Managing SSH keys for remote IoT devices has become a critical aspect of cybersecurity in the modern digital landscape. As the Internet of Things (IoT) continues to expand, securing communication between devices and servers is more important than ever. Proper SSH key management ensures that unauthorized access is minimized, while maintaining seamless connectivity for legitimate users.
With the rise of remote work and distributed systems, organizations must adopt robust strategies for managing SSH keys. This guide explores the best practices, tools, and methodologies to optimize SSH key management for IoT devices, ensuring your network remains secure and efficient.
In this article, we will delve into the importance of SSH key management, discuss potential vulnerabilities, and provide actionable insights to help you implement a secure and scalable system. By the end, you'll have a clear understanding of how to manage SSH keys effectively for remote IoT deployments.
Read also:Maximizing Insurance Marketing With A Top Ppc Agency For Insurance Sector
Table of Contents
- Introduction to Remote IoT SSH Key Management
- Why SSH Key Management Matters in IoT
- Common Vulnerabilities in SSH Key Management
- Best Practices for SSH Key Management
- Top Tools for Managing SSH Keys
- Scaling SSH Key Management for Large IoT Networks
- Automating SSH Key Management Processes
- Enhancing Security with Advanced Techniques
- Compliance Considerations for SSH Key Management
- The Future of SSH Key Management in IoT
Introduction to Remote IoT SSH Key Management
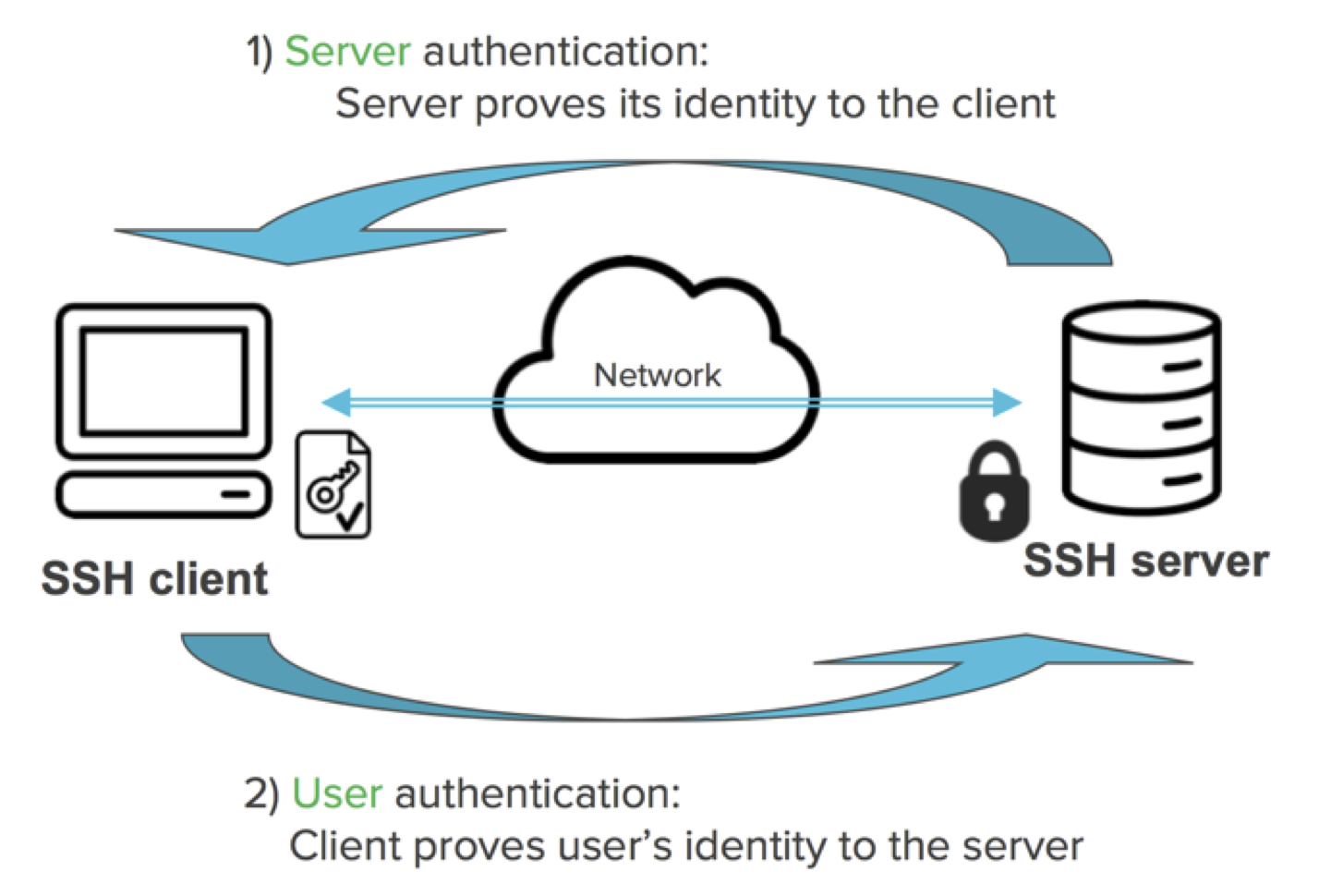
SSH (Secure Shell) keys play a pivotal role in securing remote access to IoT devices. These cryptographic keys authenticate users and devices, ensuring that only authorized parties can access sensitive systems. Effective SSH key management is essential for maintaining the integrity and security of IoT networks.
As IoT devices continue to proliferate, the complexity of managing SSH keys increases exponentially. Organizations must implement robust strategies to address challenges such as key rotation, expiration, and revocation. By prioritizing SSH key management, businesses can protect their assets and reduce the risk of cyberattacks.
Remote IoT SSH key management involves several key components, including key generation, distribution, and monitoring. This section will provide an overview of these components and explain why they are critical for securing IoT ecosystems.
