In today's interconnected world, RemoteIoT SSH example plays a crucial role in enabling secure communication between devices in the Internet of Things (IoT) ecosystem. As IoT adoption continues to grow, ensuring secure remote access has become more important than ever. This guide will explore the significance of SSH in IoT environments and provide practical examples to help you implement secure connections.
With the rise of smart devices and industrial automation, businesses and individuals alike face challenges in managing IoT networks effectively. RemoteIoT SSH example offers a reliable solution for securely accessing and managing these devices from anywhere in the world. This technology not only enhances operational efficiency but also protects sensitive data against cyber threats.
This article aims to provide a detailed understanding of RemoteIoT SSH example, its applications, and best practices for implementation. Whether you're a beginner or an experienced professional, this guide will equip you with the knowledge and tools needed to leverage SSH for your IoT projects.
Read also:Jan Halper Hayes A Comprehensive Guide To His Life Career And Contributions
Table of Contents
- Introduction to RemoteIoT SSH
- Why SSH for RemoteIoT?
- Biography of SSH Technology
- Setting Up SSH for RemoteIoT
- Common SSH Commands for RemoteIoT
- Securing RemoteIoT with SSH
- Troubleshooting SSH Connection
- Advanced SSH Features for RemoteIoT
- Real-World RemoteIoT SSH Examples
- Conclusion and Next Steps
Introduction to RemoteIoT SSH
SSH, or Secure Shell, is a cryptographic network protocol used to establish secure connections between devices over an unsecured network. In the context of RemoteIoT SSH example, this technology enables administrators and developers to remotely access IoT devices while maintaining data integrity and confidentiality. SSH provides encryption for all transmitted data, ensuring that sensitive information remains protected from unauthorized access.
The adoption of SSH in IoT environments has increased significantly due to its robust security features and ease of implementation. By leveraging RemoteIoT SSH example, organizations can efficiently manage their IoT networks, perform maintenance tasks, and troubleshoot issues without physical access to the devices.
Understanding the fundamentals of SSH and its applications in IoT is essential for anyone looking to enhance the security and functionality of their IoT projects. This section will explore the basics of SSH and its relevance to RemoteIoT SSH example.
Why SSH for RemoteIoT?
SSH offers several advantages that make it an ideal choice for RemoteIoT SSH example. These include:
- Strong Encryption: SSH uses advanced encryption algorithms to secure data transmissions, protecting against eavesdropping and man-in-the-middle attacks.
- Authentication: The protocol supports various authentication methods, including password-based and public key authentication, ensuring only authorized users can access IoT devices.
- Portability: SSH is compatible with a wide range of operating systems and devices, making it suitable for diverse IoT environments.
- Reliability: SSH connections are robust and reliable, even in challenging network conditions, ensuring uninterrupted access to IoT devices.
By implementing SSH in RemoteIoT SSH example, organizations can significantly enhance the security and efficiency of their IoT operations. This section will delve deeper into the benefits of using SSH for IoT applications and highlight its role in modern networking.
Biography of SSH Technology
SSH was originally developed in 1995 by Tatu Ylönen, a researcher at the Helsinki University of Technology, as a response to a password-sniffing attack on the university's network. Since then, SSH has evolved into a widely adopted standard for secure communication in networked environments.
Read also:Discover Your Dream Home At 215 Apartments Chicago
| Attribute | Detail |
|---|---|
| Creator | Tatu Ylönen |
| Year Developed | 1995 |
| Current Version | SSH-2 |
| Primary Use | Secure remote access and file transfer |
Today, SSH is an integral part of many IT infrastructures, including IoT ecosystems. Its evolution from a simple secure shell protocol to a comprehensive security solution underscores its importance in modern networking.
