In the rapidly evolving world of IoT (Internet of Things), accessing IoT devices remotely using SSH (Secure Shell) has become an essential skill for developers and administrators alike. Whether you're managing smart home devices, industrial sensors, or cloud-connected gadgets, SSH offers a secure and reliable way to interact with your IoT devices without compromising on security.
As the number of connected devices grows exponentially, so does the need for efficient and secure remote access solutions. This guide will walk you through everything you need to know about accessing IoT devices via SSH for free, ensuring you can manage your devices safely and effectively.
By the end of this article, you'll have a comprehensive understanding of SSH, its benefits, potential risks, and step-by-step instructions to set up and secure your IoT device connections. Let's dive in!
Read also:Unveiling The Mysteries Of The April Element Sign A Comprehensive Guide
Table of Contents
- Introduction to IoT Device SSH Access
- What is SSH and Why Use It?
- Setting Up Your IoT Device for SSH
- Free SSH Solutions for IoT Devices
- Security Best Practices for IoT SSH Access
- Troubleshooting Common Issues
- Alternatives to SSH for IoT Devices
- Performance Tips for SSH Connections
- Real-World Use Cases for IoT SSH
- Conclusion and Next Steps
Introduction to IoT Device SSH Access
IoT devices are revolutionizing how we interact with technology, enabling seamless connectivity across various industries. However, managing these devices remotely requires secure and efficient tools. SSH is one such tool that provides encrypted communication between devices, ensuring data remains protected during transmission.
Accessing IoT devices via SSH offers numerous advantages, including:
- Encrypted communication
- Secure authentication
- Remote command execution
- Platform independence
For individuals and organizations looking to manage IoT devices without incurring additional costs, free SSH solutions provide an excellent alternative to paid services. In this section, we'll explore the basics of SSH and its significance in the IoT ecosystem.
What is SSH and Why Use It?
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over unsecured networks. It encrypts all data transmitted between devices, making it an ideal choice for managing IoT devices remotely.
Key Features of SSH
SSH offers several features that make it a preferred choice for remote access:
- Data encryption
- Public key authentication
- Support for multiple commands
- File transfer capabilities
According to a report by Cybersecurity Ventures, the global cost of cybercrime is expected to reach $10.5 trillion annually by 2025. Using SSH for IoT device management significantly reduces the risk of unauthorized access and data breaches, making it a critical component of modern cybersecurity strategies.
Read also:Tamil Aunty The Heart And Soul Of South Indian Culture
Setting Up Your IoT Device for SSH
Before you can access your IoT device via SSH, you need to ensure it's properly configured. This involves installing the necessary software, setting up authentication methods, and configuring network settings.
Step-by-Step Guide to IoT Device SSH Setup
Follow these steps to prepare your IoT device for SSH access:
- Install an SSH server on your IoT device
- Configure network settings to allow remote connections
- Set up user authentication using passwords or public keys
- Test the connection using an SSH client
For example, if you're using a Raspberry Pi as your IoT device, you can enable SSH by running the following command:
sudo systemctl enable ssh
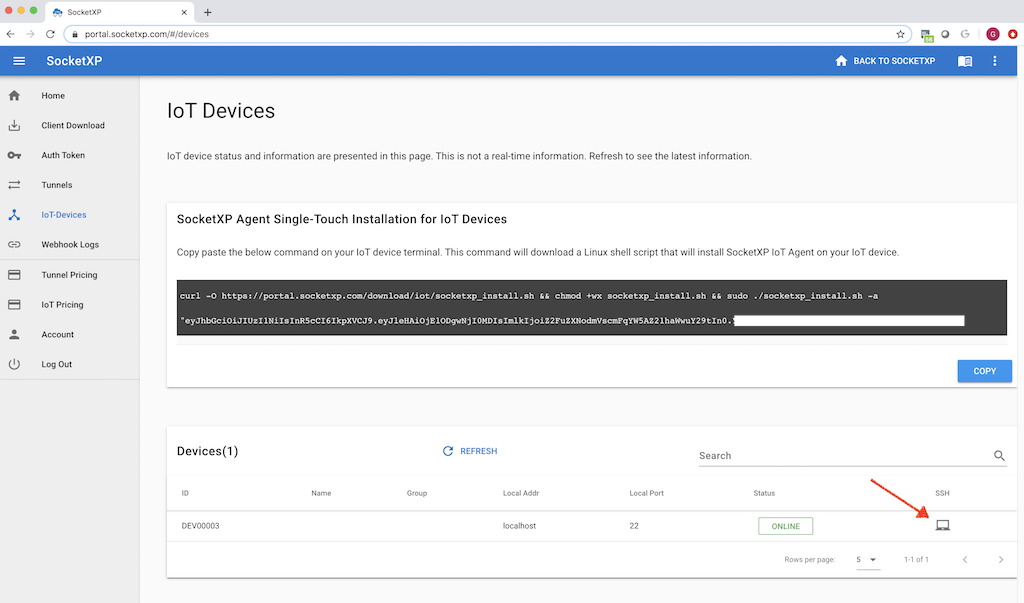
Free SSH Solutions for IoT Devices
Several free SSH solutions are available for managing IoT devices. These tools provide robust features without requiring any financial investment, making them ideal for hobbyists and small-scale projects.