Why SSH Key Management Matters in IoT
In the realm of IoT, SSH key management is not just a best practice—it's a necessity. Without proper management, SSH keys can become a liability, exposing networks to unauthorized access and data breaches. According to a report by the Ponemon Institute, poorly managed SSH keys are responsible for over 60% of security incidents in enterprise environments.
Impact of Poor SSH Key Management
Poor SSH key management can lead to several significant issues, including:
- Uncontrolled access to critical systems
- Increased risk of data breaches
- Compliance violations
- Operational inefficiencies
By implementing a comprehensive SSH key management strategy, organizations can mitigate these risks and ensure the security of their IoT infrastructure.
Read also:Discover The Best Streameast Alternative Reddit Has To Offer A Comprehensive Guide
Common Vulnerabilities in SSH Key Management
Despite the importance of SSH key management, many organizations struggle to address common vulnerabilities. These vulnerabilities can arise from outdated practices, lack of awareness, or insufficient tools. Below are some of the most prevalent vulnerabilities:
Expired Keys
Expired SSH keys can create security gaps if not properly monitored and replaced. Keys that remain active beyond their intended lifespan increase the risk of unauthorized access.
Orphaned Keys
Orphaned keys occur when employees leave an organization but their keys remain active. These keys can be exploited by malicious actors, compromising network security.
Inadequate Key Rotation
Failing to rotate SSH keys regularly can expose networks to long-term vulnerabilities. Key rotation ensures that even if a key is compromised, the damage is limited to a specific timeframe.
To address these vulnerabilities, organizations must adopt proactive measures, such as implementing automated key management systems and conducting regular audits.
Best Practices for SSH Key Management
Effective SSH key management requires adherence to best practices that prioritize security, efficiency, and scalability. Below are some key practices to consider:
Key Generation
Generate strong, unique SSH keys using modern cryptographic algorithms. Avoid reusing keys across multiple devices to minimize risk.