Setting Up SSH for RemoteIoT
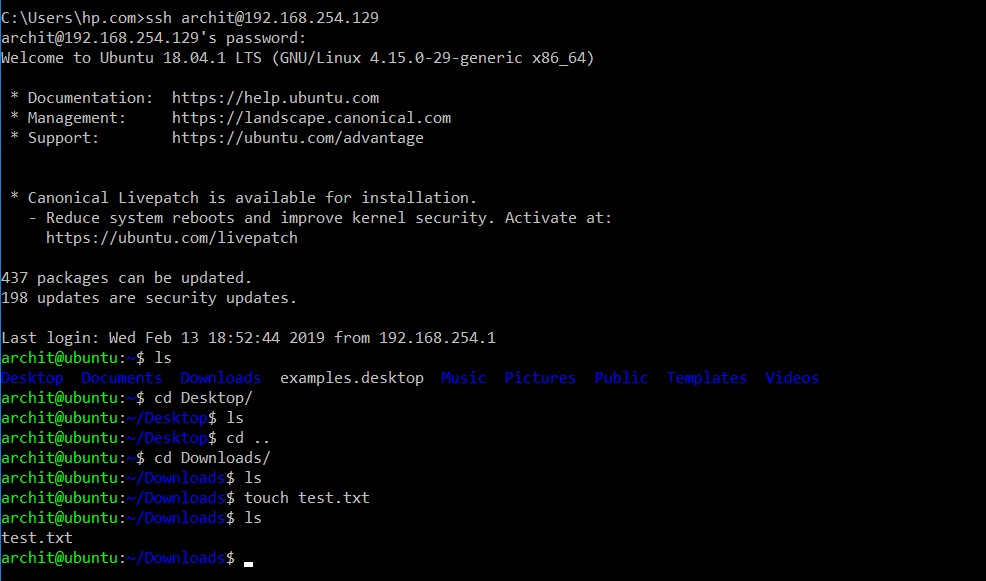
Configuring SSH for RemoteIoT SSH example involves several steps, including installing the necessary software, generating keys, and configuring settings. Below is a step-by-step guide to help you set up SSH for your IoT devices:
- Install SSH Client and Server: Ensure that both the client and server devices have SSH software installed. Popular options include OpenSSH for Linux and PuTTY for Windows.
- Generate SSH Keys: Create a pair of public and private keys using the ssh-keygen command. This step is crucial for public key authentication.
- Configure SSH Settings: Edit the SSH configuration file (usually located at /etc/ssh/sshd_config) to specify parameters such as port number, authentication methods, and access restrictions.
- Test the Connection: Use the ssh command to establish a connection to the IoT device and verify that everything is working as expected.
By following these steps, you can successfully set up SSH for your RemoteIoT SSH example and ensure secure remote access to your IoT devices.
Common SSH Commands for RemoteIoT
Understanding commonly used SSH commands is essential for effectively managing RemoteIoT SSH example. Below is a list of essential commands:
ssh username@hostname: Establishes a connection to the remote device.scp file user@host:/path: Transfers files securely between devices.ssh-keygen: Generates public and private keys for authentication.ssh-copy-id user@host: Copies the public key to the remote device for public key authentication.
These commands form the foundation of SSH operations in RemoteIoT SSH example and are indispensable for managing IoT networks.
Advanced SSH Commands
In addition to basic commands, advanced SSH features such as port forwarding and tunneling can enhance the functionality of RemoteIoT SSH example. These features enable secure access to internal networks and services, further expanding the capabilities of SSH in IoT environments.
Securing RemoteIoT with SSH
While SSH provides robust security features, additional measures can further enhance the protection of RemoteIoT SSH example. These include:
- Disabling Password Authentication: Enabling public key authentication only reduces the risk of brute-force attacks.
- Changing Default Port: Configuring SSH to use a non-standard port can deter casual attackers.
- Implementing Firewall Rules: Restricting access to specific IP addresses or networks adds an extra layer of security.
- Regular Auditing: Monitoring SSH logs and reviewing access attempts can help identify and mitigate potential threats.
By implementing these best practices, organizations can significantly strengthen the security of their RemoteIoT SSH example and protect against cyber threats.
Troubleshooting SSH Connection
Occasionally, SSH connections in RemoteIoT SSH example may encounter issues. Common problems and their solutions include:
- Connection Timeout: Verify that the remote device is reachable and the SSH service is running.
- Authentication Failure: Ensure that the correct credentials or keys are being used and that the SSH configuration allows the specified authentication method.
- Permission Denied: Check file and directory permissions on the remote device to ensure proper access rights.
Addressing these issues promptly ensures uninterrupted access to IoT devices in RemoteIoT SSH example.
Diagnostic Tools
Using diagnostic tools such as netstat, telnet, and sshd -d can help identify and resolve SSH connection problems in RemoteIoT SSH example. These tools provide valuable insights into network and service status, aiding in effective troubleshooting.
