IoT device SSH access free has become an essential topic in the tech world today. As the Internet of Things (IoT) continues to grow, more devices are becoming interconnected, making remote access a critical requirement for users and administrators alike. However, ensuring secure access without spending a fortune can be challenging. This guide aims to provide you with everything you need to know about free IoT device SSH access.
With billions of IoT devices now connected globally, the need for secure remote management is more important than ever. Whether you're managing home automation systems, industrial sensors, or smart city infrastructure, SSH (Secure Shell) offers a reliable way to access and manage these devices remotely.
This article will explore the basics of SSH, its importance in IoT, and how you can gain free access to your IoT devices using SSH. We'll also discuss the best practices for ensuring security and provide practical tips to help you get started.
Read also:Why Fort Knox Gun Safes Are The Ultimate Choice For Security And Peace Of Mind
Table of Contents
- Introduction to IoT Device SSH Access
- What is SSH?
- Why Use SSH for IoT Devices?
- Free SSH Options for IoT Devices
- Setting Up SSH Access on IoT Devices
- Security Best Practices for IoT SSH Access
- Troubleshooting Common SSH Issues
- Tools and Software for Managing IoT SSH
- Case Studies: Real-World Examples of IoT SSH Usage
- The Future of IoT Device SSH Access
- Conclusion
Introduction to IoT Device SSH Access
IoT device SSH access free is a powerful solution that allows users to remotely manage and monitor their connected devices securely. SSH, short for Secure Shell, is a cryptographic network protocol designed to provide secure communication over unsecured networks. In the context of IoT, SSH serves as a vital tool for administrators who need to manage devices remotely without compromising security.
IoT devices are increasingly being deployed in various industries, from healthcare to manufacturing, and even in smart homes. These devices often require regular updates, monitoring, and troubleshooting. SSH offers a secure and reliable method for performing these tasks, ensuring that sensitive data remains protected.
While commercial SSH solutions are available, there are also free options that can be used for personal or small-scale projects. This guide will explore these free alternatives and provide step-by-step instructions for setting them up on your IoT devices.
What is SSH?
SSH, or Secure Shell, is a protocol that enables secure communication between two networked devices. It provides encryption for data transmitted over the network, ensuring that sensitive information, such as passwords and commands, cannot be intercepted by unauthorized parties.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between the client and server, making it difficult for attackers to intercept or tamper with the information.
- Authentication: SSH supports various authentication methods, including password-based and public key authentication, to verify the identity of users.
- Command Execution: Users can execute commands remotely on the server, making it an ideal tool for managing IoT devices.
- Tunneling: SSH can be used to create secure tunnels for other protocols, such as HTTP or FTP, ensuring that all communication is encrypted.
SSH is widely used in IT infrastructure for remote server management, file transfers, and secure communication. Its adaptability makes it a perfect fit for IoT devices, where security and reliability are paramount.
Read also:Aldi Pokemon Cards Unveiling The Ultimate Collectors Paradise
Why Use SSH for IoT Devices?
Using SSH for IoT devices offers several advantages, making it a preferred choice for remote access and management:
1. Security
SSH provides robust encryption and authentication mechanisms, ensuring that sensitive data is protected from unauthorized access. This is particularly important in IoT, where devices often handle critical information.
2. Reliability
SSH connections are reliable and can be maintained even in unstable network conditions. This makes it suitable for IoT devices that may operate in challenging environments.
3. Versatility
SSH supports a wide range of functionalities, including remote command execution, file transfers, and tunneling. This versatility allows users to perform various tasks on their IoT devices without needing additional tools.
4. Open Standards
SSH is an open standard, meaning it is supported by a wide range of platforms and devices. This makes it easy to integrate into existing IoT ecosystems.
Free SSH Options for IoT Devices
While there are commercial SSH solutions available, there are also several free options that can be used for IoT devices:
1. OpenSSH
OpenSSH is one of the most popular SSH implementations and is available for free. It is widely supported on various operating systems, including Linux, macOS, and Windows. OpenSSH provides a comprehensive set of tools for secure communication and is ideal for IoT devices running on Linux-based systems.
2. Dropbear SSH
Dropbear SSH is a lightweight SSH server and client designed for embedded systems. It is an excellent choice for IoT devices with limited resources, as it requires minimal memory and processing power.
3. Bitvise SSH Client
Bitvise SSH Client offers a free version for personal use, making it a suitable option for hobbyists and small-scale projects. It provides a user-friendly interface and supports various authentication methods.