Key Distribution
Use secure methods for distributing SSH keys, such as encrypted channels or secure key management systems. Ensure that only authorized personnel have access to the keys.
Key Monitoring
Implement continuous monitoring of SSH keys to detect and respond to suspicious activities promptly. Use tools that provide real-time alerts for unauthorized access attempts.
By following these best practices, organizations can significantly enhance the security of their IoT networks and reduce the likelihood of security breaches.
Top Tools for Managing SSH Keys
Several tools are available to streamline SSH key management for IoT devices. These tools offer features such as key generation, distribution, and monitoring, making it easier for organizations to maintain secure systems. Below are some of the top tools in the market:
HashiCorp Vault
HashiCorp Vault is a popular tool for managing secrets, including SSH keys. It provides robust features for key rotation, encryption, and access control, ensuring secure SSH key management.
SSHKeychain
SSHKeychain is a lightweight tool designed specifically for managing SSH keys in IoT environments. It offers features such as key generation, storage, and distribution, making it an ideal choice for small to medium-sized organizations.
Keycloak
Keycloak is an open-source identity and access management solution that supports SSH key management. It integrates seamlessly with existing systems, providing a centralized platform for managing keys across multiple devices.
When selecting a tool for SSH key management, consider factors such as scalability, ease of use, and integration capabilities to ensure it meets your organization's needs.
Scaling SSH Key Management for Large IoT Networks
As IoT networks grow in size and complexity, scaling SSH key management becomes a significant challenge. Organizations must implement strategies that can handle thousands—or even millions—of devices without compromising security or performance.
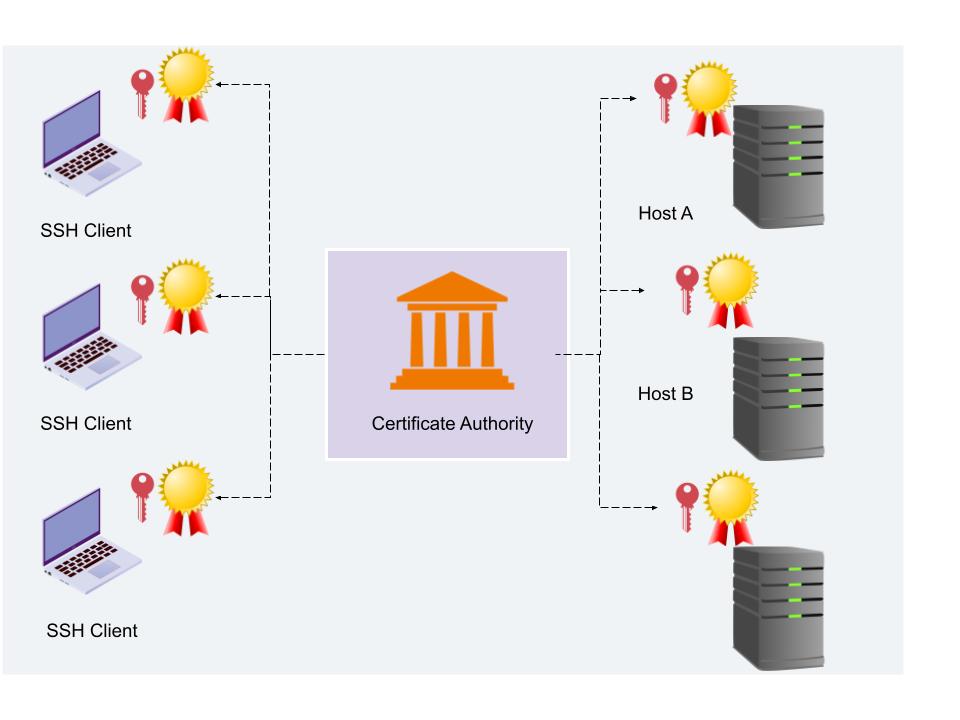
Centralized Management
Centralized management systems provide a single point of control for managing SSH keys across large IoT networks. These systems enable organizations to monitor, rotate, and revoke keys efficiently, reducing the risk of mismanagement.
