In the rapidly evolving world of technology, the need for secure remote access to IoT devices has never been more critical. Best remote IoT device SSH solutions are essential for ensuring secure communication between devices and networks, especially as more organizations adopt remote work models. With the increasing number of cyber threats, securing IoT devices has become a top priority for businesses and individuals alike.
As more devices become interconnected, the demand for robust security measures continues to grow. SSH (Secure Shell) protocols provide a reliable way to establish encrypted connections, ensuring that sensitive data remains protected from unauthorized access. This article will delve into the best remote IoT device SSH solutions available today, helping you make informed decisions for your specific needs.
Whether you're a seasoned IT professional or a beginner exploring the realm of IoT, understanding the best practices for securing your devices through SSH is crucial. By the end of this article, you'll have a comprehensive understanding of the best remote IoT device SSH solutions and how to implement them effectively in your network infrastructure.
Read also:How Much Is Dave Gahan Worth Discover The Net Worth Of Depeche Modes Iconic Frontman
Understanding the Importance of Remote IoT Device SSH
Remote IoT device SSH plays a pivotal role in maintaining secure communication between devices and networks. In today's interconnected world, IoT devices are used in various sectors, from healthcare to manufacturing, making it imperative to secure these devices against potential cyber threats.
SSH protocols provide a secure channel for remote access, encrypting all data transmitted between devices. This ensures that sensitive information remains protected from unauthorized access, reducing the risk of data breaches and cyberattacks. Understanding the importance of SSH in IoT devices is crucial for maintaining network security and protecting valuable data.
Key Features of Best Remote IoT Device SSH Solutions
When evaluating the best remote IoT device SSH solutions, it's essential to consider several key features that contribute to their effectiveness and reliability.
1. Encryption Strength
One of the most critical aspects of any SSH solution is its encryption strength. Strong encryption algorithms ensure that all data transmitted between devices remains secure and protected from interception.
2. Authentication Methods
Robust authentication methods, such as two-factor authentication (2FA) and public key authentication, enhance the security of SSH connections. These methods ensure that only authorized users can access IoT devices remotely.
3. Scalability
The best remote IoT device SSH solutions should be scalable, allowing businesses to accommodate growing numbers of devices and users without compromising performance or security.
Read also:Ty Dane Gonzalez A Rising Star In The Entertainment Industry
Top Remote IoT Device SSH Solutions
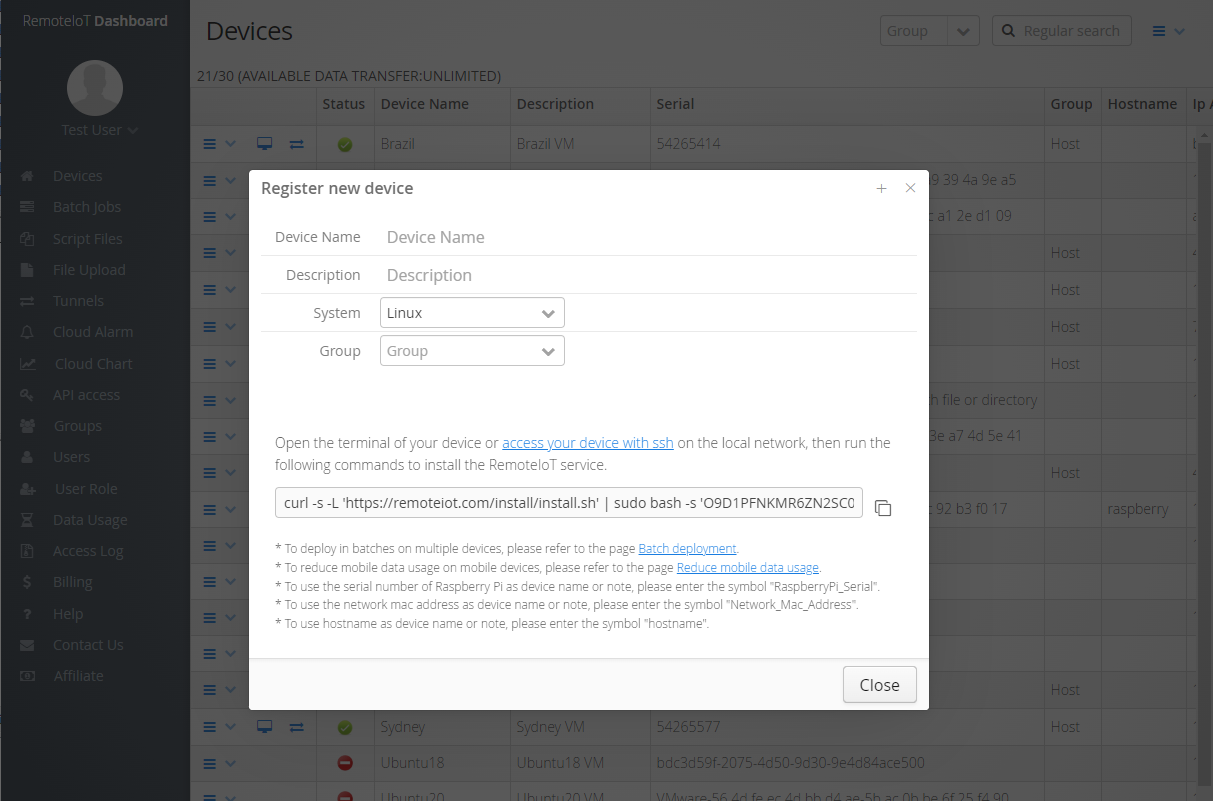
Here are some of the top remote IoT device SSH solutions available today, each offering unique features and benefits:
1. OpenSSH
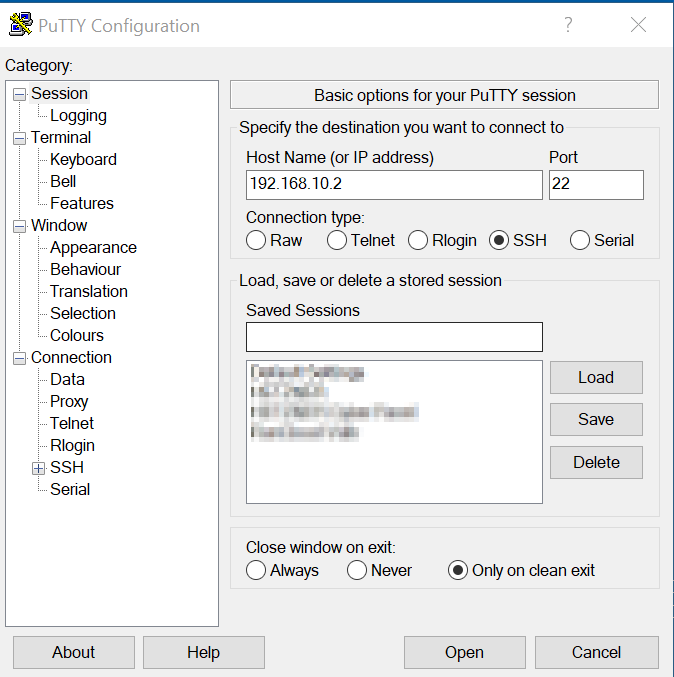
OpenSSH is one of the most widely used SSH solutions, known for its robust security features and open-source nature. It supports various encryption algorithms and authentication methods, making it a versatile choice for securing IoT devices.
2. Dropbear SSH
Dropbear SSH is a lightweight SSH server and client designed for resource-constrained environments. It's ideal for IoT devices with limited processing power and memory, offering a reliable and secure solution for remote access.