Advanced SSH Features for RemoteIoT
Beyond basic functionality, SSH offers advanced features that can enhance the capabilities of RemoteIoT SSH example. These include:
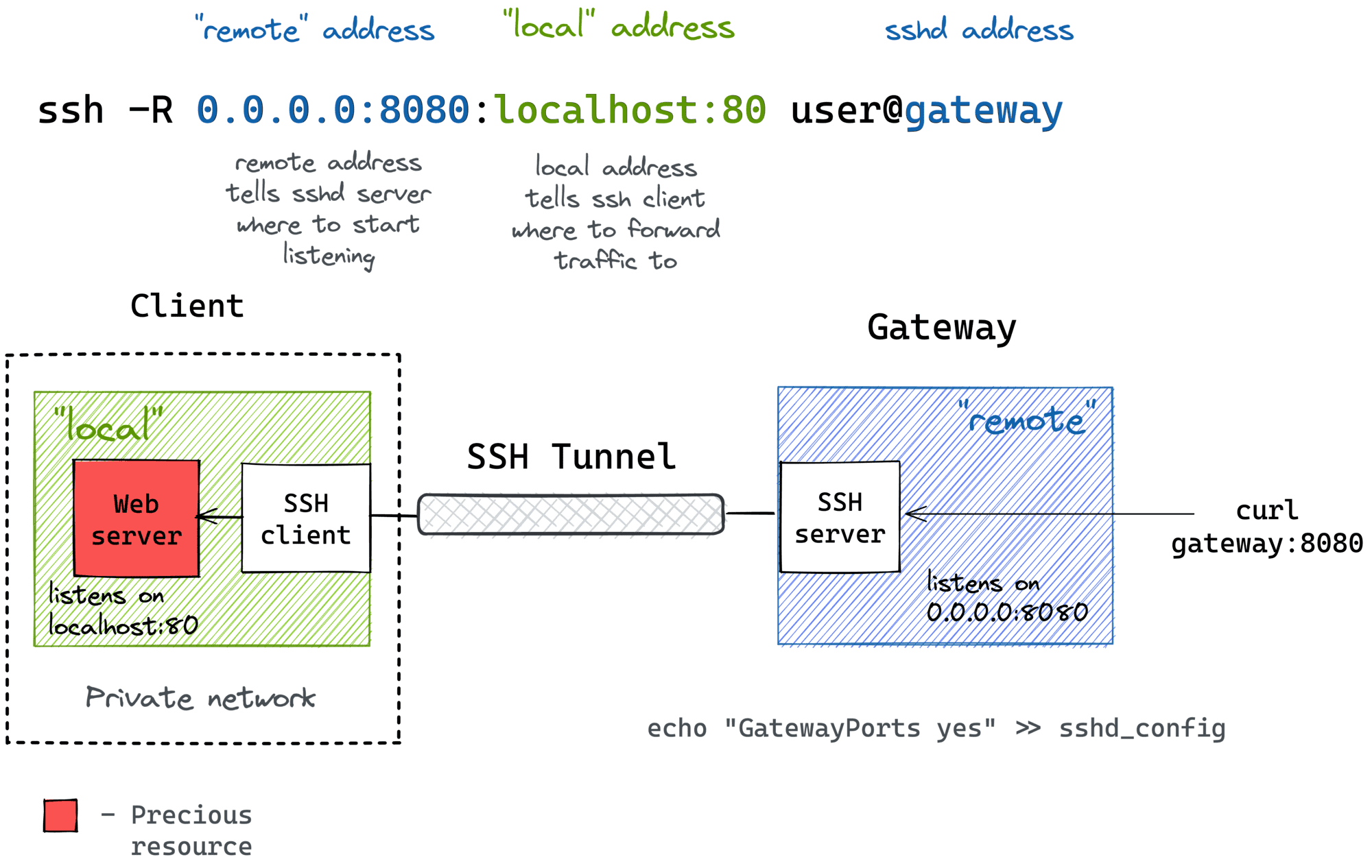
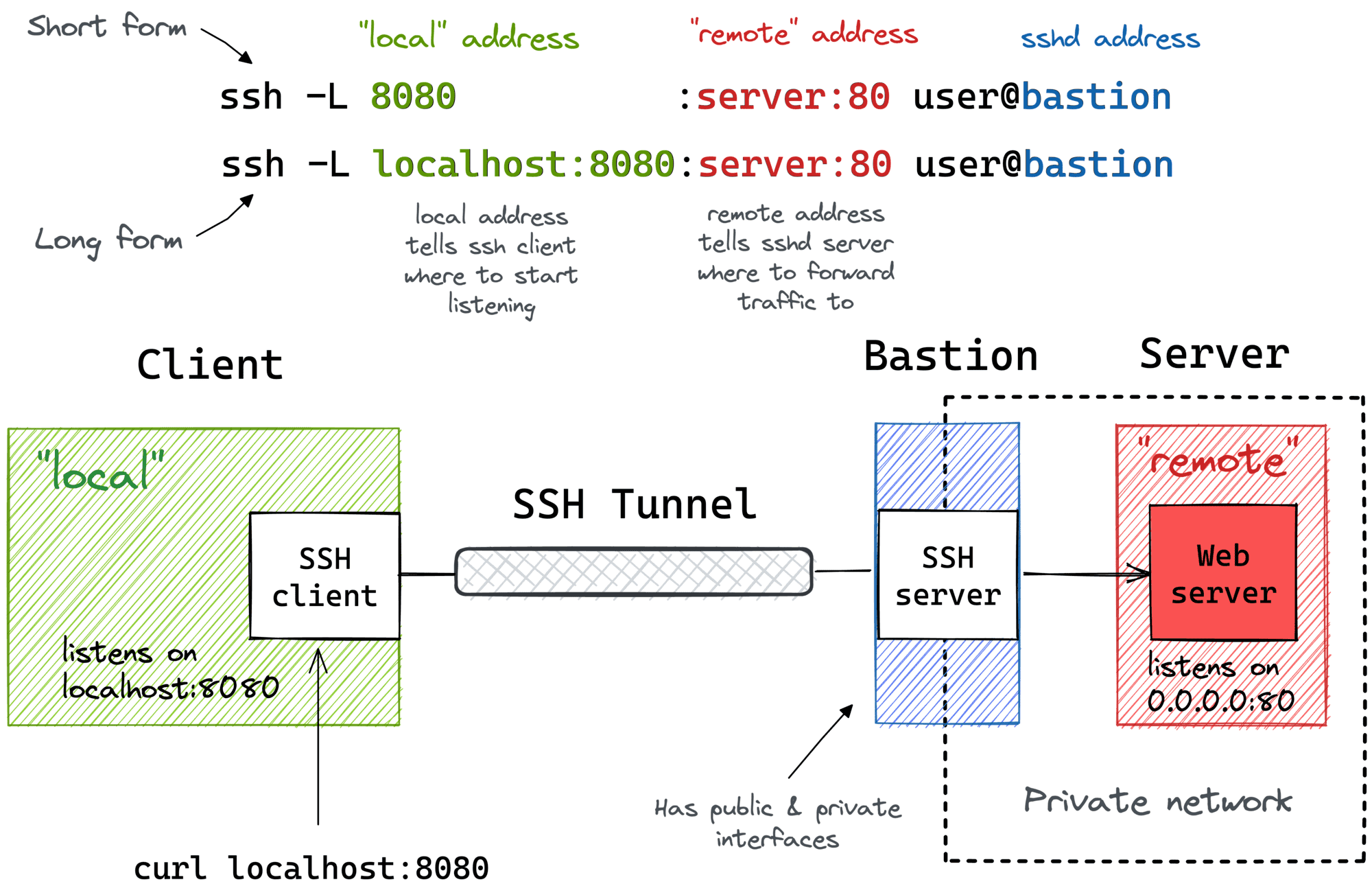
- SSH Tunneling: Creates a secure channel for transmitting data between devices, enabling access to internal networks and services.
- Agent Forwarding: Allows the use of local SSH keys for authenticating with multiple devices, simplifying access management.
- SSH Multiplexing: Reduces connection overhead by reusing existing SSH sessions, improving performance and efficiency.
Leveraging these advanced features can significantly improve the functionality and security of RemoteIoT SSH example.
Implementing SSH Tunneling
SSH tunneling is a powerful tool for securing data transmissions in RemoteIoT SSH example. By creating encrypted channels between devices, organizations can protect sensitive information and access internal resources securely.
Real-World RemoteIoT SSH Examples
Several industries have successfully implemented RemoteIoT SSH example to enhance their IoT operations. For instance:
- Manufacturing: Companies use SSH to remotely monitor and control industrial equipment, improving efficiency and reducing downtime.
- Healthcare: Healthcare providers leverage SSH for secure access to medical devices, ensuring patient data privacy and compliance with regulations.
- Smart Cities: Municipalities implement SSH in IoT networks to manage infrastructure such as traffic lights and environmental sensors.
These examples demonstrate the versatility and effectiveness of RemoteIoT SSH example across various sectors.
Conclusion and Next Steps
RemoteIoT SSH example plays a vital role in enabling secure and efficient IoT operations. By understanding the principles and applications of SSH, organizations can harness its power to protect their IoT networks and enhance operational capabilities. This guide has provided a comprehensive overview of RemoteIoT SSH example, covering its implementation, security measures, and real-world applications.
To further explore this topic, consider experimenting with SSH configurations and exploring advanced features. Additionally, stay informed about the latest developments in IoT security to ensure your implementations remain up-to-date and effective.
We invite you to share your thoughts and experiences with RemoteIoT SSH example in the comments section below. Your feedback helps us improve and expand our content. Don't forget to explore other articles on our site for more insights into IoT and related technologies.
References:
- OpenSSH Official Website: https://www.openssh.com/
- IoT Security Best Practices: https://www.nist.gov/
- SSH Protocol Standards: https://tools.ietf.org/html/rfc4251