications across various industries. Some examples include:
- Smart Agriculture: Farmers use SSH to remotely monitor and control irrigation systems, ensuring optimal water usage.
- Industrial Automation: Manufacturers leverage SSH to manage machinery and production lines from remote locations.
- Home Automation: Homeowners utilize SSH to secure and control smart home devices, enhancing convenience and security.
Case Studies
Explore case studies showcasing successful implementations of IoT SSH in different sectors to gain insights into its practical applications and benefits.
Future Trends in IoT Remote Access
The future of IoT remote access via SSH looks promising, with emerging trends such as quantum-resistant cryptography and AI-driven security measures set to enhance its capabilities. As technology continues to evolve, staying informed about these trends will be crucial for maximizing the potential of IoT SSH.
Innovations in SSH Technology
Keep an eye on innovations in SSH technology, such as new encryption algorithms and automation tools, to ensure your IoT remote access setup remains cutting-edge.
Conclusion
In conclusion, IoT remote access via SSH for free offers a cost-effective, secure, and scalable solution for managing IoT devices remotely. By following the guidelines and best practices outlined in this article, you can successfully implement and optimize this technology to meet your needs.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into IoT and related technologies. Together, let's unlock the full potential of IoT remote access via SSH!