In today's interconnected world, the Internet of Things (IoT) continues to grow exponentially, bringing innovation and convenience to businesses and individuals alike. However, with this growth comes the critical need for secure remote connectivity, especially when managing IoT devices through platforms like AWS VPC and Raspberry Pi. Ensuring secure communication is no longer optional—it’s essential.
As companies increasingly rely on IoT devices for automation, data collection, and remote monitoring, they must prioritize secure connections to prevent unauthorized access, data breaches, and cyberattacks. The integration of AWS Virtual Private Cloud (VPC) and Raspberry Pi offers a powerful solution for building secure IoT environments. This article delves into the strategies and best practices for securely connecting remote IoT devices using AWS VPC and Raspberry Pi.
Whether you're a developer, IT professional, or an enthusiast looking to enhance your IoT setup, this guide provides comprehensive insights into setting up secure connections, managing configurations, and downloading necessary resources to ensure your IoT ecosystem remains robust and protected.
Read also:Lor X Pleads Guilty A Comprehensive Analysis Of The Case
Table of Contents
- Introduction to IoT Security
- Understanding AWS VPC
- Raspberry Pi's Role in IoT
- Bi-Directional Secure Connection
- Setting Up VPC for IoT
- Secure Authentication Methods
- Data Encryption Techniques
- Remote Management of IoT Devices
- Downloading Necessary Resources
- Best Practices for IoT Security
- Conclusion
Introduction to IoT Security
The Internet of Things (IoT) has revolutionized how we interact with technology, enabling devices to communicate and share data seamlessly. However, this interconnectedness introduces vulnerabilities that malicious actors can exploit. Securely connecting remote IoT devices is paramount to safeguarding sensitive information and maintaining operational integrity.
IoT security encompasses various aspects, including device authentication, data encryption, network security, and secure communication protocols. By leveraging AWS VPC and Raspberry Pi, businesses can create a secure IoT environment that minimizes risks and maximizes efficiency.
Understanding the fundamental principles of IoT security is the first step toward building a resilient infrastructure. This section explores the importance of security in IoT ecosystems and highlights common threats that must be addressed.
Understanding AWS VPC
AWS Virtual Private Cloud (VPC) is a cornerstone of secure cloud computing, offering a logically isolated section of the AWS Cloud where users can launch resources in a virtual network. By utilizing AWS VPC, organizations can define their own IP address range, create subnets, and configure route tables to ensure secure communication between IoT devices.
Key Features of AWS VPC
- Subnet Configuration: Divide your network into smaller segments for better control and security.
- Security Groups: Implement firewall rules to control inbound and outbound traffic to your IoT devices.
- Network Access Control Lists (ACLs): Add an additional layer of security by defining rules for traffic entering or leaving subnets.
- Private Subnets: Protect sensitive devices by isolating them from public internet access.
By integrating AWS VPC into your IoT setup, you can ensure that only authorized devices and users have access to your network, reducing the risk of unauthorized access.
Raspberry Pi's Role in IoT
Raspberry Pi has emerged as a popular choice for IoT projects due to its affordability, versatility, and ease of use. This compact single-board computer can serve as a gateway for IoT devices, enabling secure communication between sensors, actuators, and cloud platforms.
Read also:Holt Mccallany Wife 2024 A Comprehensive Look Into The Life Of The Renowned Actor And His Relationship
With Raspberry Pi, developers can implement advanced security features such as encryption, authentication, and secure data transfer. Additionally, its compatibility with various programming languages and libraries makes it an ideal platform for building custom IoT solutions.
Raspberry Pi Specifications
| Feature | Details |
|---|---|
| Processor | Quad-core ARM Cortex-A53 |
| RAM | 4GB LPDDR4-3200 |
| Storage | MicroSD card |
| Connectivity | Wi-Fi, Bluetooth, Ethernet |
Bi-Directional Secure Connection
Establishing a bi-directional secure connection is crucial for ensuring that data transmitted between IoT devices and the cloud remains protected. This involves implementing robust authentication mechanisms and encryption protocols to prevent eavesdropping and tampering.
