In today's interconnected world, securely connect remote IoT VPC Raspberry Pi has become a critical need for businesses and individuals alike. As IoT devices continue to grow in popularity, ensuring secure communication between these devices and cloud-based networks is more important than ever. In this article, we will explore the best practices and techniques to establish a secure connection for IoT devices, particularly focusing on Raspberry Pi and Virtual Private Cloud (VPC).
As more organizations adopt IoT solutions, the demand for secure remote access to these devices has increased exponentially. This guide will cover everything you need to know about securing your IoT VPC connections using Raspberry Pi, including setting up secure tunnels, managing encryption, and ensuring data privacy.
Whether you're a developer, network administrator, or hobbyist, this article will provide you with actionable insights and practical steps to enhance the security of your IoT infrastructure. Let's dive into the world of secure IoT connections and explore how to protect your devices and data.
Read also:No Limit Drag Racing 20 The Ultimate Guide To Mastering The Game
Table of Contents
- Introduction to IoT Security
- Understanding Raspberry Pi Basics
- What is Virtual Private Cloud (VPC)?
- Methods for Securely Connect Remote IoT VPC Raspberry Pi
- Encryption Techniques for IoT Devices
- Enhancing Network Security with Firewalls
- Authentication Protocols for IoT
- Best Practices for IoT Security
- Troubleshooting Common IoT Security Issues
- Conclusion and Next Steps
Introduction to IoT Security
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices are everywhere. However, this widespread adoption brings significant security challenges. One of the primary concerns is how to securely connect remote IoT VPC Raspberry Pi devices to ensure data integrity and privacy.
IoT security involves protecting IoT devices and the networks they connect to from unauthorized access, data breaches, and cyberattacks. A secure IoT environment requires robust authentication, encryption, and network segmentation. In this section, we will explore the importance of IoT security and its impact on modern infrastructure.
Why IoT Security Matters
IoT devices often collect sensitive data, making them prime targets for hackers. Without proper security measures, attackers can exploit vulnerabilities in IoT devices to gain unauthorized access to networks. This can lead to data breaches, financial losses, and reputational damage. By understanding the risks and implementing secure practices, you can protect your IoT infrastructure effectively.
Understanding Raspberry Pi Basics
Raspberry Pi is a popular single-board computer widely used for IoT applications. Its affordability, versatility, and ease of use make it an ideal choice for developers and hobbyists alike. When it comes to securely connect remote IoT VPC Raspberry Pi, understanding its architecture and capabilities is essential.
Raspberry Pi can act as a gateway for IoT devices, enabling them to communicate securely with cloud-based services. By leveraging its powerful hardware and software capabilities, you can create a robust IoT infrastructure that meets modern security standards.
Key Features of Raspberry Pi
- Compact and energy-efficient design
- Support for multiple operating systems
- Extensive community support and resources
- Compatibility with various IoT protocols
What is Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a private network hosted within a public cloud environment. It provides a secure and isolated space for running cloud-based applications and services. When it comes to securely connect remote IoT VPC Raspberry Pi, a VPC ensures that data communication remains private and protected from external threats.
Read also:Did Michael J Fox Die The Truth Behind The Rumors
By using a VPC, you can control access to your IoT devices, manage network traffic, and implement advanced security features such as firewalls and intrusion detection systems. This section will delve deeper into the benefits of using a VPC for IoT applications and how it enhances security.
Benefits of Using VPC for IoT
- Enhanced data privacy and security
- Flexible network configuration options
- Scalability for growing IoT deployments
- Integration with cloud-based services
Methods for Securely Connect Remote IoT VPC Raspberry Pi
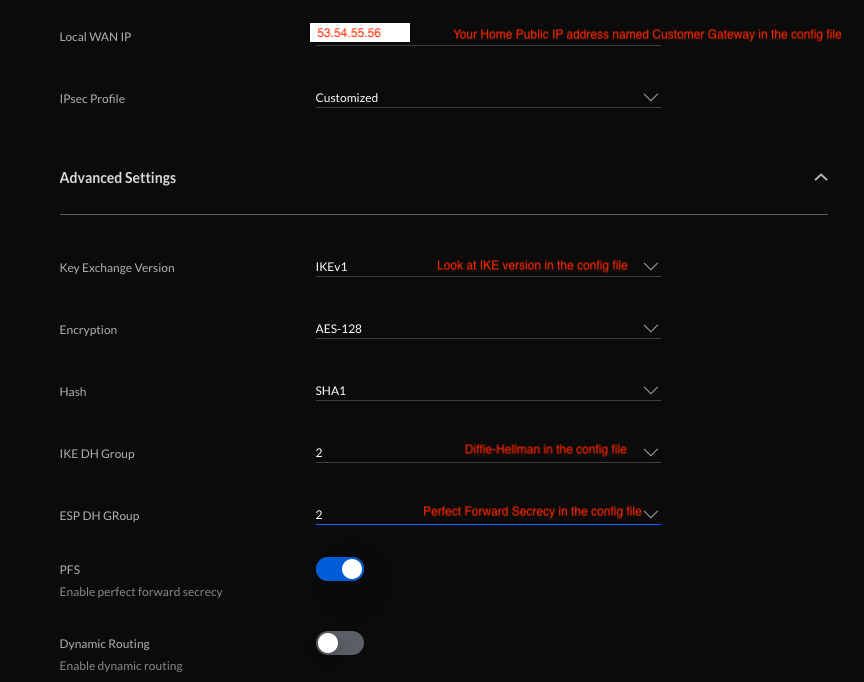
There are several methods to establish a secure connection between IoT devices and a VPC. These methods involve using encryption, secure tunnels, and authentication protocols to ensure data integrity and privacy. In this section, we will explore some of the most effective techniques for securely connect remote IoT VPC Raspberry Pi.