Popular Free SSH Clients
- PuTTY (Windows)
- OpenSSH (Linux/Mac)
- Termius (Cross-platform)
- Mobaxterm (Windows)
When choosing an SSH client, consider factors such as platform compatibility, ease of use, and feature set. For instance, OpenSSH is widely regarded as one of the most reliable and secure SSH clients available, making it a popular choice among developers.
Security Best Practices for IoT SSH Access
While SSH provides a secure method for accessing IoT devices, it's essential to follow best practices to minimize potential risks. Implementing strong security measures ensures your devices remain protected from unauthorized access.
Tips for Securing Your SSH Connections
- Use strong, unique passwords
- Enable public key authentication
- Disable password authentication
- Restrict access to specific IP addresses
- Regularly update SSH software
A study conducted by the Ponemon Institute found that 60% of data breaches are caused by weak or stolen credentials. By following these security guidelines, you can significantly reduce the likelihood of your IoT devices being compromised.
Troubleshooting Common Issues
Even with proper configuration, issues may arise when accessing IoT devices via SSH. Common problems include connection timeouts, authentication failures, and network configuration errors.
Solutions to Common SSH Issues
- Check firewall settings to ensure SSH traffic is allowed
- Verify the correctness of IP addresses and port numbers
- Ensure the SSH server is running on the IoT device
- Test the connection using different SSH clients
If you encounter persistent issues, consult the documentation for your specific SSH client or seek assistance from online forums and communities dedicated to IoT and SSH topics.
Alternatives to SSH for IoT Devices
While SSH is a widely used and trusted method for remote access, alternative solutions exist that may better suit certain use cases. These include:
Popular SSH Alternatives
- Web-based interfaces
- MQTT (Message Queuing Telemetry Transport)
- CoAP (Constrained Application Protocol)
- HTTP/HTTPS APIs
Each alternative has its own set of advantages and disadvantages, so it's important to evaluate your specific requirements before selecting a solution. For example, MQTT is well-suited for low-bandwidth environments, while HTTP/HTTPS APIs offer greater flexibility for web-based applications.
Performance Tips for SSH Connections
Optimizing SSH performance can enhance the user experience and improve overall system efficiency. Here are some tips to boost your SSH connection speed:
Enhancing SSH Performance
- Compress data using SSH compression
- Use faster encryption algorithms
- Limit the number of simultaneous connections
- Optimize network settings
Implementing these performance improvements can lead to faster connection times and more responsive interactions with your IoT devices.