By utilizing AWS VPC and Raspberry Pi, users can create a secure tunnel for communication, ensuring that both incoming and outgoing data is encrypted and authenticated. This section explores the technologies and tools available for setting up bi-directional secure connections, including SSL/TLS, SSH, and MQTT.
Setting Up VPC for IoT
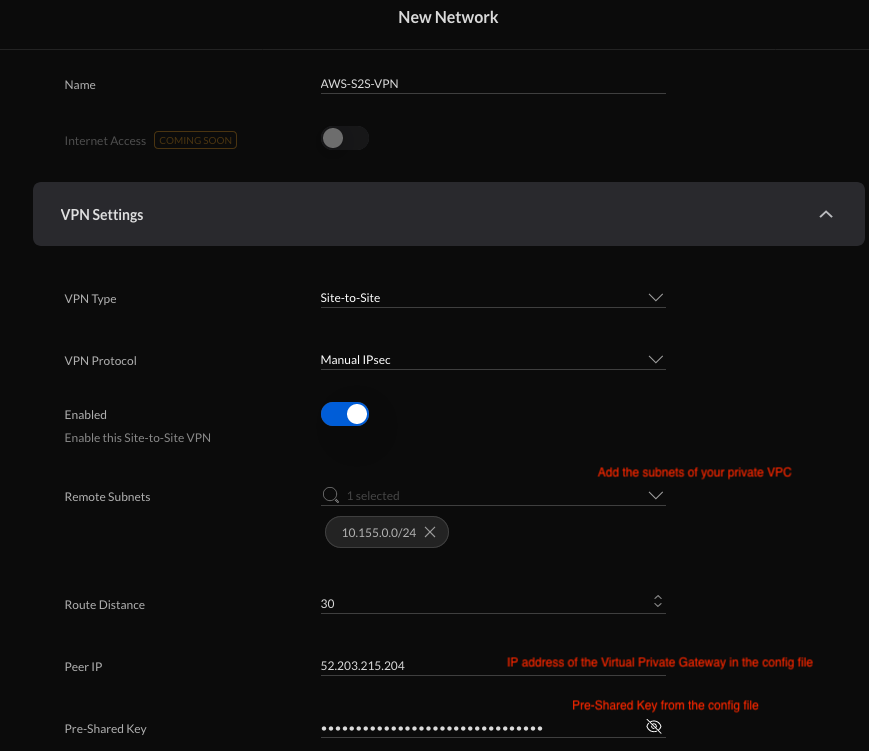
Setting up AWS VPC for IoT involves several steps, including defining your network topology, configuring subnets, and implementing security measures. This process ensures that your IoT devices operate in a secure and isolated environment, minimizing the risk of unauthorized access.
Steps to Set Up AWS VPC
- Create a new VPC and define your IP address range.
- Configure subnets for public and private access.
- Set up security groups and network ACLs to control traffic.
- Launch IoT devices within the VPC and configure routing rules.
By following these steps, you can create a secure and scalable IoT environment that supports seamless communication between devices and the cloud.
Secure Authentication Methods
Authentication is a critical component of IoT security, ensuring that only authorized devices and users can access your network. Implementing secure authentication methods such as OAuth 2.0, X.509 certificates, and multi-factor authentication (MFA) can significantly enhance the security of your IoT ecosystem.
When using Raspberry Pi as a gateway, developers can leverage its processing power to implement advanced authentication mechanisms. This section discusses the benefits and implementation of various authentication methods, providing practical examples and best practices.