Automated Processes
Automation is key to scaling SSH key management. By automating key generation, distribution, and rotation, organizations can reduce the burden on IT staff and ensure consistent adherence to security policies.
Scaling SSH key management requires a combination of technology, process, and people. Organizations must invest in the right tools and training to ensure their systems remain secure and efficient as they grow.
Automating SSH Key Management Processes
Automation plays a crucial role in modern SSH key management. By automating repetitive tasks, organizations can improve efficiency, reduce errors, and enhance security. Below are some key areas where automation can be applied:
Key Generation
Automate the generation of SSH keys to ensure they meet organizational standards and are created consistently across all devices.
Key Rotation
Implement automated key rotation schedules to ensure keys are updated regularly, minimizing the risk of compromise.
Access Control
Automate access control policies to restrict key usage to authorized users and devices, reducing the likelihood of unauthorized access.
Automation not only simplifies SSH key management but also enables organizations to respond quickly to security threats and compliance requirements.
Enhancing Security with Advanced Techniques
While basic SSH key management practices are essential, organizations can further enhance security by adopting advanced techniques. These techniques include:
Multi-Factor Authentication
Implement multi-factor authentication (MFA) to add an extra layer of security to SSH key access. MFA requires users to provide two or more verification factors before gaining access to sensitive systems.
Cryptographic Algorithms
Use modern cryptographic algorithms, such as RSA 4096 or Ed25519, to ensure the highest level of security for SSH keys. These algorithms provide stronger encryption and are more resistant to attacks.
Behavioral Analytics
Integrate behavioral analytics into your SSH key management system to detect and respond to suspicious activities in real time. This proactive approach can help prevent security breaches before they occur.
By combining these advanced techniques with traditional practices, organizations can create a robust security framework for their IoT networks.
Compliance Considerations for SSH Key Management
Compliance with industry standards and regulations is a critical aspect of SSH key management. Organizations must ensure their practices align with relevant laws and guidelines to avoid penalties and reputational damage.
General Data Protection Regulation (GDPR)
GDPR requires organizations to implement measures to protect personal data, including SSH keys. Compliance involves encrypting keys, controlling access, and maintaining detailed records of key usage.
Payment Card Industry Data Security Standard (PCI DSS)
PCI DSS mandates strict controls for managing SSH keys in payment systems. This includes regular key rotation, access restrictions, and audit logging.
By addressing compliance requirements, organizations can ensure their SSH key management practices meet legal and regulatory standards, reducing the risk of non-compliance.
The Future of SSH Key Management in IoT
As technology continues to evolve, the future of SSH key management in IoT looks promising. Emerging trends such as quantum computing, artificial intelligence, and blockchain are set to revolutionize the way organizations manage SSH keys.
Quantum-Resistant Cryptography
Quantum computing poses a significant threat to traditional cryptographic algorithms. Organizations are exploring quantum-resistant cryptography to future-proof their SSH key management systems.
AI-Driven Security
Artificial intelligence is being used to enhance SSH key management by analyzing patterns, detecting anomalies, and predicting potential threats. AI-driven systems can provide real-time insights and recommendations to improve security.
The future of SSH key management in IoT will be shaped by innovation and collaboration. By staying ahead of technological advancements, organizations can ensure their systems remain secure and resilient in the face of evolving threats.
Kesimpulan
Managing SSH keys for remote IoT devices is a critical component of cybersecurity. By implementing best practices, leveraging advanced tools, and addressing compliance requirements, organizations can secure their networks and protect sensitive data. This guide has provided actionable insights into the best remote IoT SSH key management strategies, ensuring your systems remain robust and secure.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site for more insights into cybersecurity and IoT. Together, let's build a safer digital future.