1. SSH Tunneling
SSH tunneling is a popular method for creating secure connections between devices. By encrypting data transmitted over the network, SSH ensures that sensitive information remains protected from eavesdropping and interception. Raspberry Pi supports SSH out of the box, making it an ideal platform for implementing secure IoT connections.
2. SSL/TLS Encryption
SSL/TLS encryption is another widely used technique for securing IoT communications. It involves encrypting data at the application layer, ensuring that even if the data is intercepted, it cannot be read without the proper decryption keys. This method is particularly useful for securing web-based IoT applications.
Encryption Techniques for IoT Devices
Encryption plays a crucial role in securing IoT communications. By encrypting data both in transit and at rest, you can protect sensitive information from unauthorized access. In this section, we will discuss some of the most effective encryption techniques for IoT devices, including symmetric and asymmetric encryption algorithms.
Symmetric Encryption
Symmetric encryption uses the same key for both encryption and decryption. It is fast and efficient, making it ideal for securing IoT device communications. However, securely managing encryption keys can be challenging, especially in large-scale deployments.
Asymmetric Encryption
Asymmetric encryption uses a pair of keys—one public and one private—for encryption and decryption. This method provides enhanced security, as the private key remains securely stored on the device. However, it is computationally more intensive than symmetric encryption, making it less suitable for resource-constrained IoT devices.
Enhancing Network Security with Firewalls
Firewalls are an essential component of network security. They act as a barrier between your IoT devices and the internet, controlling incoming and outgoing traffic based on predefined rules. In this section, we will explore how firewalls can enhance the security of your IoT VPC infrastructure.
Configuring Firewalls for IoT Devices
When configuring firewalls for IoT devices, it is important to define specific rules that allow only necessary traffic to pass through. This includes restricting access to certain ports and IP addresses, as well as implementing intrusion detection and prevention systems (IDPS).
Authentication Protocols for IoT
Authentication is the process of verifying the identity of users and devices. In IoT applications, strong authentication protocols are essential to ensure that only authorized devices and users can access the network. This section will cover some of the most widely used authentication protocols for IoT devices.
OAuth 2.0
OAuth 2.0 is an authorization framework that allows third-party applications to access user data without exposing their credentials. It is widely used in IoT applications to provide secure access to cloud-based services.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access to the network. This method is highly effective in preventing unauthorized access to IoT devices and networks.
Best Practices for IoT Security
To ensure the security of your IoT VPC infrastructure, it is important to follow best practices. These practices include regularly updating firmware and software, implementing strong password policies, and monitoring network activity for suspicious behavior. In this section, we will outline some of the key best practices for securing IoT devices.
Regular Firmware Updates
Regularly updating firmware and software is essential for addressing security vulnerabilities and ensuring optimal performance. Manufacturers frequently release updates to fix bugs and improve security, so it is important to keep your devices up to date.
Network Segmentation
Network segmentation involves dividing your network into smaller, isolated segments. This approach minimizes the attack surface and limits the potential impact of a security breach. By segmenting your IoT devices, you can better control access and monitor network traffic.
Troubleshooting Common IoT Security Issues
Despite following best practices, IoT security issues can still arise. In this section, we will discuss some common IoT security challenges and provide solutions for addressing them.
Unauthorized Access
Unauthorized access is one of the most common IoT security issues. To prevent this, ensure that all devices and users are properly authenticated and that access controls are configured correctly. Regularly review access logs and monitor network activity for any suspicious behavior.
Data Breaches
Data breaches can occur when sensitive information is exposed due to weak encryption or improper data handling. To mitigate this risk, use strong encryption protocols and implement strict data handling policies. Regularly audit your systems to identify and address any potential vulnerabilities.
Conclusion and Next Steps
In conclusion, securely connect remote IoT VPC Raspberry Pi is a critical aspect of modern IoT infrastructure. By implementing robust security measures such as encryption, authentication, and network segmentation, you can protect your devices and data from unauthorized access and cyberattacks. This guide has provided you with actionable insights and practical steps to enhance the security of your IoT environment.
We encourage you to take the next step by implementing the techniques discussed in this article. Share your experiences and feedback in the comments section below, and don't forget to explore other articles on our website for more information on IoT security and related topics.
References:
- https://www.cisco.com/c/en/us/solutions/internet-of-things/secure-iot.html
- https://docs.aws.amazon.com/vpc/latest/userguide/
- https://www.raspberrypi.org/documentation/