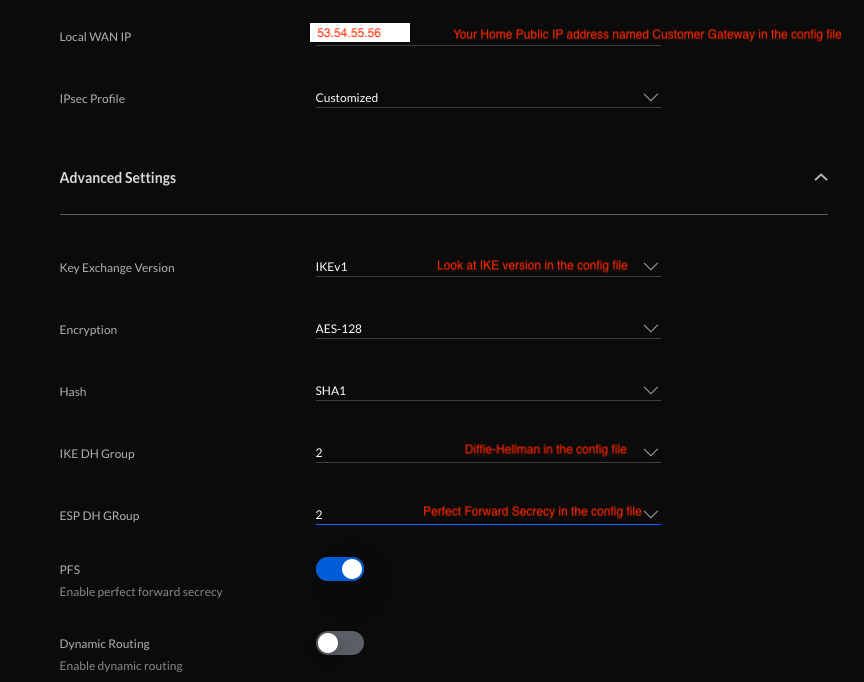
Data Encryption Techniques
Data encryption is essential for protecting sensitive information transmitted between IoT devices and the cloud. By encrypting data at rest and in transit, organizations can ensure that even if data is intercepted, it remains unreadable to unauthorized parties.
Popular Encryption Protocols
- SSL/TLS: Secure communication between devices and servers.
- AES: Advanced encryption standard for encrypting data at rest.
- MQTT-SN: Lightweight protocol for secure IoT communication.
This section delves into the technical aspects of data encryption, providing guidance on selecting the appropriate encryption protocols for your IoT setup.
Remote Management of IoT Devices
Efficient remote management is vital for maintaining the security and functionality of IoT devices. By leveraging AWS VPC and Raspberry Pi, administrators can monitor and manage their IoT ecosystem from anywhere in the world, ensuring that devices remain secure and operational.
This section explores the tools and techniques available for remote management, including AWS IoT Core, SSH, and web-based dashboards. It also highlights the importance of regular updates and patches to address potential vulnerabilities.
Downloading Necessary Resources
To implement a secure IoT environment using AWS VPC and Raspberry Pi, you will need to download several resources, including software libraries, configuration files, and documentation. This section provides links to official resources and guides to help you get started.
Recommended Downloads
By accessing these resources, you can gain a deeper understanding of the technologies involved and implement best practices for secure IoT connectivity.
Best Practices for IoT Security
Implementing best practices for IoT security is essential for protecting your devices and data from potential threats. This section provides practical advice on securing your IoT ecosystem, including regular updates, secure coding practices, and network segmentation.
Key Best Practices
- Regular Updates: Keep firmware and software up to date to address known vulnerabilities.
- Network Segmentation: Isolate IoT devices from other networks to minimize risk.
- Secure Coding: Follow secure coding practices when developing IoT applications.
By adhering to these best practices, you can create a secure and resilient IoT environment that meets the demands of modern businesses.
Conclusion
Securing remote IoT connections is a critical aspect of modern technology, and integrating AWS VPC and Raspberry Pi offers a powerful solution for building secure IoT ecosystems. By following the strategies and best practices outlined in this article, you can ensure that your IoT devices remain protected from potential threats.
We encourage you to explore the resources provided and implement the techniques discussed to enhance the security of your IoT setup. Feel free to leave a comment or share this article with others who may find it useful. Together, we can create a safer and more connected world.