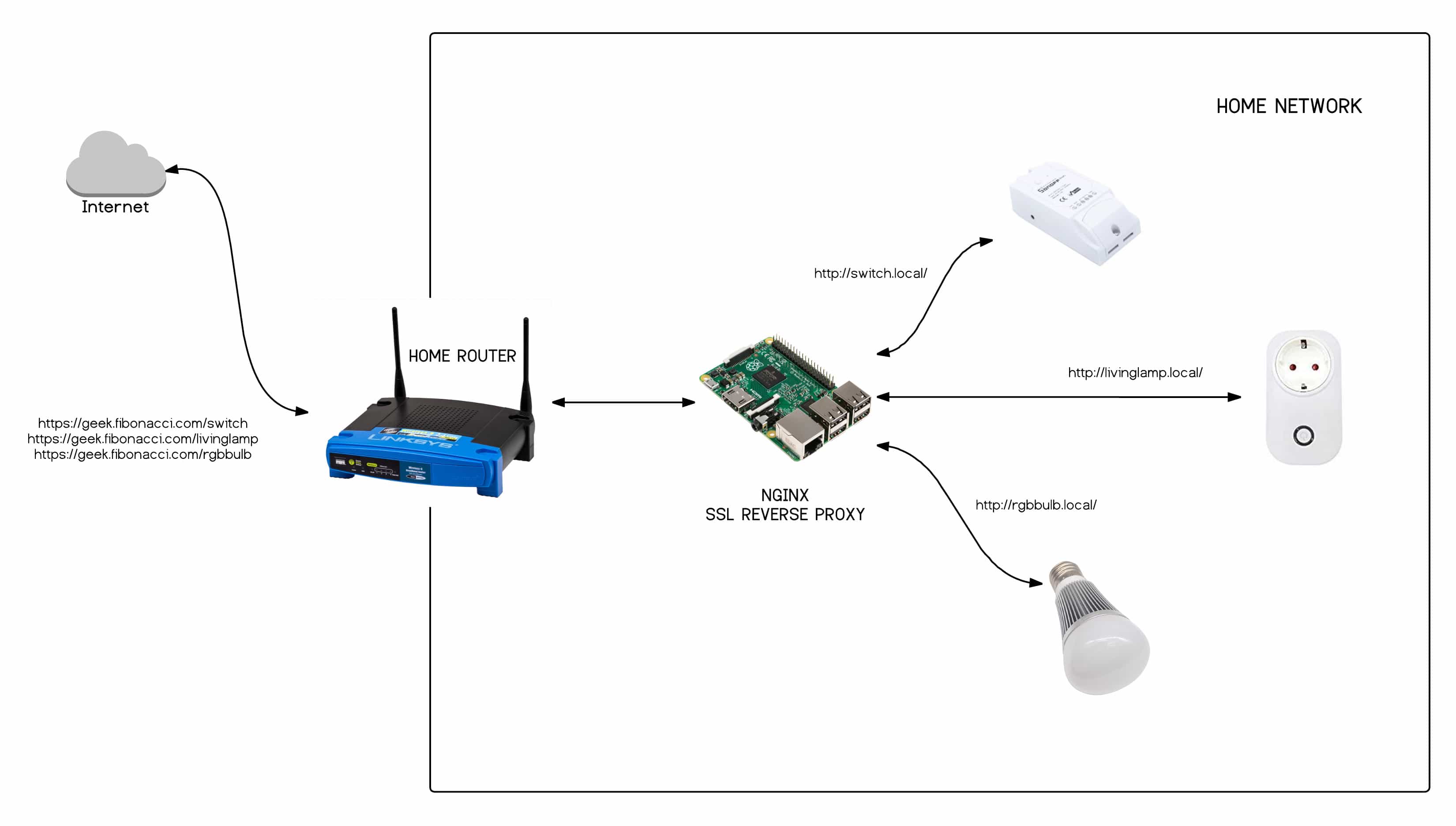
Real-World Use Cases for IoT SSH
SSH is utilized in various real-world scenarios to manage and monitor IoT devices effectively. Some common use cases include:
Examples of IoT SSH Applications
- Remote monitoring of industrial equipment
- Managing smart home devices
- Configuring network-connected sensors
- Updating firmware on remote devices
These use cases demonstrate the versatility and importance of SSH in the IoT landscape, providing a secure and reliable method for interacting with connected devices.
Conclusion and Next Steps
Accessing IoT devices via SSH offers a secure and efficient way to manage your connected devices remotely. By following the guidelines outlined in this article, you can set up and secure your SSH connections effectively, ensuring your devices remain protected from potential threats.
We encourage you to explore the various SSH clients and tools available, experimenting with different configurations to find the best solution for your specific needs. Additionally, consider sharing your experiences and insights with the community to help others learn and grow.
Feel free to leave a comment below or explore our other articles for more information on IoT and cybersecurity topics. Together, we can build a safer and more connected world!