3. Bitvise SSH
Bitvise SSH provides a user-friendly interface and advanced security features, making it a popular choice for businesses and individuals alike. Its support for multiple authentication methods and encryption algorithms ensures secure remote access to IoT devices.
How to Choose the Best Remote IoT Device SSH Solution
Selecting the right SSH solution for your IoT devices requires careful consideration of several factors:
- Security requirements: Evaluate the encryption strength and authentication methods offered by each solution to ensure they meet your security needs.
- Scalability: Choose a solution that can accommodate your growing network of IoT devices without compromising performance or security.
- Compatibility: Ensure the SSH solution is compatible with your existing infrastructure and devices.
Best Practices for Implementing Remote IoT Device SSH
To ensure the best possible security for your IoT devices, follow these best practices when implementing SSH:
1. Use Strong Passwords
Create strong, complex passwords and avoid using default credentials. Regularly update passwords to enhance security.
2. Enable Public Key Authentication
Public key authentication provides an additional layer of security by requiring users to have a private key to access devices.
3. Regularly Update SSH Software
Keep your SSH software up to date with the latest security patches and updates to protect against vulnerabilities.
Common Challenges in Remote IoT Device SSH
While SSH offers a secure way to access IoT devices remotely, there are some challenges to consider:
1. Cybersecurity Threats
As cyber threats continue to evolve, it's essential to stay vigilant and implement the latest security measures to protect your devices.
2. Resource Constraints
Some IoT devices have limited processing power and memory, making it challenging to implement resource-intensive SSH solutions.
Data and Statistics on Remote IoT Device SSH
According to recent studies, the global IoT security market is expected to grow significantly in the coming years, driven by the increasing adoption of IoT devices and the need for robust security solutions. The use of SSH in securing IoT devices is expected to play a crucial role in this growth.
Source: [Statista](https://www.statista.com)
Future Trends in Remote IoT Device SSH
As technology continues to advance, several trends are emerging in the realm of remote IoT device SSH:
- Quantum-resistant encryption: With the advent of quantum computing, researchers are exploring new encryption methods that can withstand attacks from quantum computers.
- AI-driven security: Artificial intelligence is being used to enhance security by detecting and responding to potential threats in real time.
Conclusion
In conclusion, securing IoT devices through the best remote IoT device SSH solutions is essential for maintaining network security and protecting valuable data. By understanding the key features, challenges, and best practices associated with SSH, you can make informed decisions to safeguard your devices against potential cyber threats.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into the world of IoT and cybersecurity. Together, let's build a safer and more secure digital future!
Table of Contents
- Understanding the Importance of Remote IoT Device SSH
- Key Features of Best Remote IoT Device SSH Solutions
- Top Remote IoT Device SSH Solutions
- How to Choose the Best Remote IoT Device SSH Solution
- Best Practices for Implementing Remote IoT Device SSH
- Common Challenges in Remote IoT Device SSH
- Data and Statistics on Remote IoT Device SSH
- Future Trends in Remote IoT Device SSH
- Conclusion