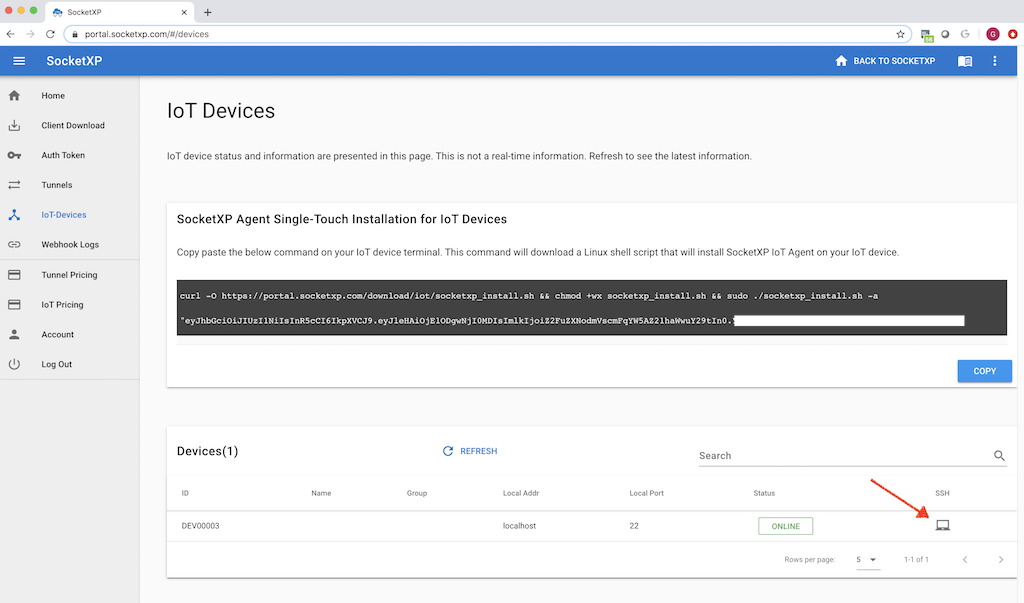
Setting Up SSH Access on IoT Devices
Setting up SSH access on IoT devices involves several steps, including installing the SSH server, configuring the network, and securing the connection. Below is a step-by-step guide:
1. Install SSH Server
The first step is to install an SSH server on your IoT device. For Linux-based devices, you can use OpenSSH or Dropbear SSH. Use the following command to install OpenSSH:
sudo apt-get install openssh-server
2. Configure Network Settings
Ensure that your IoT device is connected to the network and has a static IP address. This will make it easier to access the device remotely.
3. Secure the Connection
Use public key authentication instead of passwords to enhance security. Generate a key pair using the following command:
ssh-keygen -t rsa
Copy the public key to the IoT device using the ssh-copy-id command:
ssh-copy-id user@iot-device-ip
Security Best Practices for IoT SSH Access
Ensuring the security of your IoT device SSH access is crucial to protect against unauthorized access and cyberattacks. Below are some best practices:
1. Use Strong Passwords
If you must use password-based authentication, ensure that you use strong, complex passwords that are difficult to guess.
2. Enable Public Key Authentication
Public key authentication is more secure than password-based authentication and should be enabled whenever possible.
3. Disable Root Login
Disable root login to prevent attackers from gaining administrative access to your IoT device.
4. Monitor Logs
Regularly monitor SSH logs for any suspicious activity and take appropriate action if necessary.
Troubleshooting Common SSH Issues
Even with proper setup, SSH connections can sometimes fail. Below are some common issues and their solutions:
1. Connection Timeout
If you encounter a connection timeout, check your network settings and ensure that the IoT device is reachable from your location.
2. Authentication Failed
Authentication failures can occur due to incorrect passwords or keys. Double-check your credentials and ensure that they are correct.
3. Port Blocked
If the SSH port is blocked by a firewall, you may need to configure your firewall settings to allow SSH traffic.
Tools and Software for Managing IoT SSH
Several tools and software can help you manage IoT device SSH access more effectively:
1. PuTTY
PuTTY is a popular SSH client for Windows that offers a user-friendly interface and supports various authentication methods.
2. SSHFS
SSHFS allows you to mount remote file systems over SSH, making it easier to manage files on your IoT devices.
3. MobaXterm
MobaXterm is an advanced SSH client that offers additional features such as X11 forwarding and session management.
Case Studies: Real-World Examples of IoT SSH Usage
Several organizations and individuals have successfully implemented SSH for IoT device management. Below are some real-world examples:
1. Smart Home Automation
A homeowner used SSH to remotely manage their smart home devices, including lighting, temperature control, and security systems. This allowed them to make adjustments from anywhere in the world.
2. Industrial IoT
An industrial company deployed SSH to monitor and manage their IoT sensors and machines, ensuring that they remained operational and secure.
The Future of IoT Device SSH Access
As IoT continues to evolve, the role of SSH in secure remote access will become even more critical. Advances in encryption technologies and the development of new protocols will further enhance the security and reliability of SSH connections.
In addition, the increasing adoption of edge computing and 5G networks will enable faster and more efficient communication between IoT devices, making SSH an even more valuable tool for remote management.
Conclusion
IoT device SSH access free offers a cost-effective and secure solution for managing connected devices remotely. By following the steps outlined in this guide, you can set up SSH access on your IoT devices and ensure that they remain secure and reliable.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT and related technologies. Together, let's build a safer and more connected world!
References: